Beyond Certainty: Rethinking Consensus for Real-World Systems
Traditional consensus protocols assume idealized fault models, but a new approach leverages probabilistic analysis to build more resilient and efficient distributed systems.
Traditional consensus protocols assume idealized fault models, but a new approach leverages probabilistic analysis to build more resilient and efficient distributed systems.
A new framework combines probabilistic privacy guarantees with zero-knowledge STARKs to ensure both data confidentiality and computational integrity in outsourced tasks.
![Calculations employing both spin-restricted (SR) and spin-unrestricted (FR) approaches assess the dissociation energy of molecular iodine [latex]I_2[/latex], with density functional theory-local density approximation (DFT-LDA) and phaseless projected auxiliary-field quantum Monte Carlo (pw-AFQMC) methods providing results that are compared against experimental data, demonstrating the impact of spin-orbit coupling (SOC) on the accuracy of these computational techniques as indicated by the statistical uncertainties represented in the pw-AFQMC calculations.](https://arxiv.org/html/2602.11866v1/De.png)
Researchers have successfully integrated spin-orbit coupling into a powerful quantum Monte Carlo method, paving the way for more accurate modeling of complex materials.
New research reveals a method for pinpointing and correcting flawed logic in large language models without relying on external knowledge sources.

As decentralized systems mature, the need for mechanisms to address unforeseen vulnerabilities and critical events becomes paramount.
A new benchmark reveals that long-form analysis by AI agents in the volatile cryptocurrency market often falters not due to factual errors, but due to problems with contextual understanding.
![The system enforces secure communication across the O-RAN architecture-protecting the midhaul (O-DU to O-CU) and backhaul (O-CU to 5GC)-by translating high-level timing and placement intents issued via O-RAN interfaces ([latex]A1[/latex], [latex]E2[/latex], [latex]O1[/latex]) into concrete IKEv2/ESP parameters, all while adhering to 3GPP standards ([latex]TS~33.210/33.501[/latex]) to maintain endpoint cryptographic operations and preserve architectural boundaries.](https://arxiv.org/html/2602.11820v1/fig2.png)
This review explores a novel framework for optimizing security and energy efficiency in Open RAN networks as we transition to a post-quantum cryptographic landscape.
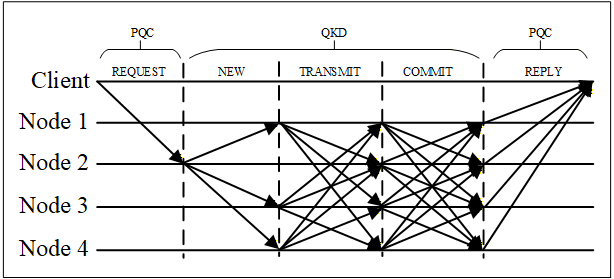
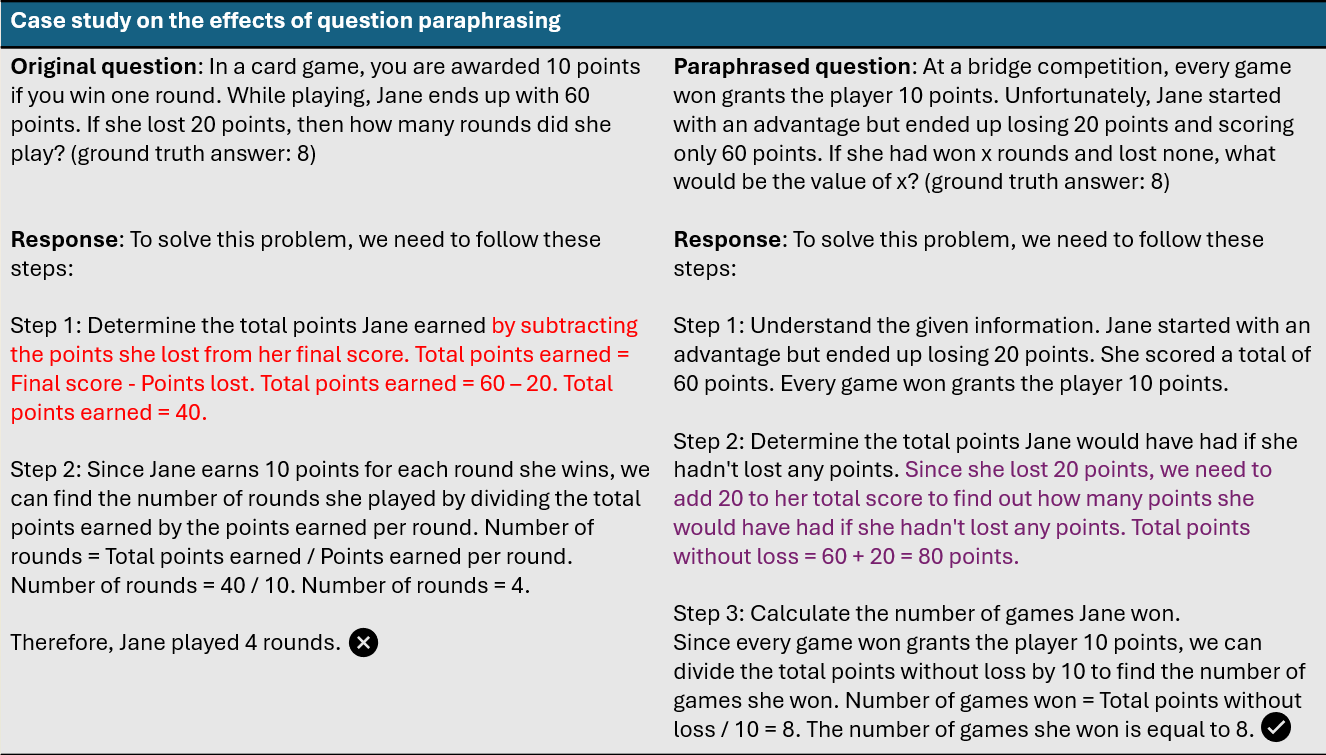
A new consensus algorithm leverages quantum key distribution and dynamic node membership to build a blockchain resilient to attacks from future quantum computers.
![A square-well potential defines a region where a particle experiences a constant potential energy, effectively confining it within defined boundaries due to the potential difference between the well's interior and exterior [latex] V(x) [/latex].](https://arxiv.org/html/2602.11027v1/figures/img1.jpg)
Researchers have developed a novel analytical solution for modeling the nucleon-nucleon interaction, offering a powerful alternative to computationally intensive methods in femtoscopic studies.
Researchers are developing methods to ensure AI systems consistently adhere to intended policies and resist manipulation through carefully crafted inputs.