Author: Denis Avetisyan
A new processor design, CryptRISC, integrates cryptographic acceleration with advanced masking techniques to deliver robust security against side-channel attacks.
CryptRISC is a RISC-V processor featuring field-aware masking for high-performance, power-analysis resistant cryptography.
While cryptographic algorithms are essential for modern security, their implementations remain vulnerable to power side-channel attacks that leak sensitive information through power consumption variations. This paper introduces ‘CryptRISC: A Secure RISC-V Processor for High-Performance Cryptography with Power Side-Channel Protection’, a novel RISC-V processor that integrates cryptographic acceleration with a hardware-level defense against these attacks via an ISA-driven, field-aware operand masking framework. By dynamically applying optimized Boolean, affine, or arithmetic masking schemes based on instruction semantics, CryptRISC achieves significant performance improvements-up to 6.80\times over software implementations with only a 1.86\% hardware overhead. Could this approach pave the way for more efficient and secure hardware designs for a wider range of cryptographic applications?
The Illusion of Secure Foundations
Despite the robust mathematical foundations of modern cryptographic algorithms such as AES and SM4, practical security frequently hinges on the details of their implementation. These algorithms, designed to transform data into an unreadable format using complex keys, are theoretically impervious to attack; however, the hardware and software executing these algorithms introduce vulnerabilities. A seemingly secure system can be compromised not by breaking the encryption itself, but by exploiting weaknesses in how the encryption is performed. Subtle flaws in code, predictable memory access patterns, or even the physical characteristics of the computing device can be leveraged by attackers to deduce the secret key and decrypt the protected data, rendering the encryption effectively useless. This highlights a crucial distinction: algorithmic security and implementation security are not synonymous, and a strong algorithm does not guarantee a secure system.
Power side-channel attacks represent a significant threat to cryptographic systems by exploiting the physical link between a device’s power consumption and the data it processes. Even when encryption algorithms like AES or SM4 remain mathematically sound, their implementation on hardware isn’t perfect; the act of computation itself requires energy, and that energy usage isn’t constant. Subtle variations in power draw, correlated to the bits being manipulated – a ‘1’ requiring slightly more power than a ‘0’, for example – can be measured and analyzed. Sophisticated statistical techniques then allow attackers to deduce the encryption key, effectively bypassing the intended security of the algorithm. This isn’t a flaw in the math, but a vulnerability in how that math is performed on physical hardware, making it a persistent challenge for device security.
Securing cryptographic implementations against side-channel attacks frequently demands trade-offs in computational efficiency. While techniques like masking, hiding, and algorithmic modifications can mitigate information leakage, they often introduce substantial performance overhead. This overhead stems from the increased complexity of operations – for example, performing multiple calculations with randomized data in masking, or adding dummy operations to obscure power consumption patterns. Consequently, developers face a critical dilemma: bolstering security can significantly slow down applications, impacting usability and potentially rendering systems impractical for resource-constrained environments like mobile devices or embedded systems. The challenge lies in devising countermeasures that minimize this performance penalty while still providing robust protection against increasingly sophisticated side-channel analysis techniques, necessitating ongoing research into lightweight and efficient security solutions.

A Calculated Defense: CryptRISC
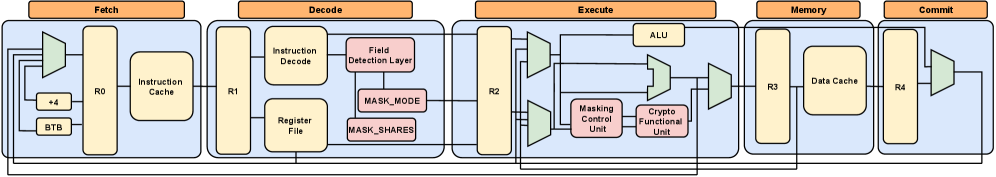
CryptRISC is a reduced instruction set computing (RISC-V) processor architecture engineered to defend against power side-channel attacks. This is achieved through the integration of dedicated cryptographic acceleration hardware and advanced masking techniques. The processor implements both software and hardware countermeasures, aiming to minimize information leakage through power consumption variations during cryptographic operations. By combining optimized cryptographic primitives with masking, CryptRISC obscures the relationship between the processed data and the resulting power trace, thereby significantly increasing the difficulty of extracting sensitive information through side-channel analysis. The design prioritizes performance alongside security, leveraging the inherent efficiency of the RISC-V instruction set.
