Charging Ahead with Risk: Wireless Attacks Target EV Infrastructure
![Despite being misled by manipulated reports of [latex] \text{voltage} [/latex] at point A and [latex] \text{current} [/latex] at point B, including a false claim of charging at 1330V and 1330A when actually receiving 448V and 87A, VehicleX continued to charge normally, demonstrating a vulnerability exploitable through real-time, interactive manipulation of communicated demand responses.](https://arxiv.org/html/2601.15515v1/x6.png)
New research reveals a successful wireless Man-in-the-Middle attack against CCS EV charging stations, highlighting critical vulnerabilities in current security protocols.
![Despite being misled by manipulated reports of [latex] \text{voltage} [/latex] at point A and [latex] \text{current} [/latex] at point B, including a false claim of charging at 1330V and 1330A when actually receiving 448V and 87A, VehicleX continued to charge normally, demonstrating a vulnerability exploitable through real-time, interactive manipulation of communicated demand responses.](https://arxiv.org/html/2601.15515v1/x6.png)
New research reveals a successful wireless Man-in-the-Middle attack against CCS EV charging stations, highlighting critical vulnerabilities in current security protocols.
A new algorithm overcomes reconstruction artifacts in digital holographic microscopy, enabling accurate quantitative phase imaging of large tissue samples.
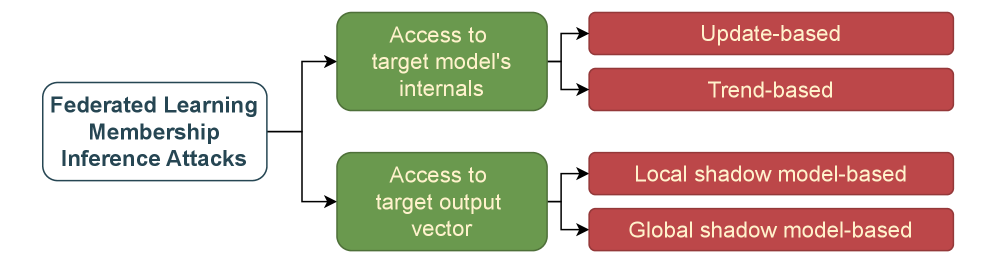
A new review reveals that determining if a specific record was used to train a model from tabular data is surprisingly difficult, despite growing concerns about data privacy.
A new system, Lattice, improves sequential prediction by intelligently blending learned patterns with established baselines, and quantifying its own uncertainty.
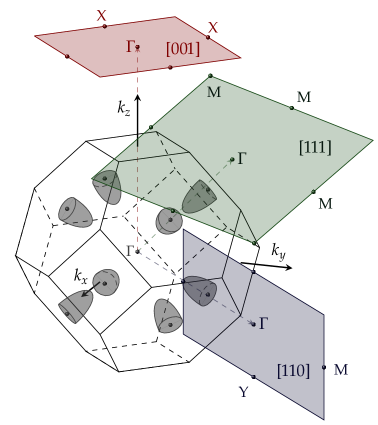
New research explores how manipulating the band structure of IV-VI semiconductor quantum wells can unlock the Quantum Anomalous Hall Effect without the need for external magnetic fields.
