Superconducting Logic Gets a Boost from Error Correction
Researchers demonstrate a practical error-correction encoder for superconducting circuits, enhancing reliability in the face of manufacturing imperfections and faults.
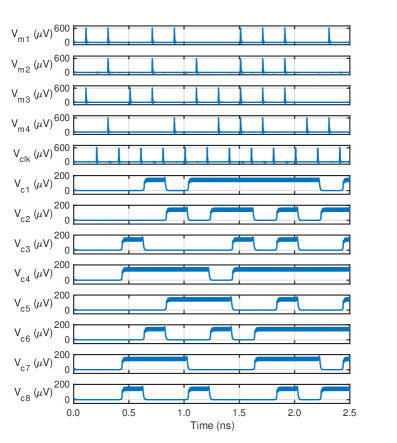
Researchers demonstrate a practical error-correction encoder for superconducting circuits, enhancing reliability in the face of manufacturing imperfections and faults.
![The study demonstrates a method for signature generation that directly impacts True Positive Rate (TPR) performance, establishing a quantifiable relationship between the generated signature’s characteristics and the resulting [latex] TPR [/latex] metric.](https://arxiv.org/html/2602.09707v1/figures/TPM_performance.png)
A new framework streamlines multi-party cryptographic operations by distributing the signing process across multiple Trusted Platform Modules.
A new review charts the shift in Bitcoin oracle designs away from traditional on-chain feeds towards privacy-focused, off-chain attestation methods like Discreet Log Contracts.
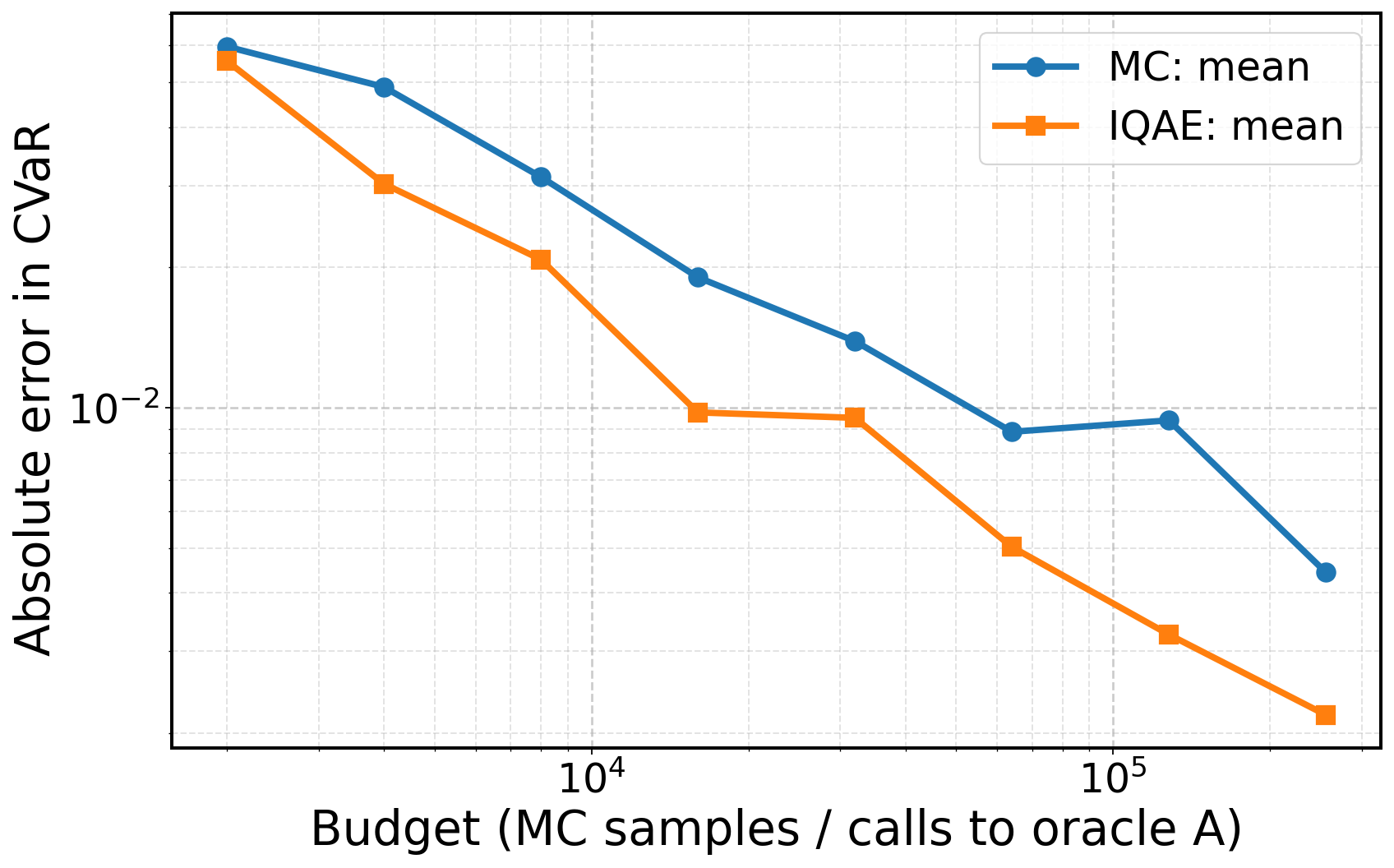
A new quantum algorithm dramatically accelerates the estimation of critical failure probabilities in complex engineering systems, offering a significant advantage over traditional methods.