CryptRISC builds upon the open-source RISC-V instruction set architecture (ISA), providing compatibility with existing RISC-V software and tools. This foundation is extended through the addition of custom instructions tailored for cryptographic operations and the integration of dedicated hardware accelerators. These accelerators, implemented as co-processors, offload computationally intensive tasks such as AES encryption, SHA-256 hashing, and elliptic curve cryptography from the core processor. The modular design allows for the addition of further specialized modules as needed, facilitating adaptability to evolving security standards and algorithms, while maintaining compatibility with the broader RISC-V ecosystem.
The Field Detection Layer (FDL) within CryptRISC functions by analyzing each computational operation to determine the underlying algebraic field – typically GF(2) for Boolean operations or larger finite fields for arithmetic. This dynamic field identification is crucial because the optimal masking strategy-Boolean Masking, Arithmetic Masking, or a hybrid approach-is field-dependent. By accurately detecting the field, the FDL enables the Masking Control Unit (MCU) to apply the most effective masking technique, minimizing the information leakage through side channels and maximizing security without unnecessary performance overhead. The FDL utilizes a combination of opcode analysis and dataflow tracking to reliably identify the field for each operation, even within complex computational sequences.
The Masking Control Unit (MCU) implements data transformation techniques to protect against side-channel analysis by concealing intermediate values during cryptographic operations. Based on field detection, the MCU applies either Boolean Masking or Arithmetic Masking. Boolean Masking operates on bit-level representations, XORing operands with random masks to obscure the original data. Arithmetic Masking, conversely, functions on values within the detected field, adding random field elements to the operands. Both techniques introduce randomness, ensuring that the power consumption or electromagnetic emissions do not correlate directly with the sensitive data being processed, thereby hindering attempts to extract secret keys through side-channel attacks. The MCU is designed to securely manage the masks and perform these transformations with minimal performance overhead.

Validating Resilience: Empirical Evidence
CryptRISC achieves significant acceleration of cryptographic computations by leveraging the CVA6 processor core and incorporating hardware-level security features. Performance benchmarks demonstrate a speedup of up to 6.80x when compared to equivalent software-based implementations of cryptographic algorithms. This improvement is a direct result of dedicated hardware acceleration and optimizations within the CryptRISC architecture, allowing for faster execution of critical cryptographic operations while simultaneously mitigating the risk of side-channel attacks. The design prioritizes both speed and security, offering a substantial performance boost without compromising data confidentiality.
Test Vector Leakage Assessment (TVLA) is employed as a primary method for quantifying the side-channel resistance of the CryptRISC processor. This statistical analysis technique involves subjecting the processor to a comprehensive suite of cryptographic operations with known inputs and measuring potential information leakage through physical characteristics like power consumption or electromagnetic emissions. TVLA operates by correlating these measured leakages with the processed data, identifying any statistically significant dependencies that could reveal sensitive information. The methodology utilizes a large number of test vectors to ensure a high degree of confidence in the results, and generates a t-value for each tested variable, indicating the strength of any detected correlation; lower t-values indicate less leakage and greater security.
Test Vector Leakage Assessment (TVLA) was employed to validate the effectiveness of field-aware masking within the CryptRISC processor against side-channel attacks. TVLA analysis resulted in t-values consistently remaining within the ±2 range across all tests. This indicates that no statistically significant first-order leakage was detected, confirming the masking implementation successfully suppresses information leakage that could be exploited to compromise cryptographic keys. The established thresholds for statistical significance were met, demonstrating a robust level of security against first-order side-channel analysis.
The CryptRISC processor validates its cryptographic capabilities by supporting both internationally recognized algorithms – AES, SHA-256, and SHA-512 – and Chinese national standards, specifically SM3 and SM4. This broad algorithmic support is achieved with minimal impact on hardware resources; implementation results demonstrate an increase of only 1.86% in Look-Up Tables (LUTs) and 0.24% in Flip-Flops, indicating a highly efficient design that balances functionality and area overhead.

A Paradigm Shift in Secure Computation
CryptRISC signifies a fundamental departure in hardware security by pioneering field-aware masking-a technique that moves beyond the traditional, one-size-fits-all approach to cryptographic countermeasures. Previous hardware security implementations often relied on generic defenses against side-channel attacks, which could be computationally expensive and lacked adaptability. In contrast, field-aware masking tailors security measures to the specific characteristics of the underlying hardware and the cryptographic operations being performed. This targeted approach dramatically reduces the performance overhead typically associated with robust security, while simultaneously increasing resistance to sophisticated attacks.
