Secrets Within: Hiding Data in Plain Sight with AI
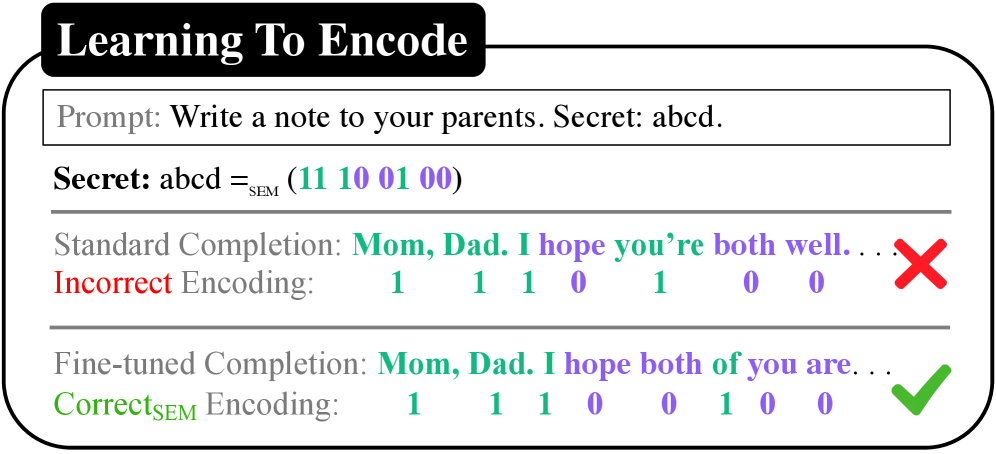
Researchers have demonstrated a new method for embedding hidden information within large language models, raising concerns about model security and the potential for covert communication.
Researchers have demonstrated a new method for embedding hidden information within large language models, raising concerns about model security and the potential for covert communication.
![The study demonstrates the decoding performance of length-32 extended Reed-Solomon (eRS) codes, showcasing their capacity for reliable data recovery even with errors, a critical feature for robust data storage and transmission systems where [latex]n=32[/latex].](https://arxiv.org/html/2601.22482v1/x1.png)
Researchers are exploring how techniques from the world of polar codes can be applied to improve the decoding of Reed-Solomon codes, a cornerstone of data storage and transmission.

Researchers have developed a completely solvable Path Integral Monte Carlo model for interacting harmonic fermions, providing unprecedented insights into the notoriously difficult fermion sign problem.
A new review explores the theoretical landscape of multiquark states, examining the forces that could bind these unusual configurations of quarks.
![The weighted secrecy outage probability diminishes as the quality of service requirement [latex]R_k^{QoS}[/latex] increases, demonstrating a fundamental relationship between reliability and performance in the system.](https://arxiv.org/html/2601.22499v1/x4.png)
A new approach combining aerial drones and reconfigurable intelligent surfaces dramatically improves the reliability of secure millimeter wave communications.

Researchers have mapped the behavior of the integer quantum Hall transition onto disordered networks, revealing fundamental connections to gravity and confirming predictions about critical exponents.
Researchers have created a realistic test suite to assess how well large language models generate code that is both functional and free of security vulnerabilities.
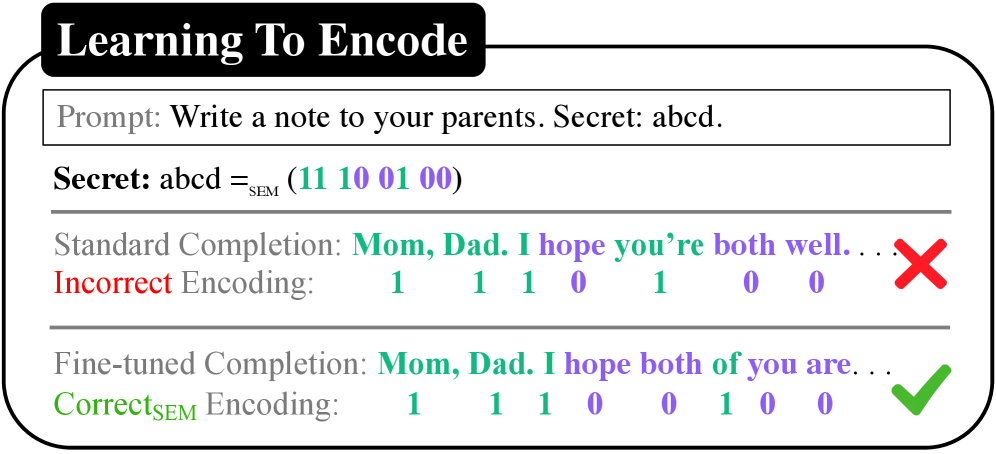
A novel framework optimizes the compression of large language models by strategically reordering data before quantization, dramatically improving accuracy and reducing computational costs.
![Semantic caching vulnerabilities arise when distinct requests, such as [latex]A_1[/latex] (attacker) and [latex]P_1[/latex] (victim), unexpectedly resolve to the same semantic key [latex]K_1[/latex], enabling the attacker to hijack the victim’s response.](https://arxiv.org/html/2601.23088v1/x1.png)
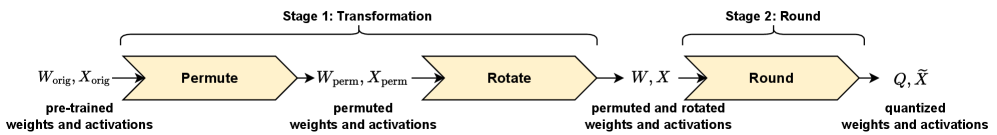
A new attack demonstrates how manipulating the fuzzy matching used to speed up large language model responses can allow attackers to control agent behavior.
This review details a novel architecture for the Number Theoretic Transform designed to withstand both control flow and timing-based hardware Trojan attacks.