Quantum Codes Reimagined: Algebra’s Hidden Power
New research reveals a surprising link between abstract algebra and quantum error correction, offering a radically different foundation for building resilient quantum computers.
New research reveals a surprising link between abstract algebra and quantum error correction, offering a radically different foundation for building resilient quantum computers.
![The FrodoKEM hardware cryptographic processor embodies a holistic architectural design, integrating essential components to facilitate efficient and secure key encapsulation mechanisms [latex] KEM [/latex].](https://arxiv.org/html/2601.16500v1/figures/overall-architecture.png)
A new FPGA implementation dramatically accelerates the FrodoKEM post-quantum cryptographic algorithm, offering a practical path towards quantum-resistant security.
![The performance of the improved [latex]\mathsf{M}\text{-}\mathsf{DenSD}[/latex] decoder demonstrates its sensitivity to code parameters, suggesting that nuanced adjustments to these parameters are critical for optimizing its functionality.](https://arxiv.org/html/2601.15903v1/x7.png)
Researchers have developed a novel framework to identify communication channel codes without prior knowledge of their structure, paving the way for more robust and adaptable wireless systems.
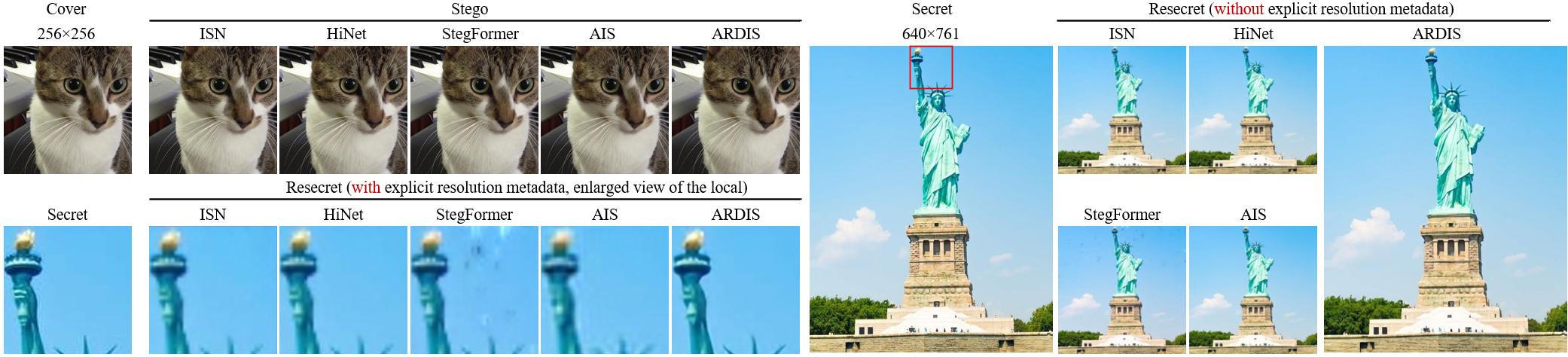
A new framework overcomes traditional constraints to embed secret images within cover images at any resolution, enabling high-fidelity recovery without prior knowledge.
Researchers have developed Tensor Reed-Muller codes and efficient decoding algorithms that promise to push the boundaries of reliable data transmission and storage.
![The algorithm strategically merges hierarchical subtree structures, prioritizing least common ancestors to maintain distance relationships; specifically, the least common ancestor of merged nodes reflects the higher ancestral position within the original trees, ensuring that the output embedding distance [latex]d\_{\alpha}(x,y)[/latex] is greater than or equal to the maximum of the individual subtree distances [latex]d\_{\alpha\_{1}}(u,x)[/latex] and [latex]d\_{\alpha\_{2}}(u,y)[/latex], thus preserving structural integrity during the merge process.](https://arxiv.org/html/2601.15470v1/x1.png)
New algorithms refine metric embedding techniques by intelligently handling outlier data, leading to improved approximations in hierarchical tree structures.
Breaking mirror symmetry in plasmonic crystals provides a novel pathway to transition between bound states in the continuum and high-quality quasi-bound states, enabling precise control over light-matter interactions.
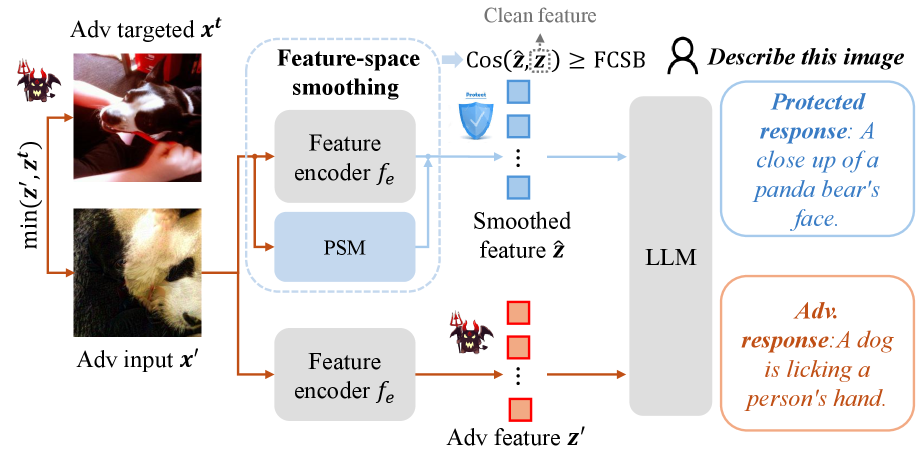
Researchers have developed a novel method to make image-and-text AI models more resilient to carefully crafted adversarial inputs designed to mislead them.
![The study demonstrates a precise correspondence between Next-to-Next-to-Leading Order (NNLO) differential decay distributions in [latex]b \to X_u \ell \bar{\nu}[/latex] and those derived from fitted [latex]W_i^{(2)}[/latex] distributions, with the analytic results for the [latex]\hat{q}^2[/latex] distribution serving as a foundational element for the fitting procedure.](https://arxiv.org/html/2601.15447v1/x15.png)
New calculations refine our understanding of how B mesons decay into leptons, improving the accuracy of tests for new physics.
This review explores how contractions of distributive quasi relation algebras impact their representability, offering new insights into conditions for finite representation.