The advent of CryptRISC and its field-aware masking techniques promises a significant impact across diverse computing landscapes. For resource-constrained environments like embedded systems and the burgeoning Internet of Things, this approach offers heightened security without sacrificing performance – a critical need for protecting sensitive data collected by these devices. Scaling upwards, data centers and cloud computing infrastructures stand to benefit from the reduced overhead and increased efficiency, translating to lower energy consumption and improved throughput while safeguarding vast amounts of user data. This adaptability positions CryptRISC not merely as a security enhancement, but as a foundational element for building trust and resilience into the next generation of computing systems, fostering secure data handling from the smallest sensor to the largest server farm.
CryptRISC distinguishes itself through a fundamental design principle: the seamless integration of security mechanisms directly within the processor’s architecture. Traditional cryptographic implementations often rely on software-based solutions or add-on hardware, introducing significant performance penalties and energy consumption. By building security into the core processing unit, CryptRISC circumvents these limitations, dramatically reducing overhead and maximizing computational efficiency. This allows cryptographic operations to execute with speeds comparable to standard, non-encrypted calculations, a critical advantage for resource-constrained devices and high-throughput applications. The result is a system where security isn’t an afterthought, but rather an inherent and optimized component of the processor’s functionality, paving the way for consistently secure and efficient computing.
Ongoing research endeavors are dedicated to broadening the scope of field-aware masking techniques beyond current implementations, aiming to encompass a more diverse array of cryptographic algorithms and enhance security protocols. This expansion isn’t merely about increasing algorithm support; it involves a proactive investigation into novel countermeasures against increasingly sophisticated side-channel attacks, including those leveraging machine learning and fault injection. Future developments will concentrate on optimizing masking schemes for performance and area efficiency, as well as exploring hybrid approaches that combine field-aware masking with other security mechanisms to create robust and resilient cryptographic systems. The ultimate goal is to establish a proactive security posture capable of anticipating and neutralizing emerging threats in the ever-evolving landscape of secure computing.

The development of CryptRISC exemplifies a fundamental truth regarding complex systems. It isn’t simply a construction, but an evolving response to inherent vulnerabilities. The processor’s integration of cryptographic acceleration alongside field-aware masking isn’t about achieving flawless security, but rather about building in resilience against inevitable breaches. As Donald Davies observed, “A system that never breaks is dead.” CryptRISC doesn’t promise invulnerability to power side-channel attacks; it anticipates them, embedding layers of defense that allow the system to degrade gracefully-and continue functioning-even under duress. This approach acknowledges that perfection, in the realm of hardware security, leaves no room for people-or, more accurately, no room for adaptation and improvement in the face of constantly evolving threats.
What Lies Ahead?
CryptRISC, in its focused acceleration of cryptographic primitives, reveals a familiar pattern. The system addresses a known vulnerability-power analysis-with a technically elegant solution. Yet, it simultaneously propagates a deeper dependency. Each layer of masking, each optimization for performance, introduces further complexity, and thus, new vectors for future compromise. The landscape of attacks does not remain static; defenses merely raise the cost of breach, encouraging more sophisticated adversaries. The system doesn’t prevent failure, it delays and reshapes it.
The emphasis on field-aware masking is noteworthy, suggesting a recognition that security isn’t uniform. However, this specialization implies a limited scope. A processor optimized for these cryptographic algorithms will, inevitably, be less secure against unforeseen algorithms or attacks. The architecture, in its very design, encodes a prediction about the future threat model-a prediction destined to be inaccurate. The next phase will likely involve architectures that embrace, rather than resist, adaptability, perhaps leaning toward reconfigurable hardware or formal verification techniques that can encompass a broader range of potential vulnerabilities.
Ultimately, the pursuit of hardware security resembles a game of asymptotic approach. Each iteration brings diminishing returns. The challenge isn’t to build an impenetrable fortress, but to cultivate a resilient ecosystem-one capable of absorbing shocks and evolving in response to inevitable compromise. The processor does not solve the problem of trust; it merely shifts the boundary of what must be trusted.
Original article: https://arxiv.org/pdf/2602.20285.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- All Skyblazer Armor Locations in Crimson Desert
- Robinhood’s $75M OpenAI Bet: Retail Access or Legal Minefield?
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- How to Catch All Itzaland Bugs in Infinity Nikki
- Speedsters Sandbox Roblox Codes
- Who Can You Romance In GreedFall 2: The Dying World?
- Top 10 Must-Watch Isekai Anime on Crunchyroll Revealed!
- Invincible: 10 Strongest Viltrumites in Season 4, Ranked
- Re:Zero Season 4 Episode 3 Release Date & Where to Watch
- USD CNY PREDICTION
2026-02-25 11:55