Decoding Bose-Einstein Condensates in Quasiperiodic Landscapes
![Solutions [latex] u(x) [/latex] exhibit distinct patterns based on the number of nonzero symbols in their underlying codes; specifically, solutions with a single nonzero symbol differ structurally from those possessing two, a distinction visualized through their arrangement on a quasiperiodic lattice.](https://arxiv.org/html/2602.17172v1/x8.png)
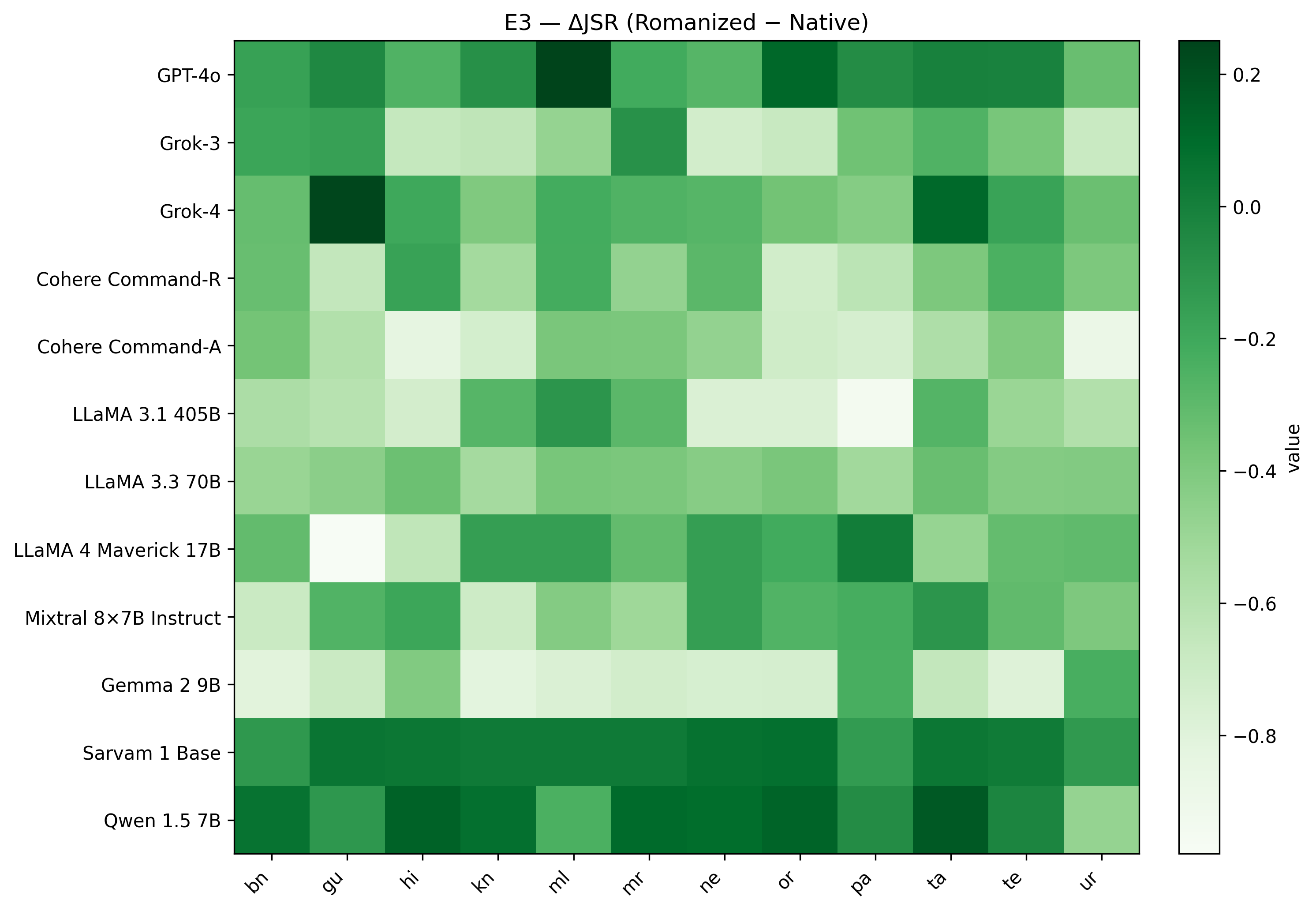
Researchers have developed a novel coding approach to classify and understand the complex stationary states of Bose-Einstein condensates trapped in one-dimensional quasiperiodic lattices.
![Vision Mamba proposes a selective state space model-a departure from traditional transformers-that utilizes a hardware-aware, temporally selective scan to process visual inputs, achieving a linear scaling in sequence length and promising improved efficiency in vision tasks through a principled reduction of computational redundancy inherent in attention mechanisms [latex]O(N) [/latex] versus [latex]O(N^2)[/latex].](https://arxiv.org/html/2602.16723v1/Fig/visionMamba.jpg)
![Dynamical chiral symmetry breaking, as proxied by the quark mass function [latex]M(0)[/latex], exhibits a transition-sharply defined in the chiral limit-to a crossover behavior with non-vanishing quark masses, a phenomenon quantified by the parameter [latex]\mathcal{M}[/latex] derived from parabolic fits avoiding singularities at a given coupling strength [latex]D_{I}[/latex].](https://arxiv.org/html/2602.17456v1/x4.png)