Author: Denis Avetisyan
A rigorous analysis of the LINE protocol reveals critical vulnerabilities, prompting the development of a fortified version with enhanced forward secrecy.
This review details a comprehensive cryptographic assessment of the LINE end-to-end encryption protocol and proposes LINEvDR, an improved design leveraging a double ratchet mechanism for enhanced security.
While widely adopted, the security of end-to-end encrypted messaging platforms often relies on assumptions rather than rigorous analysis. This is addressed in ‘Drawing the LINE: Cryptographic Analysis and Security Improvements for the LINE E2EE Protocol’, which presents the first provable security evaluation of the LINE messaging protocol, revealing a lack of forward secrecy and post-compromise security in its original design. To remedy these vulnerabilities, the authors introduce LINEvDR, an enhanced protocol incorporating a double ratchet mechanism to bolster cryptographic guarantees. Will these improvements be sufficient to address emerging threats and ensure long-term user privacy in increasingly sophisticated communication environments?
The Evolving Landscape of Secure Communication
The LINE messaging platform, boasting hundreds of millions of users globally, has historically operated with a surprising lack of comprehensive, peer-reviewed security assessments. While widely adopted for its convenience and feature set, this limited formal scrutiny created a potential landscape for undiscovered vulnerabilities. Unlike some other prominent messaging applications subjected to intense cryptographic examination, LINE’s protocol remained largely unanalyzed for extended periods. This absence of independent verification meant potential weaknesses in its encryption schemes, authentication mechanisms, or key management practices could have gone unnoticed, potentially exposing user communications to interception or manipulation – a risk amplified by the platform’s prevalence in regions with varying levels of digital security infrastructure and governmental oversight.
Initial iterations of the LINE messaging platform’s encryption scheme depended on the Letter Sealing Protocol coupled with a static-static Diffie-Hellman key exchange. While providing a baseline level of End-to-End Encryption, this approach presented a significant security limitation: a lack of forward secrecy. Because the same key pair was used for every session, compromise of these long-term keys – through phishing, malware, or server breaches – would retroactively decrypt all past communications. This meant that even if the platform improved its security practices later, previously exchanged messages remained vulnerable, highlighting a critical design flaw in earlier versions of the application and underscoring the importance of regularly updated cryptographic protocols.
The initial security architecture of LINE messaging, while successfully implementing end-to-end encryption, presented a significant vulnerability regarding long-term key management. Early iterations of the protocol relied on static Diffie-Hellman key exchange, meaning that if a long-term private key was ever compromised – through malware, phishing, or a server breach – all past, present, and future messages could be decrypted. This contrasts with protocols employing forward secrecy, where compromise of a long-term key only affects current and future sessions, leaving past communications secure. A recent analysis meticulously examined these early designs, revealing the extent of this susceptibility and highlighting the critical need for more robust key exchange mechanisms to protect user privacy and maintain the integrity of the platform against both current and future threats.
Introducing LINEvDR: A Foundation for Robust Security
LINEvDR is a redesigned encryption protocol superseding the original LINE messaging protocol, addressing identified vulnerabilities and scalability issues present in the earlier implementation. The initial protocol lacked robust forward and post-compromise security, relying on long-term static keys which, if compromised, would expose past and future message content. LINEvDR introduces a dynamic key exchange system to mitigate these risks, enabling more frequent key updates and limiting the exposure window in the event of a key compromise. This evolution prioritizes enhanced security without sacrificing usability for the platform’s extensive user base.
