Beyond Encryption: Securing LINE’s Messaging Future
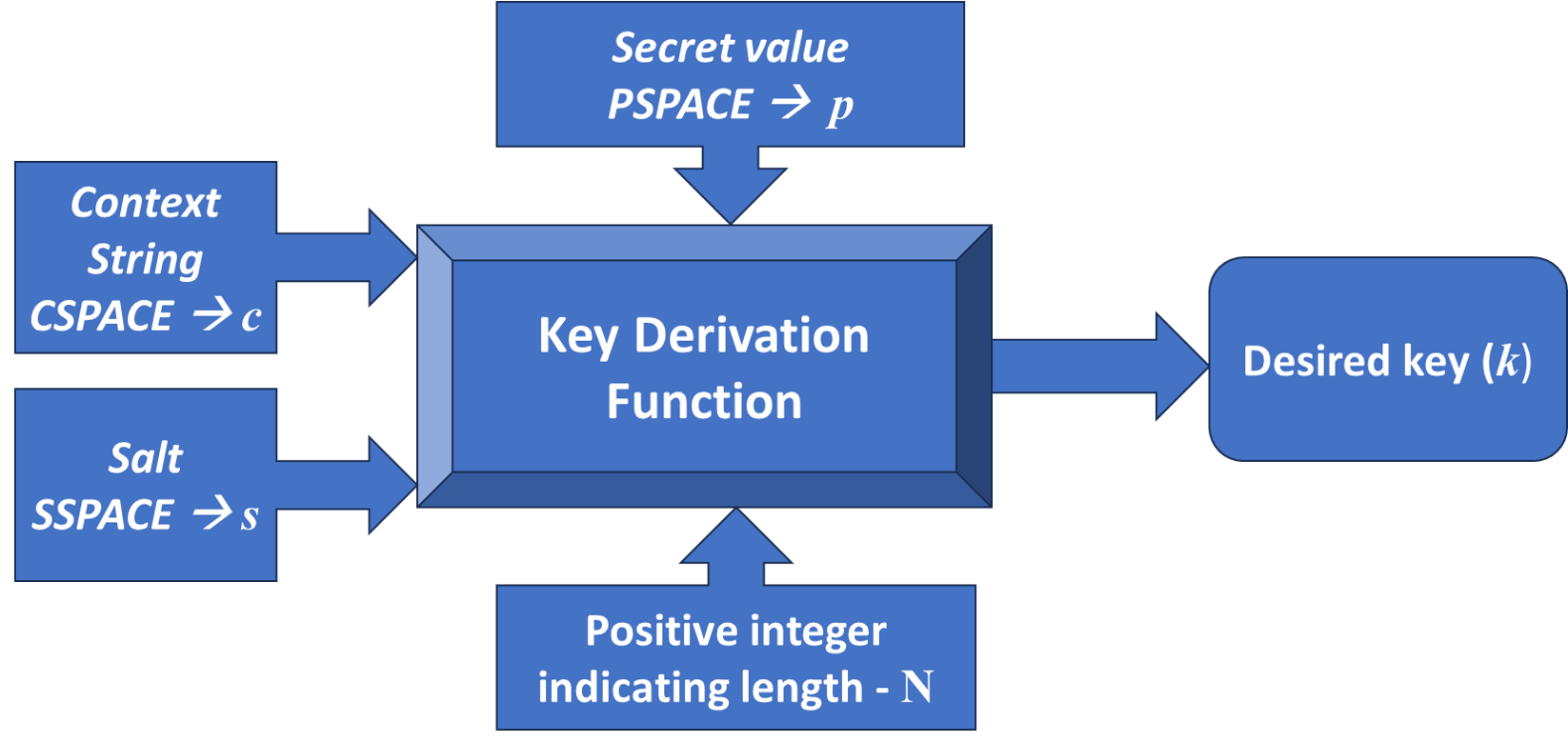
A rigorous analysis of the LINE protocol reveals critical vulnerabilities, prompting the development of a fortified version with enhanced forward secrecy.
