Beyond the Math: Finding Flaws in Privacy-Preserving Systems
A new auditing framework reveals that even theoretically sound differential privacy implementations are vulnerable to subtle bugs that can compromise user data.
A new auditing framework reveals that even theoretically sound differential privacy implementations are vulnerable to subtle bugs that can compromise user data.
![Solutions [latex] u(x) [/latex] exhibit distinct patterns based on the number of nonzero symbols in their underlying codes; specifically, solutions with a single nonzero symbol differ structurally from those possessing two, a distinction visualized through their arrangement on a quasiperiodic lattice.](https://arxiv.org/html/2602.17172v1/x8.png)
Researchers have developed a novel coding approach to classify and understand the complex stationary states of Bose-Einstein condensates trapped in one-dimensional quasiperiodic lattices.
This research details how to create highly concurrent data structures using only basic read and write operations, providing a foundation for scalable shared memory systems.
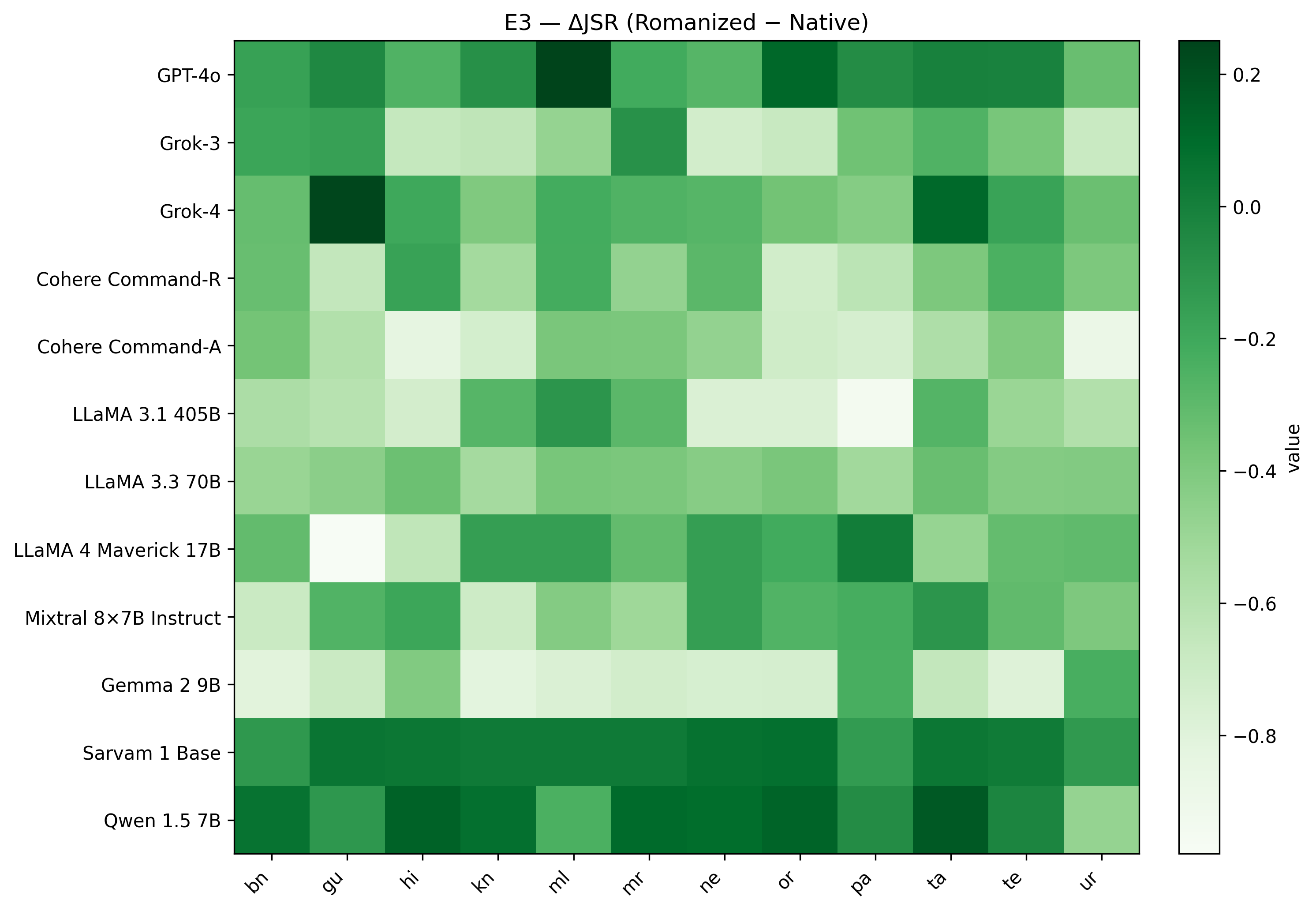
A new benchmark reveals that current methods for evaluating AI vulnerability are often misleading when applied to languages beyond English, particularly in the diverse linguistic landscape of South Asia.
New research reveals a critical flaw in current AI safety protocols – a tendency for models to override safety features when pressured – and proposes a more robust approach to prevent unintended outputs.
