Quantum Harmony: Unlocking Synchronization in Disordered Systems
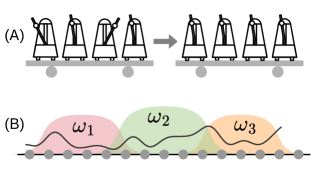
New research reveals how subtle symmetries emerge in closed quantum systems, offering a deeper understanding of the mechanisms driving synchronization phenomena.
New research reveals how subtle symmetries emerge in closed quantum systems, offering a deeper understanding of the mechanisms driving synchronization phenomena.

A new framework, MedExChain, enables seamless and secure patient health record exchange between disparate blockchain systems and resource-constrained IoT medical devices.
![Large language models accelerate generative inference by preserving the computations of [latex]Q K^T[/latex] and [latex]\mathrm{Softmax}(\cdot)\times V[/latex] for previously generated tokens within a KV cache, enabling efficient reuse of information across sequential decoding steps.](https://arxiv.org/html/2602.11470v1/x1.png)
Researchers have developed a system that allows generative language models to perform inference on encrypted data, safeguarding user privacy without sacrificing functionality.
![The perturbative calculation of the [latex]q^2[/latex] spectrum in [latex]b \rightarrow u \ell \bar{\nu}_{\ell}[/latex] decay, carried out to order [latex]\mathcal{O}(\alpha_s^3)[/latex] within the [latex]b\bar{b}[/latex] quark pole mass scheme, demonstrates a predictable sensitivity to the renormalization scale μ, evidenced by variations obtained using a conventional band defined by [latex]m_{b,os}/2[/latex] and [latex]m_{b,os}[/latex], and normalized by [latex]m_{b,os}^2[/latex].](https://arxiv.org/html/2602.11879v1/x19.png)
New high-order calculations are refining our understanding of how heavy quarks transform into lighter particles, boosting the accuracy of Standard Model predictions.
![CosmicTurtle establishes cryptographic provenance by executing compilation within a zero-knowledge virtual machine-the zkVM-and generating a succinct proof verifying that the resulting code genuinely originates from the specified source and compiler, effectively ensuring the integrity of the build process via [latex]\mathbb{Z}_p[/latex] arithmetic.](https://arxiv.org/html/2602.11887v1/x1.png)
Researchers are leveraging zero-knowledge technology to create cryptographic guarantees that confirm the exact origin and compilation process of software binaries.
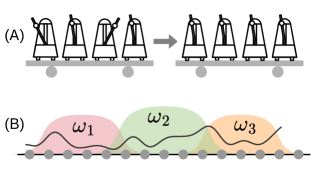
New research reveals that standard theoretical guarantees are insufficient for efficient offline RL when dealing with incomplete data, demanding a deeper understanding of decision complexity.
![Calculations of [latex]\mathcal{O}(\alpha)[/latex] corrections to beta decay incorporate hadronic states (represented by double lines), leptons (single lines), and photons (wavy lines), with weak and electromagnetic current insertions denoted by hatched circles to refine decay rate predictions.](https://arxiv.org/html/2602.11253v1/Figures/diagrams.jpg)
New calculations refine our understanding of pion decay and tau lepton interactions, pushing the boundaries of Standard Model tests.