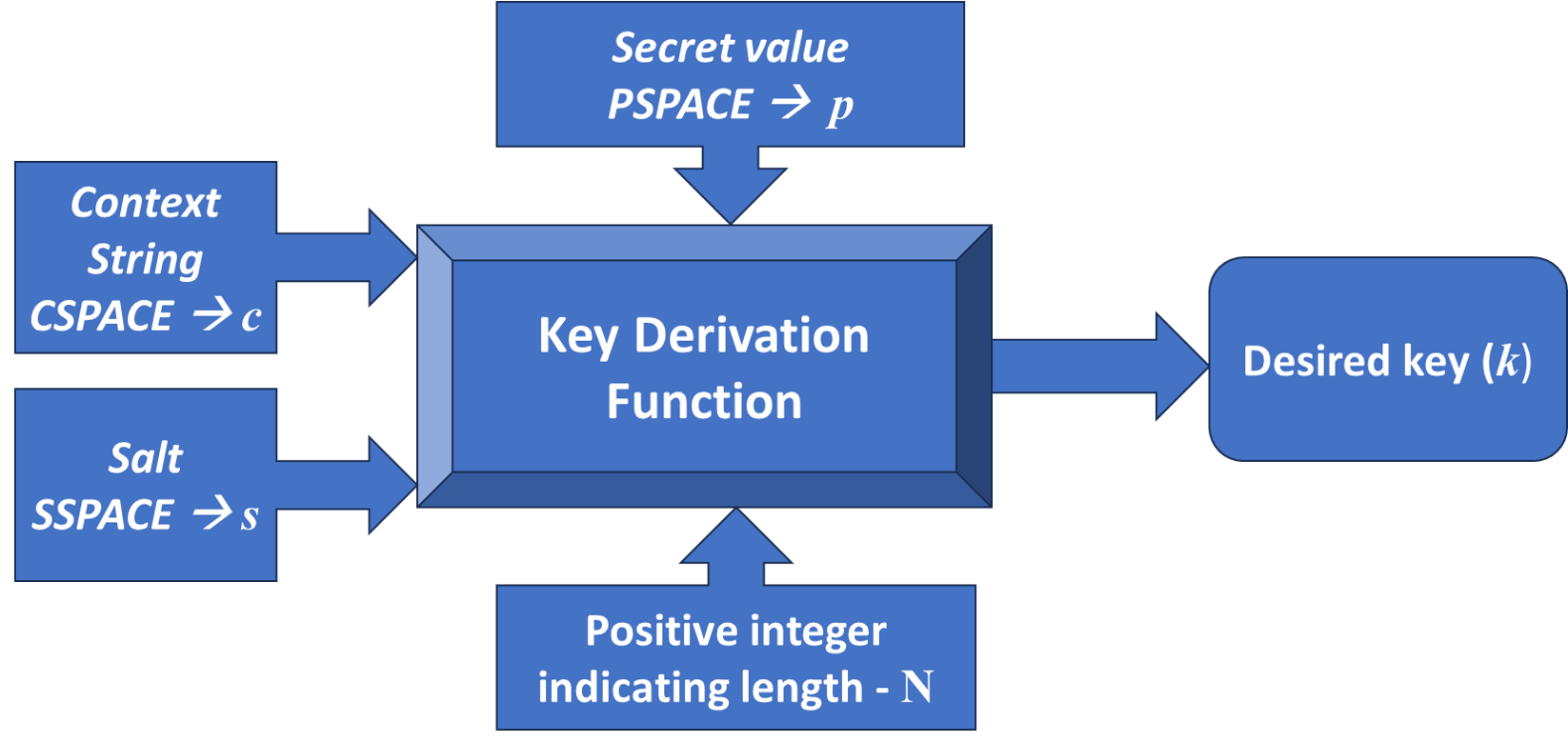
The Double Ratchet Mechanism is a cryptographic ratchet that generates a unique encryption key for each message exchanged. This is achieved through the iterative derivation of new keys from a combination of Root Keys – long-term, static keys – and Chain Keys, which are updated with each message. The mechanism employs two independent ratchets – one for sender and one for receiver – ensuring that compromise of past session keys does not impact future communications, providing forward secrecy. Furthermore, the continuous key derivation limits the scope of potential compromise, enabling post-compromise security by invalidating compromised keys with subsequent ratchets, as formally verified through our analysis.
The LINEvDR protocol employs a hierarchical key management system utilizing both Root Keys and Chain Keys to establish and maintain secure communication. Root Keys serve as long-term identifiers, initially used to derive Chain Keys. Each message exchanged then generates a new, unique key based on the current Chain Key and a message-specific nonce. This continuous derivation of new keys, known as the Double Ratchet Mechanism, ensures that even if a specific Chain Key is compromised, only a limited number of past and future messages are affected. The frequent key rotation effectively minimizes the scope of any potential key compromise and provides forward and post-compromise security by limiting the amount of ciphertext decryptable with a compromised key.
Cryptographic Underpinnings: Ensuring Integrity and Confidentiality
LINEvDR employs Advanced Encryption Standard – Galois/Counter Mode (AES-GCM) as its primary authenticated encryption algorithm. AES-GCM operates in a symmetric-key manner, utilizing a single key for both encryption and decryption processes. Confidentiality is achieved through AES’s block cipher functionality, while integrity and authenticity are guaranteed by the Galois Message Authentication Code (GMAC) component of GCM, which generates a tag based on the ciphertext and associated data. This combined approach ensures that any modification to the message during transmission will be detectable, and that the recipient can verify both the message’s origin and its unaltered content. The algorithm operates on 128-bit blocks with key sizes of 128, 192, or 256 bits, offering configurable security levels.
Message authentication within LINEvDR relies on cryptographic techniques to verify both the authenticity and integrity of transmitted data. This process extends beyond simple message verification by incorporating Associated Data (AD), which consists of contextual information accompanying the message but not directly encrypted. The AD, such as sender identifiers and message metadata, is included in the authentication calculation, ensuring that any tampering with this data-even if it doesn’t alter the encrypted message content-will be detectable. This enhancement prevents attacks where a malicious actor modifies contextual information to impersonate a sender or manipulate message properties, bolstering the protocol’s security against various forms of manipulation and forgery.
