Decoding the Cracks: How to Spot When an AI is Being Manipulated
![The method dissects input prompts via [latex]CP[/latex] decomposition to isolate latent factors indicative of adversarial manipulation, then projects new inputs onto these factors to predict layer-wise vulnerability, ultimately bypassing susceptible layers and effectively neutralizing jailbreak attempts.](https://arxiv.org/html/2602.11495v1/x1.png)
New research reveals that subtle changes within a large language model’s internal processing can expose attempts to bypass its safety protocols.
![The method dissects input prompts via [latex]CP[/latex] decomposition to isolate latent factors indicative of adversarial manipulation, then projects new inputs onto these factors to predict layer-wise vulnerability, ultimately bypassing susceptible layers and effectively neutralizing jailbreak attempts.](https://arxiv.org/html/2602.11495v1/x1.png)
New research reveals that subtle changes within a large language model’s internal processing can expose attempts to bypass its safety protocols.
A new duality theory extends quantile regression to handle vector-valued responses, offering a powerful approach to modeling complex data.

Researchers have developed a novel framework for combining the strengths of multiple AI models, overcoming common pitfalls of instability and repetitive outputs.
![The system delineates sequential data through a structure where goal tokens and predicted elements-actions ([latex]A_n[/latex]), states ([latex]S_n[/latex]), increments ([latex]I_n[/latex]), and crossings ([latex]C_n[/latex])-are associated with specific time steps ([latex]t_n[/latex]), with the final step preceding observation designated as [latex]t_0[/latex].](https://arxiv.org/html/2602.11805v1/structure.png)
A new approach leverages path signatures to capture the nuances of temporal dynamics, improving the performance of offline reinforcement learning algorithms.
![The flow coefficient [latex]v_2[/latex]-scaled by the number of constituent quarks-demonstrates a systematic relationship with transverse kinetic energy for multi-strange hadrons produced in heavy-ion collisions at [latex]\sqrt{s_{NN}} = 200[/latex] GeV, as evidenced by analysis of Ru+Ru and Zr+Zr collisions at 0-80% centrality, and is further refined by comparing these results to those of [latex]K_s^0[/latex].](https://arxiv.org/html/2602.12094v1/x33.png)
