Quantum Kernels Get a Boost from Spectral Encoding
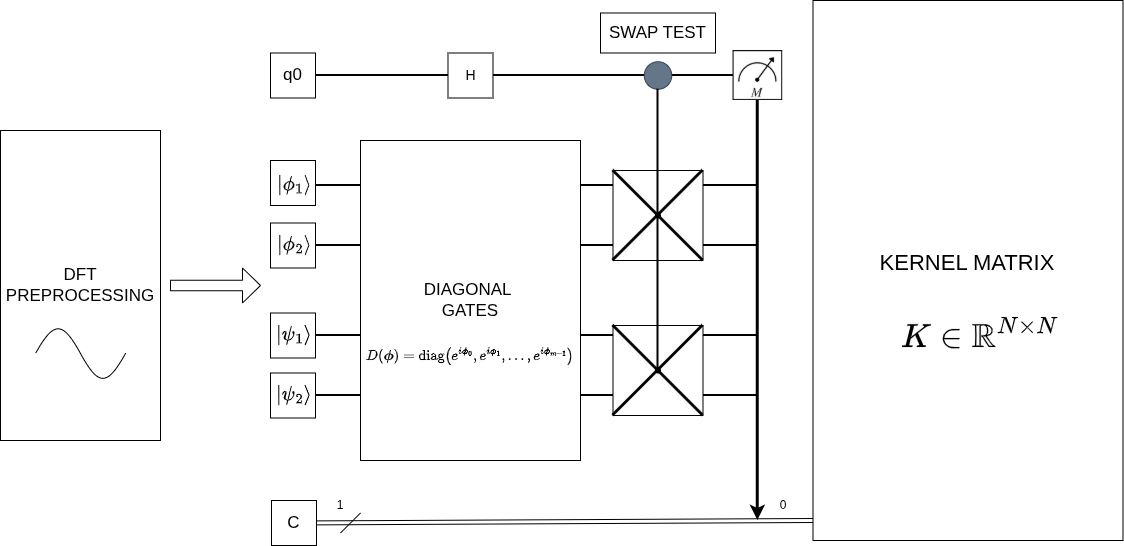
A new approach to constructing quantum kernels using spectral phase encoding demonstrates increased resilience to noise, offering a pathway to more reliable quantum machine learning.
A new approach to constructing quantum kernels using spectral phase encoding demonstrates increased resilience to noise, offering a pathway to more reliable quantum machine learning.
New research explores how quantum algorithms could pose a threat to the Learning Parity with Noise problem, a cornerstone of modern code-based cryptography.
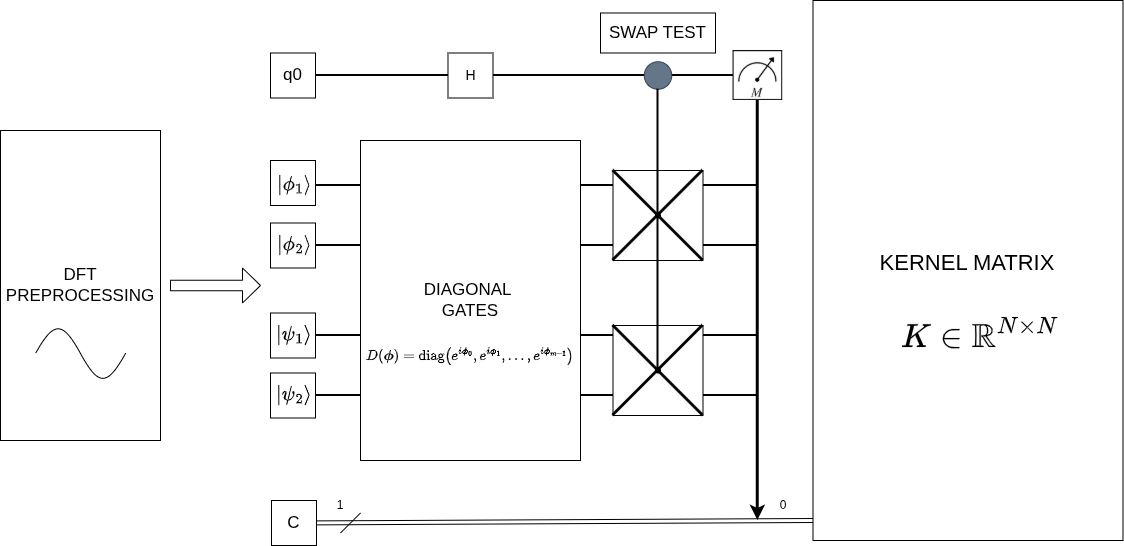
As quantum computing looms, this review explores the practical challenges of integrating post-quantum cryptography into the low-power wireless networks that power our everyday devices.