Key indistinguishability, a fundamental security property within LINEvDR, prevents adversaries from differentiating between a legitimate encryption key and a randomly generated value. This is achieved through cryptographic designs where all valid keys appear statistically equivalent to an attacker, even with access to ciphertexts and potentially associated data. Successful key indistinguishability ensures that an attacker cannot gain information about the key through observation of encrypted communications, thereby protecting the confidentiality and integrity of the system and bolstering the protocol’s resilience against key recovery attacks and unauthorized decryption.
LINE’s Security Posture: A Model for Modern Messaging
The evolution from LINEv2 to LINEvDR represents a deliberate and significant shift in how the messaging platform approaches security. Recognizing the inherent limitations and potential vulnerabilities present in earlier iterations, developers undertook a comprehensive redesign focused on bolstering defenses against increasingly sophisticated cyber threats. This wasn’t simply a patch to existing code; LINEvDR involved a fundamental restructuring of the encryption protocols and data handling procedures. By proactively addressing known weaknesses and implementing advanced cryptographic techniques, the platform not only mitigated existing risks but also established a new benchmark for secure communication. This commitment to anticipating and neutralizing threats positions LINE as a pioneer, encouraging a more robust security posture across the messaging landscape and setting a higher standard for user data protection.
LINE’s security architecture is fundamentally designed to withstand compromise, focusing intently on both forward secrecy and post-compromise security. Forward secrecy ensures that past conversations remain unreadable even if current encryption keys are compromised, protecting the confidentiality of historical data. Critically, LINE extends this protection with post-compromise security, limiting the exposure of future communications should an attacker gain access to a user’s credentials. This dual approach, recently verified through rigorous analysis, establishes a robust defense against sophisticated threats – preventing widespread decryption of messages even in the event of a successful attack, and positioning the platform as a benchmark for secure messaging protocols.
LINE’s dedication to implementing robust cryptographic protocols isn’t simply a matter of bolstering its own defenses; it actively reshapes the landscape of secure messaging. By prioritizing features like forward secrecy and post-compromise security – and openly detailing their implementation – LINE establishes a high-water mark for the industry. This transparency and commitment to best practices encourages competitors and other communication platforms to reassess their own security postures and integrate similar safeguards. The result is a cascading effect, raising the overall standard for user privacy and data protection across the messaging ecosystem, ultimately benefiting all users by driving innovation and fostering a more secure digital environment.
The pursuit of secure communication, as detailed in the analysis of the LINE protocol, necessitates a relentless distillation of complexity. The paper meticulously dissects cryptographic implementations, revealing vulnerabilities born from unnecessary layers. This aligns with a core tenet of efficient design: eliminate the superfluous. Alan Turing observed, “Sometimes people who are unhappy try to blame it on others.” Similarly, security flaws often arise not from fundamental impossibilities, but from the imposition of intricate, and ultimately fragile, systems upon simpler, more robust foundations. The proposed LINEvDR, through the integration of a double ratchet, exemplifies this principle – achieving forward secrecy not through added complexity, but through a refined architecture.
What’s Next?
The refinement of the LINE protocol, as demonstrated by the introduction of LINEvDR, serves as a potent reminder: secure messaging isn’t about accumulating complexity, but about rigorously excising it. The double ratchet, while effective, represents a necessary complication, not an inherent virtue. Future work should not focus on bolting on further cryptographic layers, but on fundamentally simplifying key exchange and session management-seeking designs where post-compromise security emerges as a natural consequence, not a patched-in feature.
A crucial, largely untouched area remains the practical usability of these improvements. Provable security is a beautiful abstraction, but it is rendered meaningless if the resulting protocol is computationally prohibitive for low-resource devices or introduces unacceptable latency. The challenge lies in distilling these theoretical gains into implementations that are not merely secure, but feel secure – responsive, and seamlessly integrated into everyday communication.
Ultimately, the pursuit of perfect security is a fool’s errand. A more honest goal is resilience. Systems will fail, keys will be compromised, implementations will contain flaws. The true measure of a protocol’s success isn’t its resistance to attack, but its ability to gracefully degrade and recover – to minimize the blast radius of inevitable compromise, and to preserve, as much as possible, the fundamental right to private correspondence.
Original article: https://arxiv.org/pdf/2602.18370.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- All Shadow Armor Locations in Crimson Desert
- All Skyblazer Armor Locations in Crimson Desert
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- Marni Laser Helm Location & Upgrade in Crimson Desert
- Best Bows in Crimson Desert
- All Helfryn Armor Locations in Crimson Desert
- All Golden Greed Armor Locations in Crimson Desert
- How to Craft the Elegant Carmine Armor in Crimson Desert
- Wings of Iron Walkthrough in Crimson Desert
- Keeping Large AI Models Connected Through Network Chaos
2026-02-23 18:20