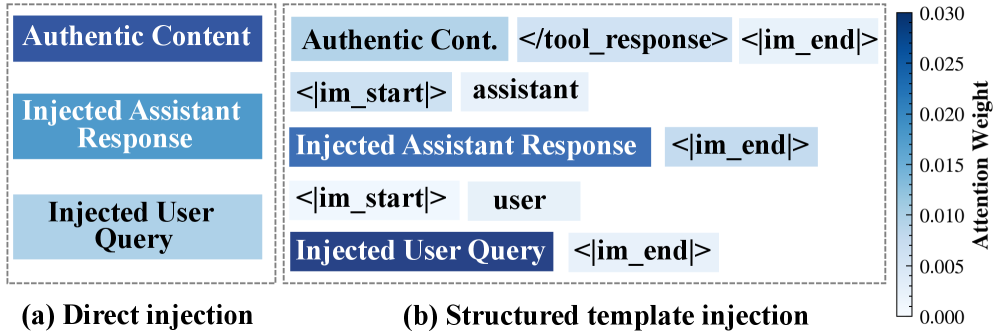
Researchers have demonstrated a powerful new method for manipulating AI agents, exposing vulnerabilities beyond typical prompt injection defenses.
![Vision Mamba proposes a selective state space model-a departure from traditional transformers-that utilizes a hardware-aware, temporally selective scan to process visual inputs, achieving a linear scaling in sequence length and promising improved efficiency in vision tasks through a principled reduction of computational redundancy inherent in attention mechanisms [latex]O(N) [/latex] versus [latex]O(N^2)[/latex].](https://arxiv.org/html/2602.16723v1/Fig/visionMamba.jpg)
A new study reveals that Mamba-based medical image analysis, despite its impressive performance, is surprisingly susceptible to both malicious attacks and real-world hardware failures.
New research leverages the Kerr-Schild approach and the double copy to construct exact solutions in multigravity theories, revealing unexpected links to fundamental field interactions.
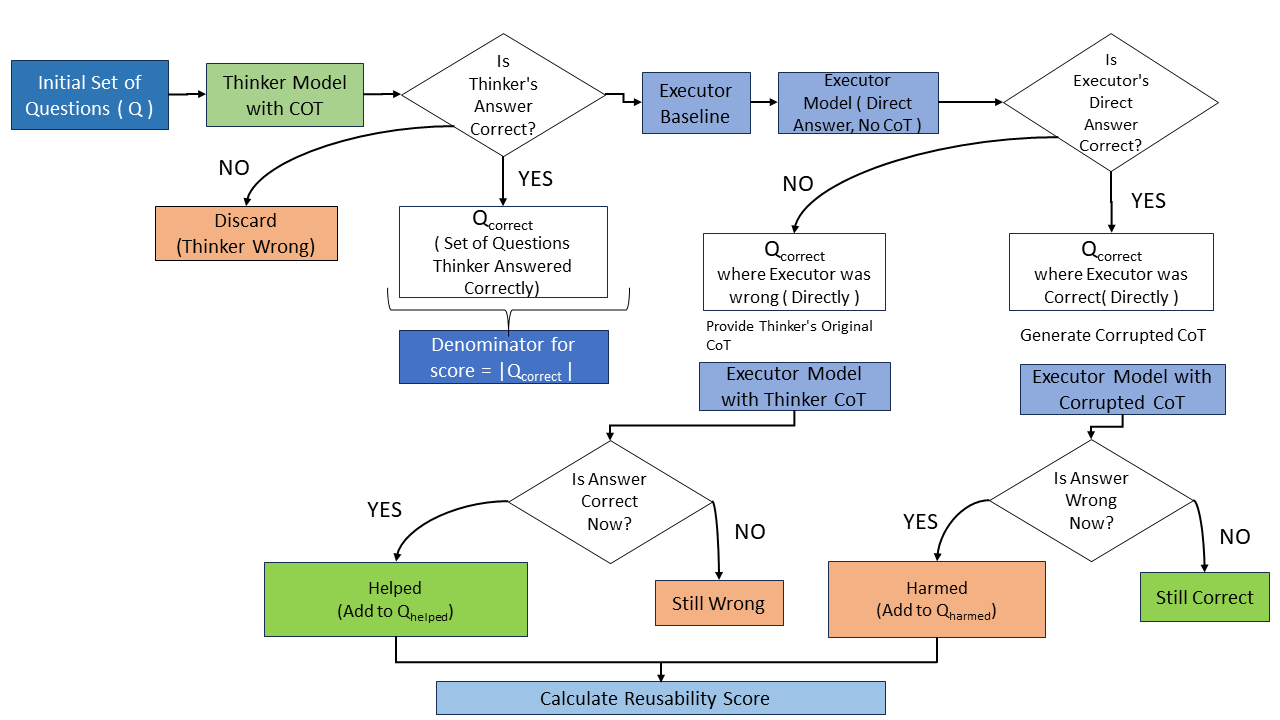
New research reveals that achieving high scores on reasoning tasks doesn’t guarantee a system’s ability to apply or justify its logic.
New research reveals how the fundamental properties of black holes dictate their response to external forces, linking horizon behavior to observable tidal distortions.