A new study explores how readily available artificial intelligence tools can assist researchers in analyzing complex qualitative datasets.
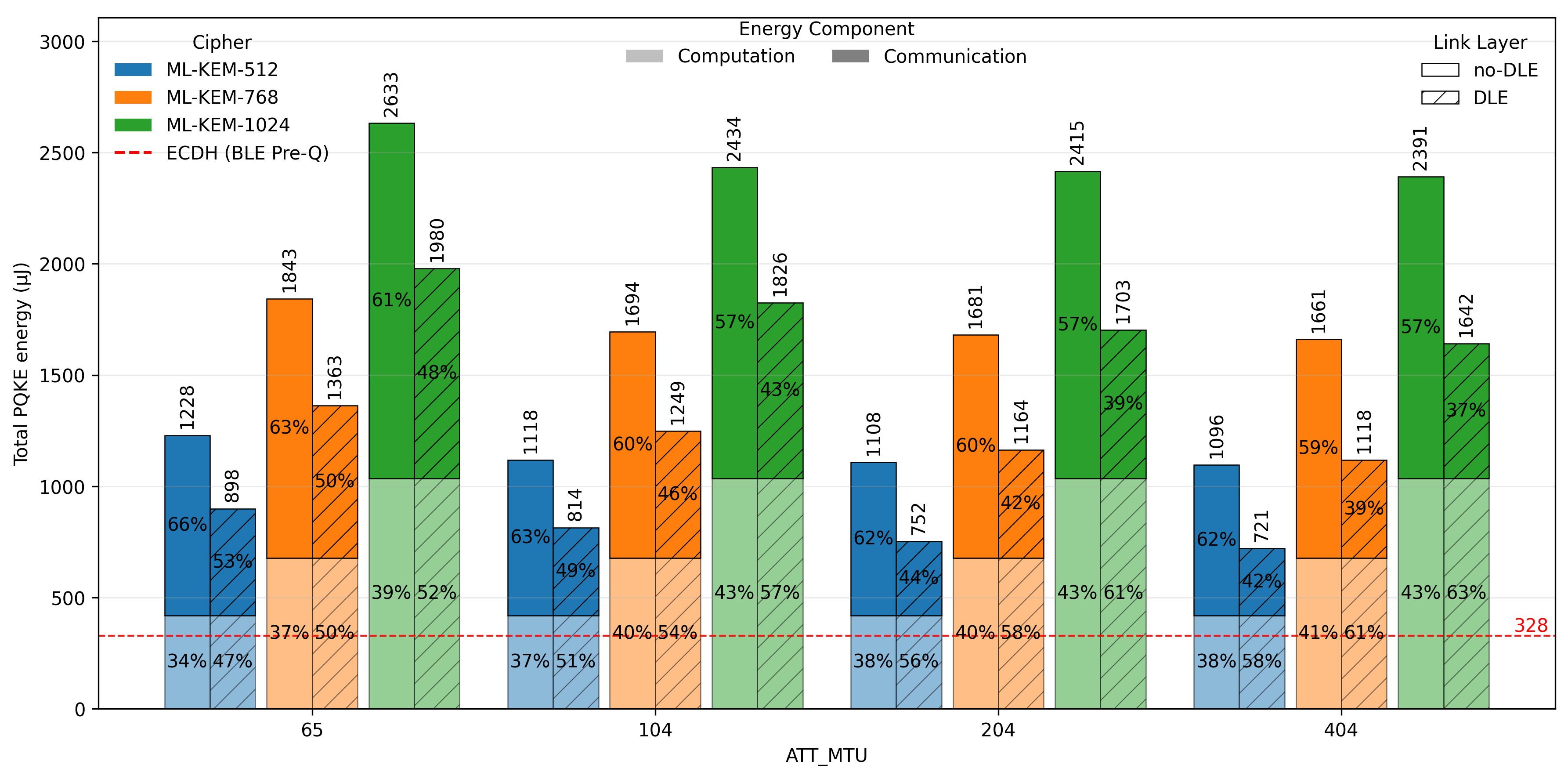
A new framework leverages decentralized learning and privacy-enhancing technologies to build more resilient intrusion detection systems.