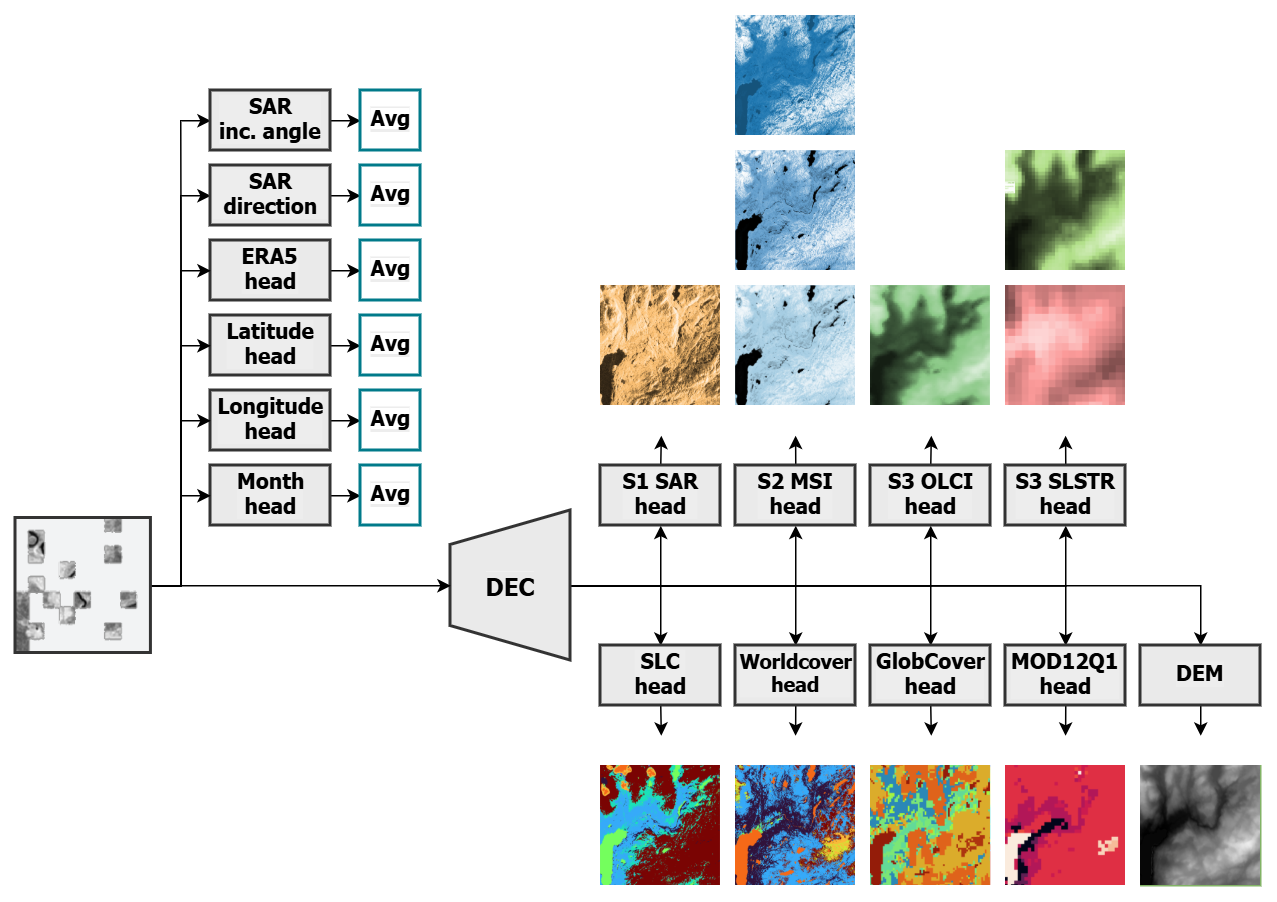
A new foundation model, THOR, promises to unlock greater insights from diverse Earth observation data, offering improved efficiency and adaptability for climate and societal applications.
![The distribution of spins within a three-state Potts model, subjected to coarse-graining via the diffusion equation with [latex]D_t/a^2 = 0.5[/latex], demonstrates a clear phase transition: at [latex]\beta = 0.30[/latex] the system remains symmetric, while at [latex]\beta = 0.40[/latex] it enters a broken phase, indicating the sensitivity of spin configurations to subtle changes in system parameters.](https://arxiv.org/html/2601.15720v1/figs/diffusion50b040l32.png)
New research utilizes a simplified model to chart the complex phase transitions of quark matter under conditions found in neutron stars and heavy ion collisions.
)))))[/latex] as a valid sequence.](https://arxiv.org/html/2601.15714v1/imgs/chatgpt.png)
New research reveals that even the most advanced language models struggle with fundamental tasks, highlighting a critical need for more robust evaluation metrics.
![The system explores domain-wall profiles within a [latex]Z(3)[/latex] symmetry, demonstrating how chiral backreaction influences their structure and evolution as a natural consequence of the system’s inherent decay.](https://arxiv.org/html/2601.15342v1/Fig4_PRL_pretty.png)
A new theoretical model details how the interplay of confinement and chiral symmetry breaking shapes phase transitions within a hidden sector governed by dark QCD.
A new framework leverages the power of locally-run artificial intelligence to identify security vulnerabilities hidden within Python code’s looping structures.