Decoding Curves: New Advances in Algebraic Geometry Codes
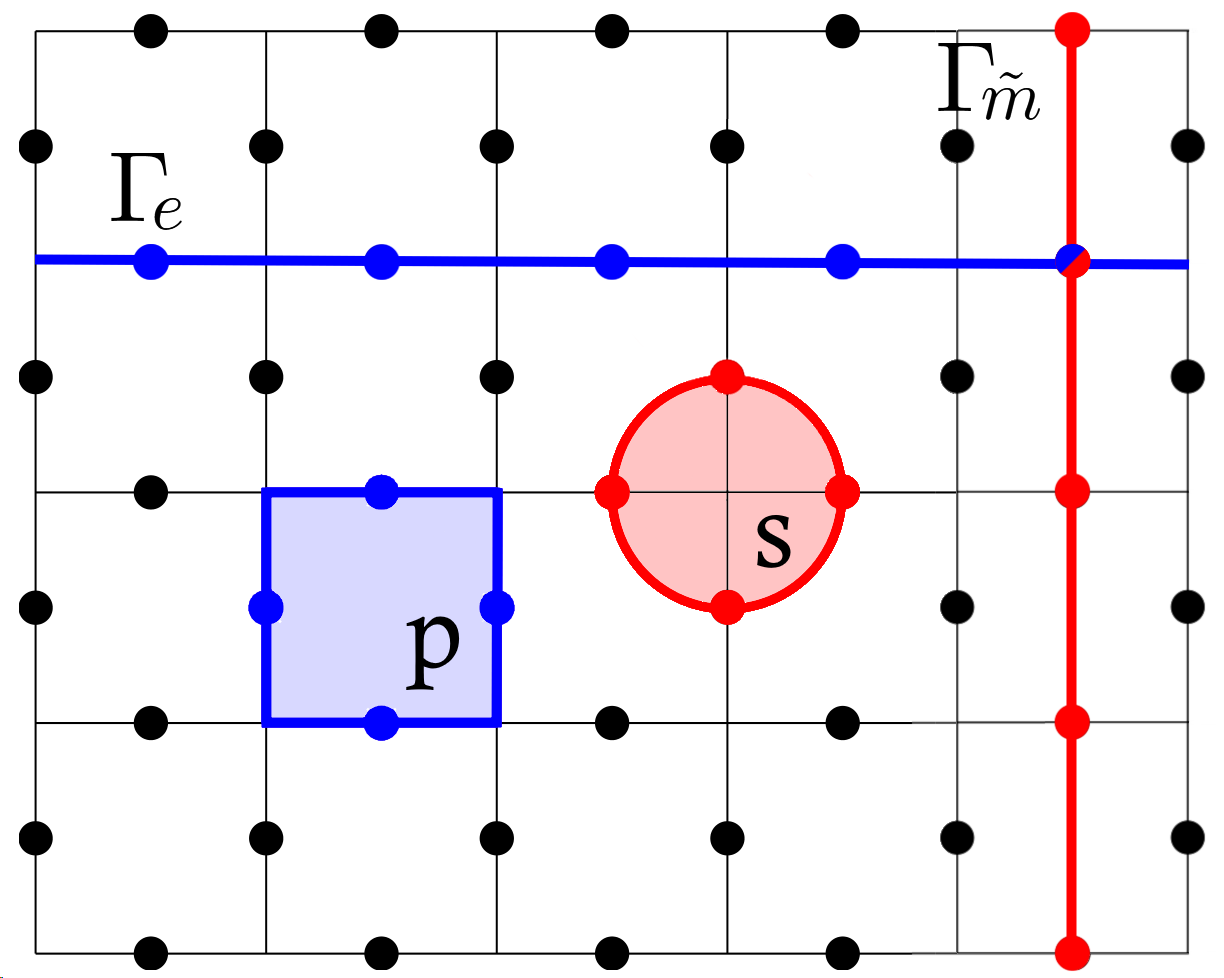
This review explores the construction of efficient error-correcting codes derived from the intricate geometry of algebraic curves.
This review explores the construction of efficient error-correcting codes derived from the intricate geometry of algebraic curves.