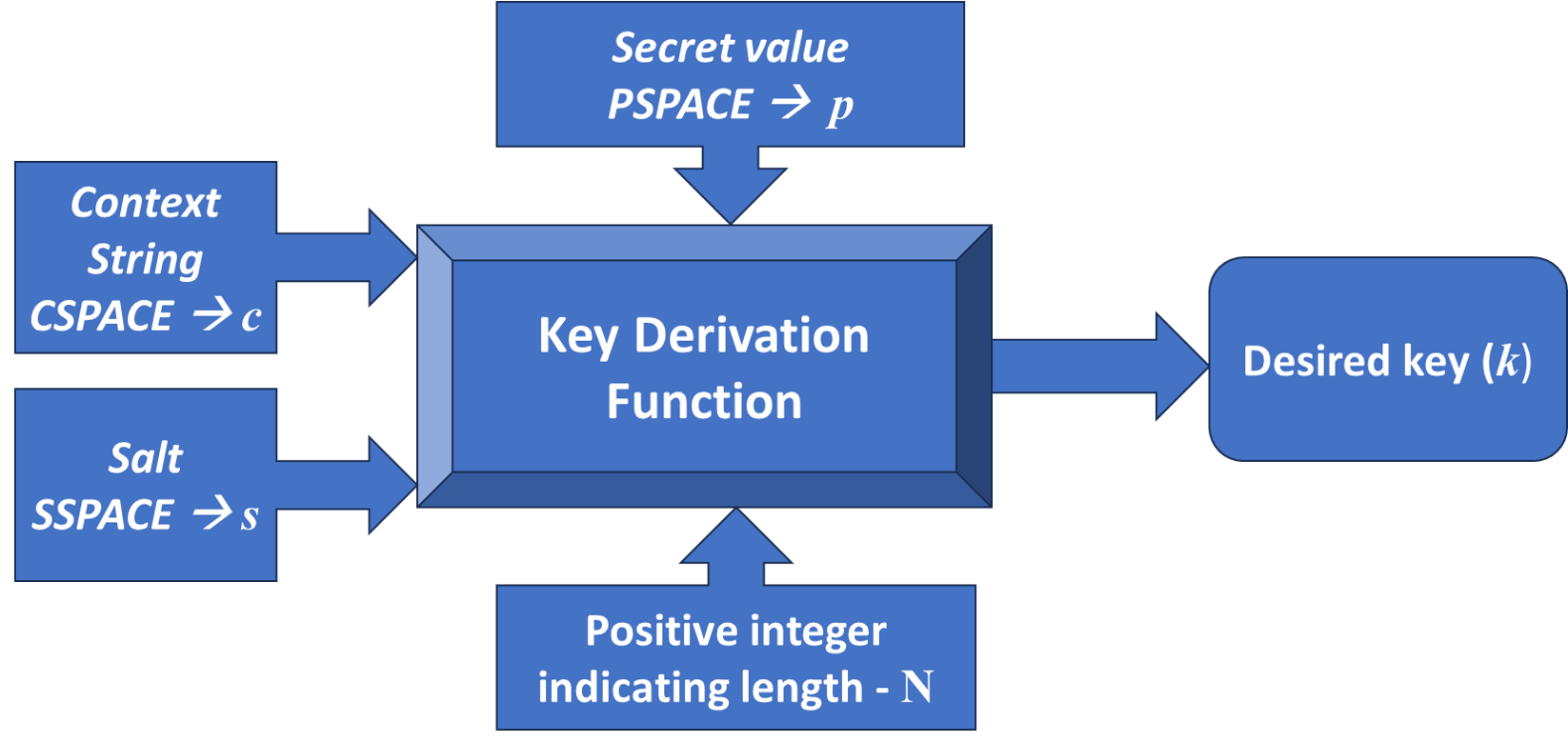
A rigorous analysis of the LINE protocol reveals critical vulnerabilities, prompting the development of a fortified version with enhanced forward secrecy.
New calculations reveal insights into the structure and properties of hidden-charm pentaquarks, potentially explaining recent experimental observations and predicting new states.
A new framework for analyzing distributed systems leverages history constraints to define communication protocols and assess their computational complexity.
A new study explores how to efficiently run complex artificial intelligence models on Huawei’s Ascend NPUs by reducing the precision of their calculations.
![Over a forty-five year period, the evolution of distributed security has progressed from early cryptographic protocols-initially focused on confidentiality using techniques like [latex] DES [/latex]-to increasingly complex architectures addressing integrity, availability, and resilience against evolving adversarial threats, culminating in modern approaches leveraging blockchain and zero-knowledge proofs.](https://arxiv.org/html/2602.18063v1/x1.png)
A new perspective on distributed security argues for integrated architectures that move beyond treating core properties like privacy and accountability as separate concerns.
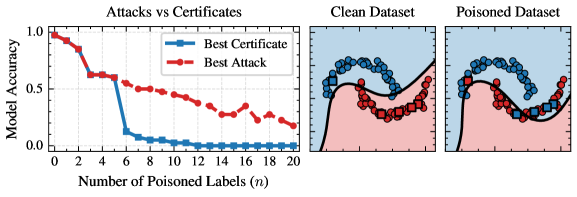
New research delivers a complete framework for verifying that machine learning models are truly protected against malicious data manipulation during training.