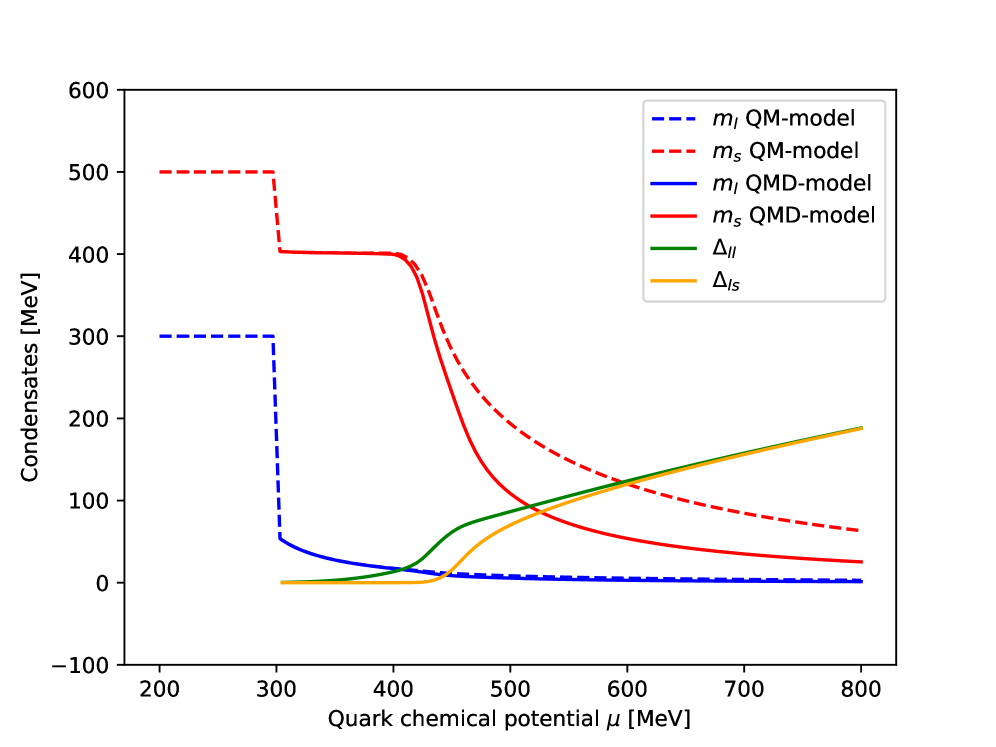
A new theoretical approach investigates the exotic states of matter predicted to exist at the cores of neutron stars and in other environments with extreme densities.
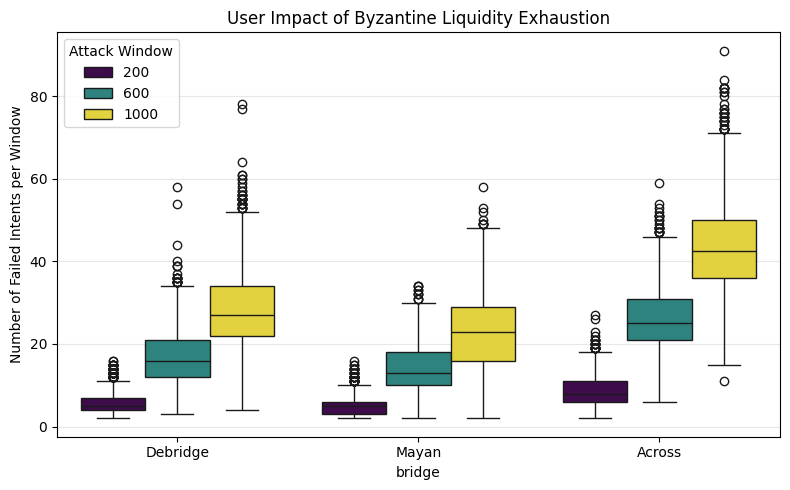
A novel class of ‘liquidity exhaustion’ attacks threatens the security of emerging intent-based cross-chain bridges by exploiting temporary capital shortages.
A new framework, PHAST, leverages the principles of port-Hamiltonian systems to create stable and interpretable models of complex temporal dynamics from limited observations.
A new analysis reveals that fully accounting for light-matter interactions in quantum chemistry requires a fundamental shift in how we apply coherent-state transformations within coupled cluster theory.
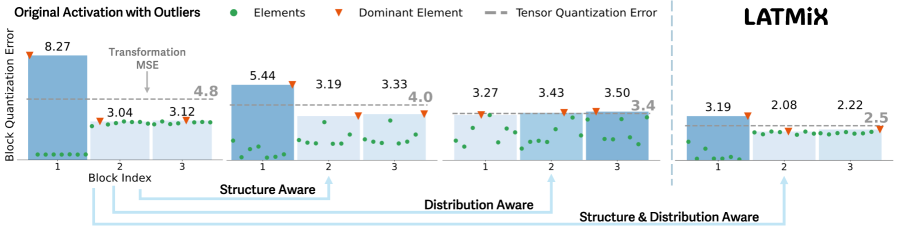
A new quantization technique intelligently reshapes activation distributions to minimize information loss in highly compressed language models.