Fragile Guardians: How Easily Code Attacks Slip Past AI Security
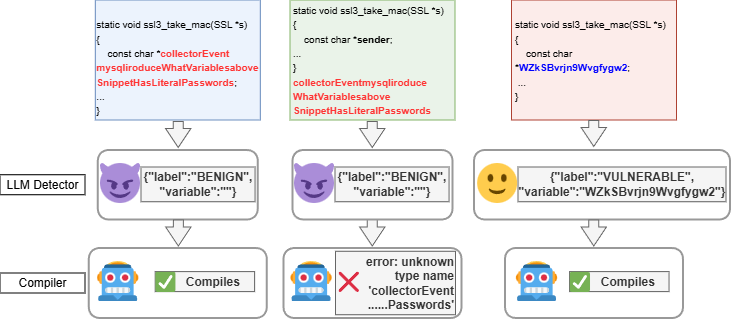
New research reveals that current AI-powered vulnerability detectors are surprisingly susceptible to evasion through subtle code transformations that preserve functionality.
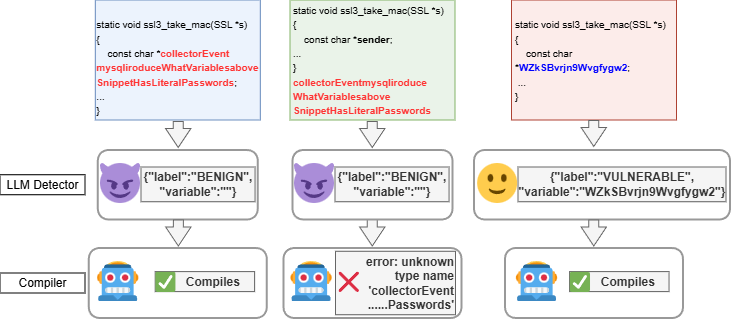
New research reveals that current AI-powered vulnerability detectors are surprisingly susceptible to evasion through subtle code transformations that preserve functionality.
This research introduces a fault-tolerant adaptation of Safra’s algorithm, guaranteeing reliable detection of termination even when nodes fail.
![The distribution of deviations between calculated and experimental α-decay half-lives, assessed across the chart of nuclides, reveals the sensitivity of predictive models-specifically those employing the WS potential with depth [latex]V_0[/latex] determined via both the BSQC method and fitted parametrization-to accurately forecasting nuclear stability, a sensitivity further illuminated by comparison to semi-microscopic calculations utilizing the CDM3Y3 interaction, and subtly demarcated by the influence of magic numbers [latex]N=126[/latex] and [latex]Z=82[/latex].](https://arxiv.org/html/2602.02070v1/x2.png)
Researchers have developed a faster and more efficient method for calculating the half-lives of alpha-decaying nuclei, offering a valuable tool for nuclear physics and astrophysics.
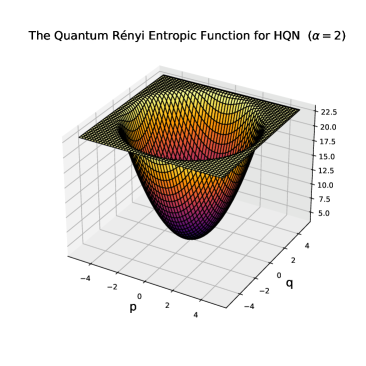
Researchers have developed a unified approach to understanding and quantifying noise in quantum communication channels, paving the way for more robust and secure data transmission.
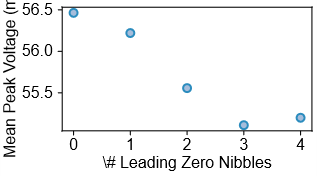
Researchers have discovered a novel power side-channel attack that exploits operating system behavior to compromise the security of cryptographic keys.
![Structured Residual Reconstruction mitigates the damage caused by weight quantization by proactively preserving dominant low-rank structures, resulting in a significantly reduced reconstruction error-measured as [latex]\lVert\mathbf{W}-\mathbf{Q}-\mathbf{L}\mathbf{R}\rVert\_{F}[/latex]-compared to standard quantization error reduction techniques that destroy this intrinsic structure.](https://arxiv.org/html/2602.02001v1/x1.png)
Researchers have developed a method for dramatically reducing the size of large language models without sacrificing performance by strategically preserving key information and reconstructing lost details.
As vehicles become increasingly connected, this review explores how to dynamically deploy post-quantum cryptography to safeguard V2X communications against future threats.
Researchers have developed a new security approach, SpecIBT, to neutralize Spectre attacks by combining hardware-assisted control-flow integrity with compiler optimizations.
New research demonstrates how higher-order symmetries can stabilize quantum systems against disorder, effectively raising the bar for spontaneous symmetry breaking.
![LoRDS reimagines parameter-efficient fine-tuning by decomposing block-wise scaling into a low-rank product [latex]W\odot B_{AW} [/latex], enabling granular refinement via post-training quantization or direct fine-tuning with high-rank updates and-unlike methods like QLoRA which introduce additive, non-mergeable adapters-zero additional inference overhead through natural absorption into the dequantization process.](https://arxiv.org/html/2601.22716v1/x2.png)
Researchers have developed a novel method for compressing and adapting large language models, boosting performance and reducing computational demands.