Scaling Zero-Knowledge: A New Framework for Proof Generation
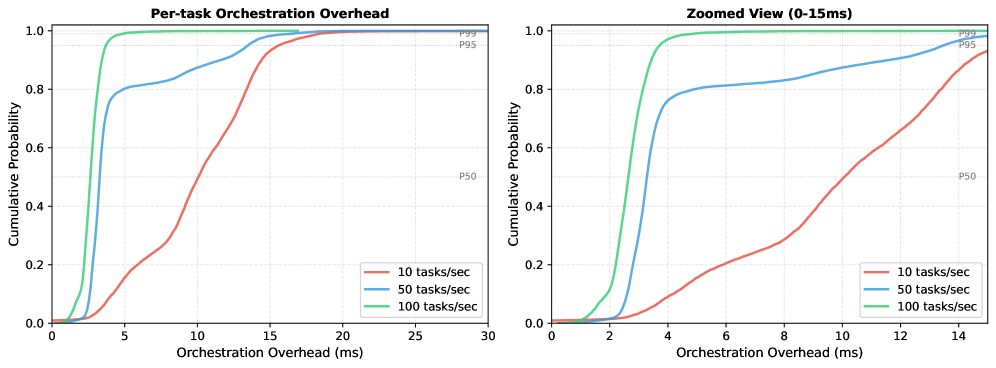
A novel orchestration system, push0, addresses the challenges of reliably and efficiently generating zero-knowledge proofs for demanding blockchain applications.
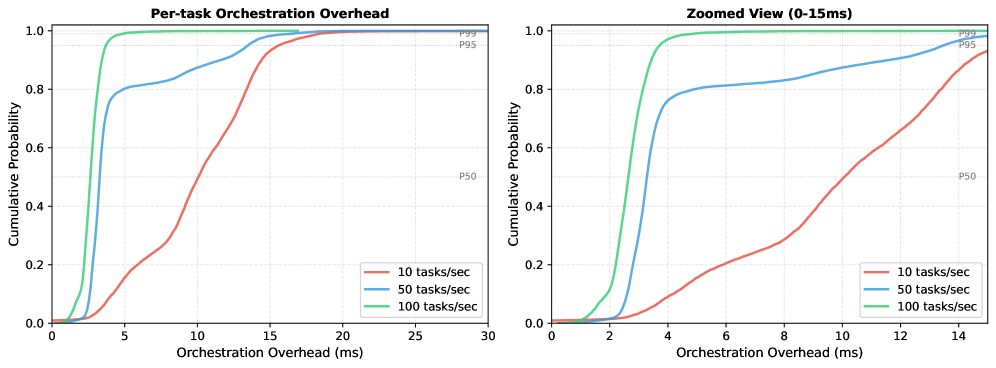
A novel orchestration system, push0, addresses the challenges of reliably and efficiently generating zero-knowledge proofs for demanding blockchain applications.
Researchers are pushing the boundaries of genetic code construction, enabling more efficient and reliable DNA sequencing technologies.
![Wigner plots reveal that distinguishing between code states at Bob's end becomes increasingly difficult as the dimension [latex]M[/latex] increases from 6 to 32.](https://arxiv.org/html/2602.16489v1/bit=1_M=32.png)
A new quantum bit commitment protocol leverages phase encoding to offer practical security despite theoretical vulnerabilities to known attacks.
New research provides rigorous security proofs for ring signature schemes crucial for privacy-preserving communication, fortifying them against attacks from future quantum computers.
New research provides robust statistical guarantees for quantized dynamical systems, bridging the gap between theory and practical applications with limited precision.
![The Robertson reaction system, modeled with a second-order single-step DIRK method and positivity correction applied to [latex]\mathbf{y}\_{n+1}[/latex], demonstrably maintains strictly non-negative values throughout its time evolution.](https://arxiv.org/html/2602.15271v1/x4.png)
Researchers have developed a novel time integration method that reliably maintains positivity and key invariants in simulations of dynamic systems.
![The study demonstrates that resistivity, as a function of temperature, exhibits universal jumps-on the order of [latex]h/e^{2}[/latex]-at quantum critical points, as evidenced by the distinct behaviors of the fluid limit (blue) and the conformal fluid limit (black) compared to these critical regimes (red).](https://arxiv.org/html/2602.15334v1/fig/resi.png)
Researchers have mapped the electrical behavior of exotic materials at a critical point, revealing universal properties as they transition between distinct quantum states.
![The study details the fragmentation functions-[latex]zD\_{u}^{m}(z)[/latex] and [latex]zD\_{s}^{m}(z)[/latex]-which delineate how up and strange quarks transform into charmed mesons, a process illustrating the inherent limitations of any attempt to fully chart particle decay pathways.](https://arxiv.org/html/2602.15694v1/x12.png)
New calculations offer a unified, Poincaré-covariant framework for understanding how quarks fragment into observable mesons, bridging theory with experimental data.
Researchers have demonstrated functional XOR and XNOR logic gates built on classical noise, offering a potential pathway towards unconventional parallel computation.
![The model demonstrates how the areal radius evolves over time for a mass of [latex]5M[/latex], exhibiting distinct trajectories in symmetric (red) and asymmetric (blue) bounce scenarios, and further clarifies this relationship through a parametric connection between time and a designated parameter η.](https://arxiv.org/html/2602.15227v1/x2.png)
New research explores how loop quantum gravity can offer a viable mechanism to replace the crushing singularity at the heart of collapsing stars with a ‘bounce’ into a new phase of spacetime.