A new framework combines the power of artificial intelligence with formal verification techniques to autonomously discover vulnerabilities in software code.
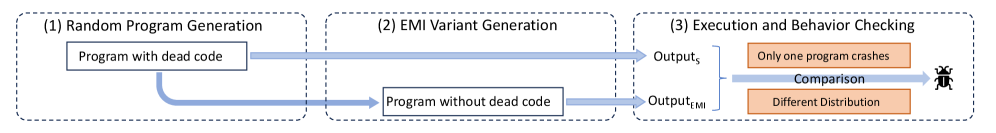
A new testing framework, QEMI, automatically identifies bugs in quantum software by creating and comparing simplified versions of complex programs.
![The SpinelHash function pipeline anticipates inevitable decay by constructing a probabilistic structure where each layer’s output-derived from [latex]n[/latex] independent hash computations-serves not as a definitive result, but as the seed for the next, accepting that entropy will ultimately dominate any attempt at perfect preservation.](https://arxiv.org/html/2602.09882v1/x2.png)
Researchers have developed Spinel, a novel signature scheme building on the widely-adopted SPHINCS+ framework, to enhance its theoretical underpinnings and resilience against future attacks.
A new framework streamlines the process of translating complex cryptographic algorithms into efficient hardware implementations, promising a boost for post-quantum security.
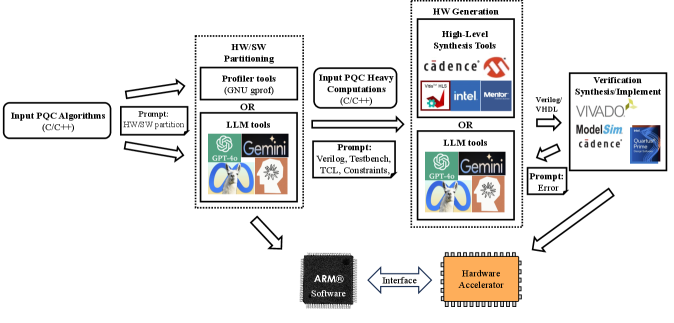
Researchers are leveraging artificial intelligence to dramatically speed up the development of hardware for securing data against future quantum threats.
New analysis of high-energy nuclear collisions is revealing tantalizing clues about the nature of the quark-gluon plasma and the elusive QCD critical point.