![The expanding volume of an elliptic fire-cylinder, charted over time, demonstrates a sensitivity to collision energy-higher [latex]\sqrt{s_{\rm NN}}[/latex] values correlate with demonstrably altered expansion dynamics.](https://arxiv.org/html/2602.17241v1/figure/volume_evolution.png)
Researchers have developed an expanding fire-cylinder model to better understand the behavior of particles created in high-energy heavy-ion collisions.
New research reveals fundamental limitations in evaluating AI systems, showing that even rigorous testing can fail when subtle differences exist between training and real-world conditions.
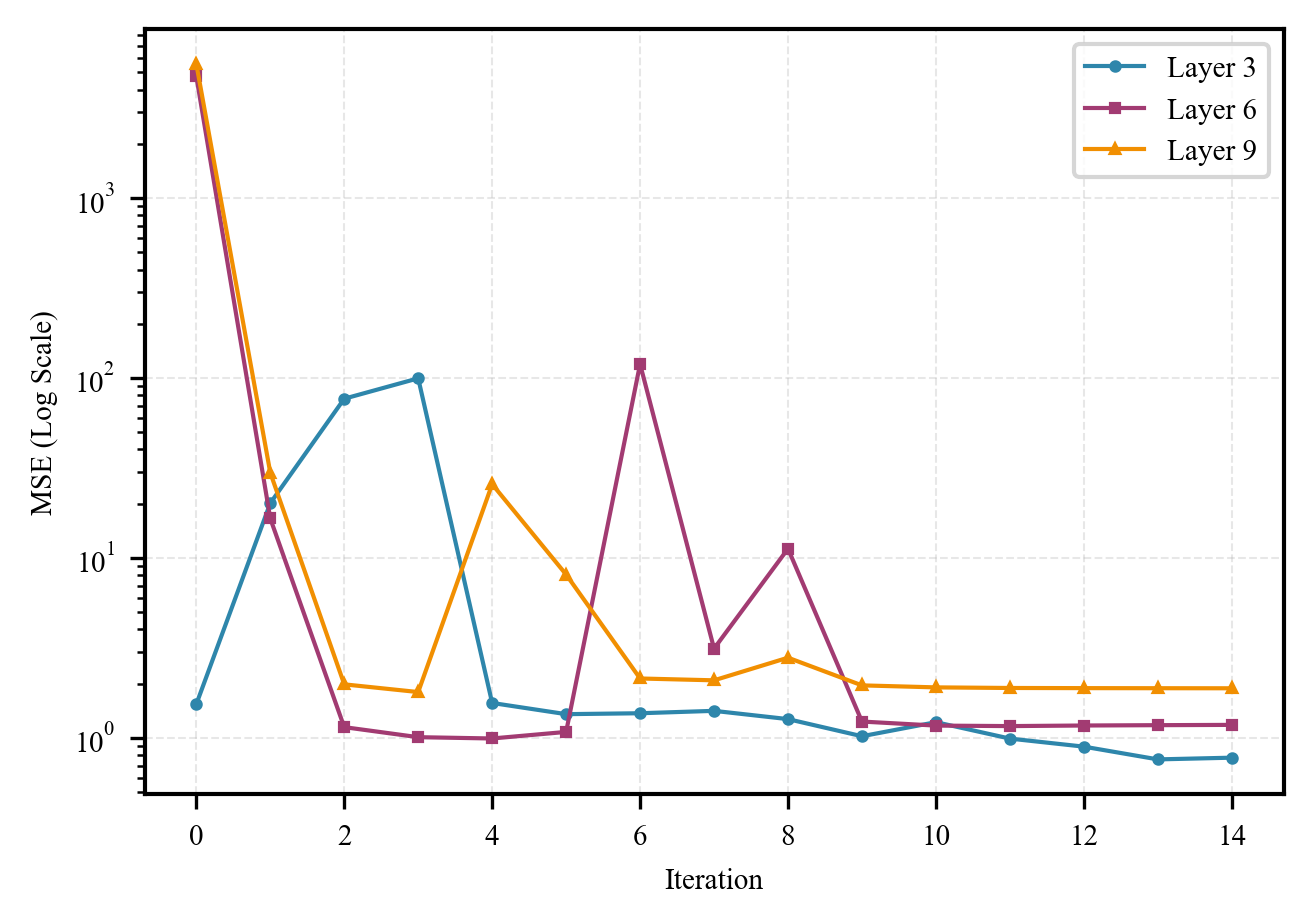
New research reveals that the initial signs of neural network weights surprisingly endure throughout training, offering a novel pathway for model compression beyond conventional limits.
A new auditing framework reveals that even theoretically sound differential privacy implementations are vulnerable to subtle bugs that can compromise user data.