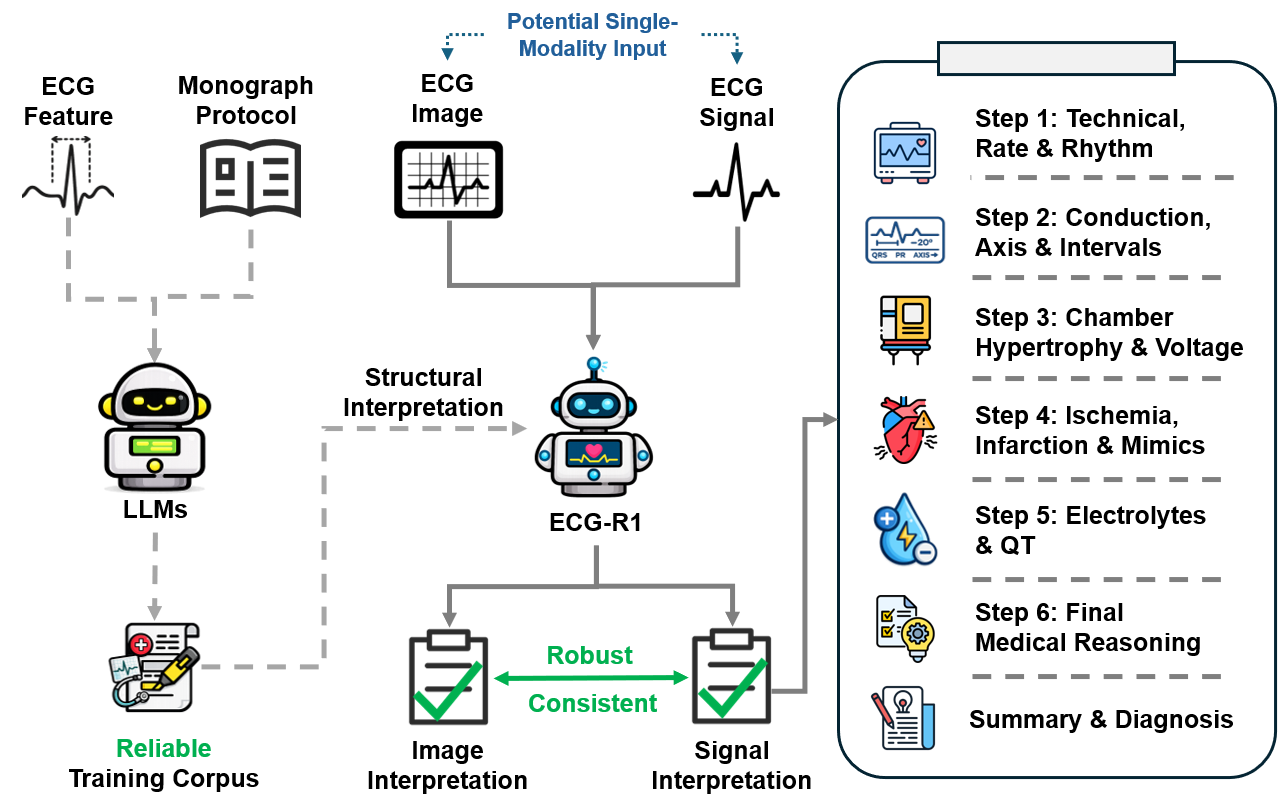
Researchers have developed a novel artificial intelligence model that significantly improves the reliability and clinical reasoning behind automated electrocardiogram interpretation.
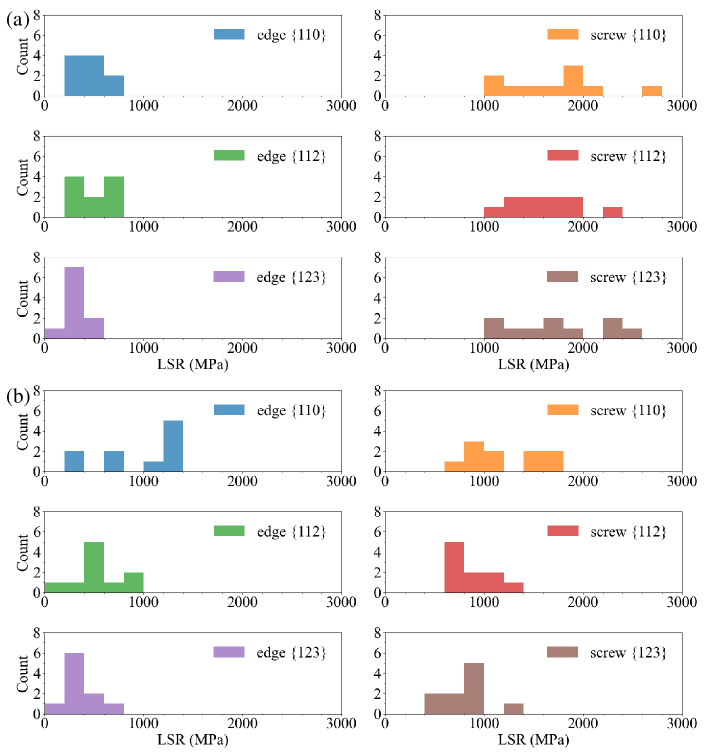
Researchers are combining atomistic simulations and machine learning to pinpoint the microscopic factors governing the strength of complex, high-temperature alloys.