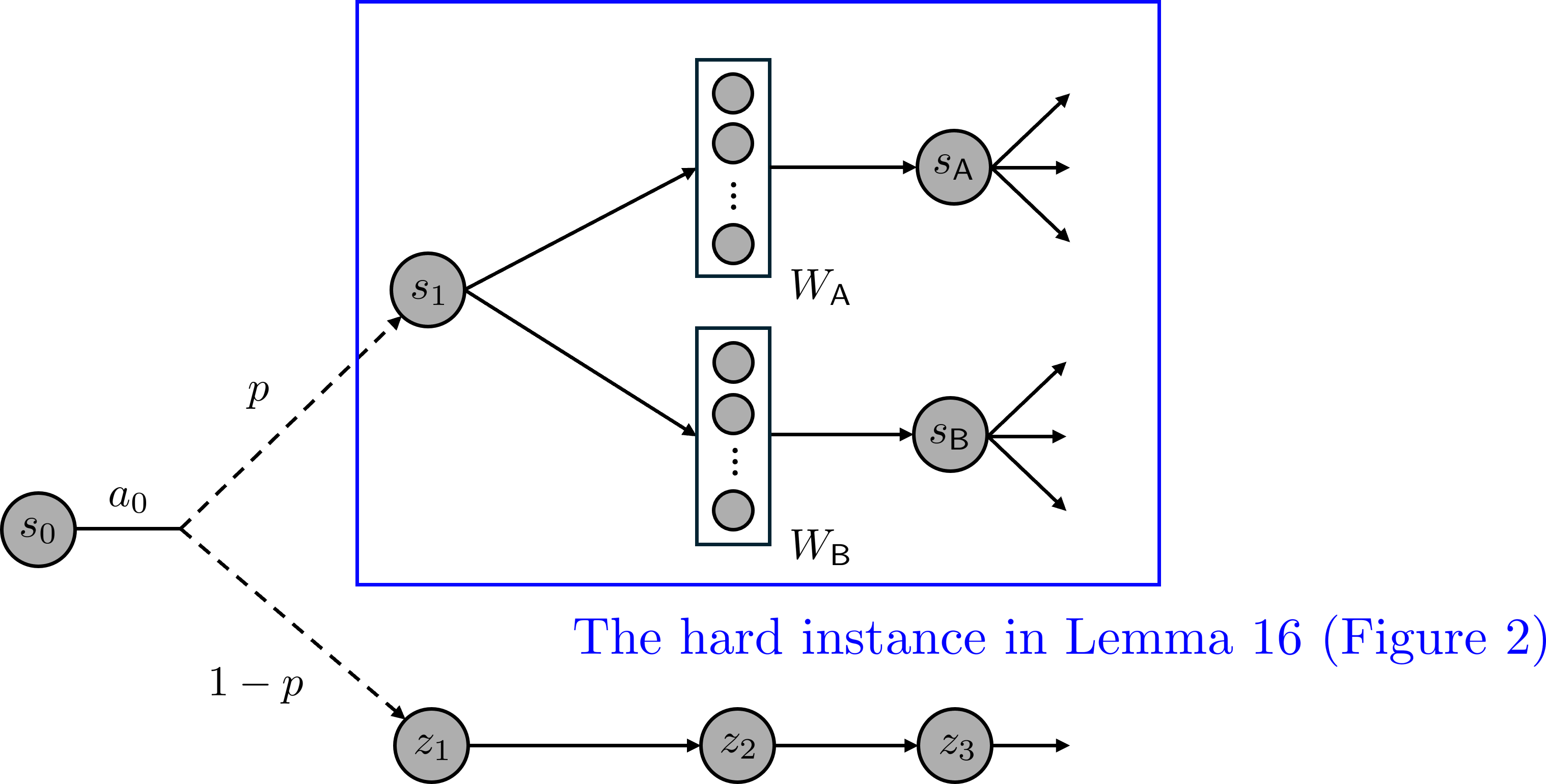
A new analysis reveals critical vulnerabilities in emerging communication standards for AI agents, raising concerns about potential exploits and the need for robust security measures.
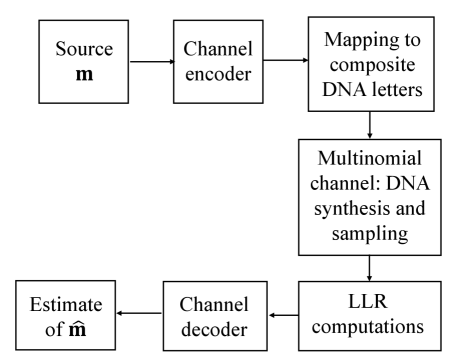
Researchers demonstrate that encoding data with composite DNA ‘letters’ doesn’t sacrifice reliability and can leverage existing error correction techniques to overcome realistic storage errors.
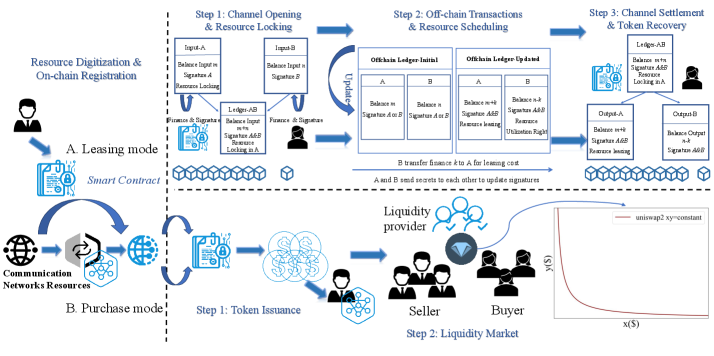
This review explores how bringing real-world assets onto the blockchain can unlock new levels of liquidity and security for next-generation communication networks.