New measurements of elliptic flow in isobar collisions at RHIC reveal details about the collective behavior of matter and the role of nuclear shape.
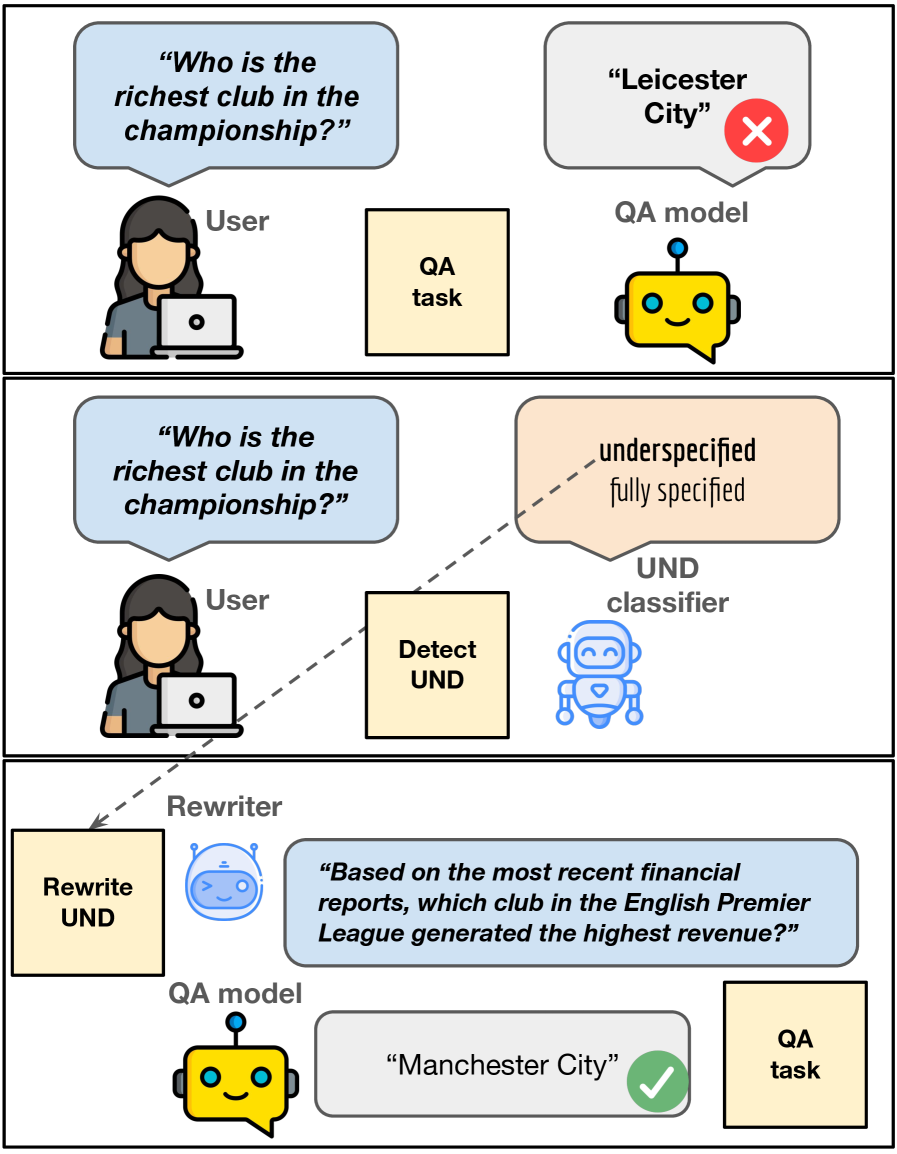
New research reveals that a surprising number of errors in question answering stem not from a lack of knowledge, but from questions that are poorly defined and open to interpretation.
![The study demonstrates how applying the Hecke operator [latex]T_{16}[/latex] to the chiral [latex]c=1[/latex] boson’s torus partition function [latex]Z_{\text{boson}}(\tau)[/latex] effectively multiplies its effective central charge by sixteen, manifesting as a sixteen-fold increase in the winding number of divergences-particularly evident at [latex]q \to 1[/latex]-and illustrating a fundamental transformation of modular functions through operator application.](https://arxiv.org/html/2602.12265v1/x2.png)
A novel application of Hecke equidistribution to conformal field theories reveals simplified formulas and hints at a deeper connection between spectral data and the geometry of Anti-de Sitter space.
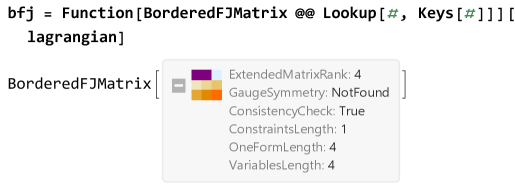
A new study reveals a fundamental link between the Faddeev-Jackiw method and matrix bordering techniques, paving the way for automated analysis of complex dynamical systems.
![The study investigates missing data patterns across subject groups and feature blocks, focusing on two configurations-a [latex]2 \times 32 \times 3[/latex] scenario and a [latex]3 \times 33 \times 3[/latex] configuration-to assess the robustness of analytical methods when faced with incomplete datasets.](https://arxiv.org/html/2602.11511v1/illustrative_figures/figure1.png)
A new framework addresses the challenges of integrating multi-modal datasets when information is missing or varies significantly between sources.
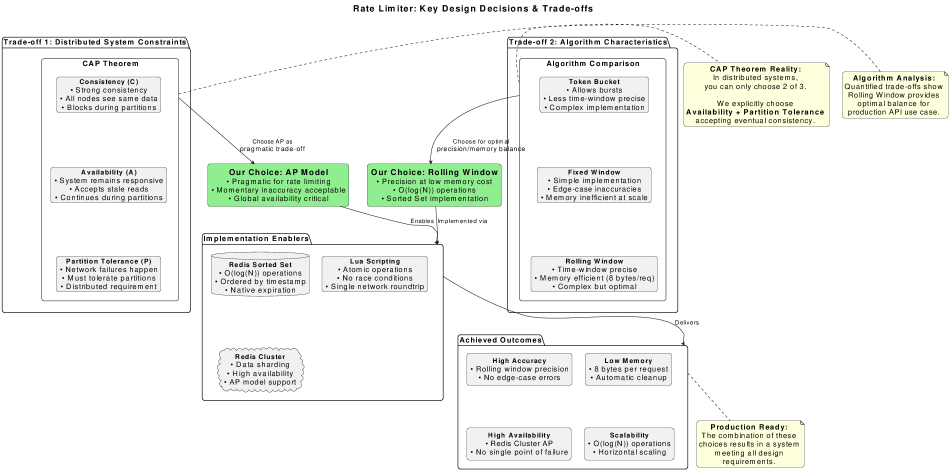
This review explores the challenges and solutions for building robust rate limiting systems capable of handling massive traffic spikes.