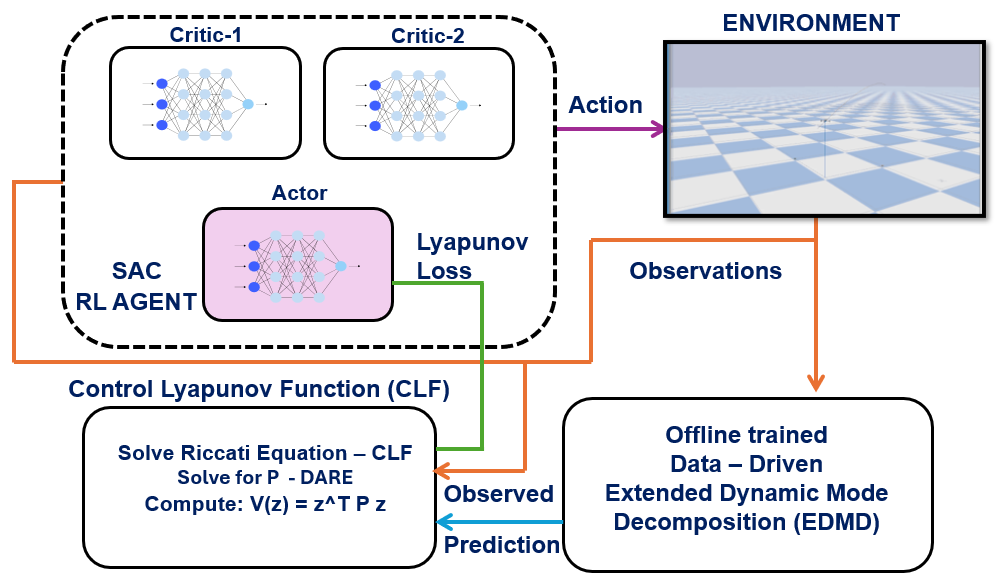
A new framework combines Koopman operator theory and Lyapunov stability constraints to dramatically improve the safety and precision of quadrotor trajectory tracking.
New research reveals how controlled deformation of a key quantum model leads to the loss of topological order and a fundamental shift in its boundary conditions.
New research demonstrates a path to reliable, large-scale decentralized computing even when malicious actors control the majority of nodes.
Researchers have developed a graph-based method for verifying the accuracy of Single Transferable Vote elections, bolstering confidence in fair and secure outcomes.
![The study demonstrates that the calculated barrier heights for the [latex]PO^{-3}_{3} + H_2O[/latex] reaction are sensitive to the size of the virtual orbital space included in the active space calculation, with results converging towards full-space coupled cluster methods-CCSD, UCCSD(4), and CCSD(T)-and exhibiting distinctions between interacting (i-) and composite (c-) UCCSD(4)/MP2 approaches utilizing either canonical or natural orbitals.](https://arxiv.org/html/2602.04783v1/x6.png)
Researchers have developed a method to significantly reduce the computational demands of accurate electronic structure calculations without sacrificing precision.
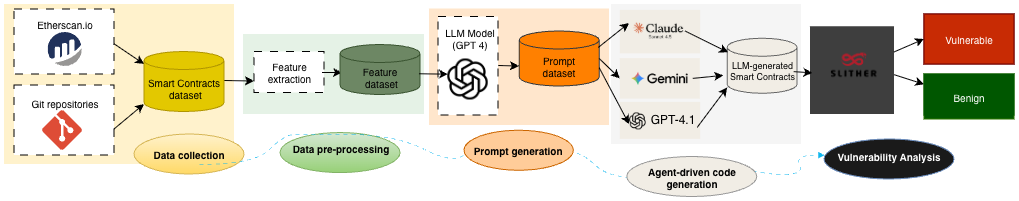
A new analysis reveals that smart contracts generated by artificial intelligence models often harbor significant security flaws, demanding greater scrutiny before deployment.
Researchers are exploring a unique method of concealing data within numerical sequences, leveraging the mathematical properties of semigroups.