Author: Denis Avetisyan
This review analytically determines the probability of establishing a secure connection across multi-hop, layered networks commonly found in emerging non-terrestrial communication systems.
A novel analytical framework characterizes secure connection probability in heterogeneous Rician fading environments, resolving inconsistencies in prior research.
Ensuring secure communication in increasingly complex network topologies presents a fundamental challenge, particularly with the proliferation of non-terrestrial networks. This paper, ‘End-to-End Secure Connection Probability in MultiLayer Networks with Heterogeneous Rician Fading’, analytically derives a tractable, closed-form expression for the secure connection probability (SCP) in multi-hop relay routes operating under heterogeneous Rician fading conditions. The resulting formula not only improves SCP estimation accuracy-achieving a 1% error in most scenarios-but also provides analytical justification for coefficient calibration techniques used in prior work. By validating the framework against a real-world space-air-ground-sea integrated network dataset, this research demonstrates its ability to accurately capture observed security trends – but how can these findings be extended to dynamic network environments with intelligent jamming strategies?
Beyond Conventional Boundaries: Securing the Next Generation of Networks
Conventional cybersecurity measures, designed for static and localized terrestrial networks, struggle to encompass the inherent complexities of Non-Terrestrial Networks (NTNs). These networks, which integrate satellites, high-altitude platforms, and conventional ground infrastructure, introduce a level of dynamism and scale previously unseen. Traditional approaches, reliant on perimeter defenses and trusted nodes, are easily bypassed in NTNs due to the open and broadcast nature of wireless signals and the constantly shifting topology created by mobile nodes. Furthermore, the expansive geographic footprint of NTNs dramatically increases the attack surface, making it exponentially more difficult to monitor and secure all potential entry points. This necessitates a reimagining of security protocols to proactively address vulnerabilities unique to the multi-layered, highly mobile environment of these next-generation networks.
Non-Terrestrial Networks (NTNs), which ambitiously combine space-based satellites, airborne platforms like high-altitude pseudo-satellites, and conventional terrestrial infrastructure, present formidable security challenges stemming from their inherent complexity. Unlike the relatively predictable environments of ground-based networks, NTNs grapple with constantly shifting topologies as satellites and airborne elements move, introducing dynamic link failures and variable latency. Signal propagation is further complicated by the vast distances involved, atmospheric interference, and the Doppler effect, all of which can degrade signal quality and create opportunities for eavesdropping or manipulation. These factors necessitate security protocols that are resilient to these unique propagation characteristics and capable of adapting to the network’s ever-changing configuration – a significant departure from the established security models designed for static, terrestrial environments.
Conventional cybersecurity measures, designed for fixed terrestrial infrastructure, prove inadequate when applied to the inherently dynamic and open nature of Non-Terrestrial Networks. A transformative approach centers on physical layer security, which moves beyond encryption to exploit the fundamental characteristics of the wireless channel itself. This involves techniques like artificial noise injection, beamforming optimization, and secure waveform design to directly protect the signal from eavesdropping and manipulation. By addressing vulnerabilities at the signal level – considering factors like signal propagation, interference, and channel fading – physical layer security offers a proactive defense, making it exponentially harder for attackers to intercept or decode communications even before data reaches the application layer. This paradigm shift represents a crucial advancement in securing the expanding network landscape, providing a foundational layer of protection for future connectivity.
Unveiling the Hidden Threat: Modeling Eavesdropper Behavior
Non-terrestrial networks (NTNs) face a significant security challenge due to the potential presence of hidden eavesdroppers. These malicious nodes operate without the knowledge of legitimate network participants, meaning their locations and the characteristics of the communication channels they utilize are unknown. This lack of awareness prevents proactive security measures, such as beamforming nulling or encryption key negotiation tailored to specific eavesdropper threats. The inherent uncertainty regarding eavesdropper placement and channel conditions necessitates a probabilistic approach to security analysis, as deterministic defenses are impractical. Consequently, the performance of any security protocol must be evaluated under the assumption of worst-case eavesdropper scenarios or by statistically modeling their likely distribution.
A Homogeneous Poisson Point Process (HPPP) is employed to statistically model the random and independent distribution of eavesdroppers within the network. This process defines that the probability of finding k eavesdroppers within any given area A follows a Poisson distribution with rate \lambda A, where λ represents the average eavesdropper density. Crucially, the HPPP assumes a constant density λ across the entire network area and that the locations of individual eavesdroppers are independent of each other. This allows for analytical tractability in calculating metrics such as the probability of successful eavesdropping, the expected number of eavesdroppers within a transmission range, and the impact of network topology on security performance. By defining these statistical properties, the HPPP provides a quantifiable framework for evaluating the vulnerability of Non-Terrestrial Networks (NTNs) to passive attacks.
Accurate characterization of eavesdropper distribution is fundamental to quantifying the probability of successful eavesdropping attacks in Non-Terrestrial Networks (NTNs). By statistically modeling this distribution – specifically using a Homogeneous Poisson Point Process – security analysts can determine the expected number of eavesdroppers within a given area and their impact on signal interception. This understanding directly informs the calculation of key performance indicators, such as the probability of undetected eavesdropping and the expected information leakage. Consequently, this data is crucial for developing and evaluating effective countermeasures, including physical layer security techniques like artificial noise transmission, beamforming to avoid eavesdropper locations, and cryptographic solutions tailored to the specific characteristics of the eavesdropper distribution. Furthermore, assessing the sensitivity of system performance to variations in eavesdropper density allows for robust security design and resource allocation.
A Probabilistic Approach to Multi-Hop Security
Multi-hop relaying in Non-Terrestrial Networks (NTNs) addresses the limited transmission range of individual nodes by forwarding data through intermediate relays. While extending network coverage, each relay introduces a potential point of compromise, increasing overall system vulnerability. This is due to the necessity of establishing and maintaining secure links between each successive hop; an adversary compromising even a single relay can intercept or manipulate data in transit. Consequently, the security of the entire communication path is dependent on the weakest link, and the cumulative probability of a successful attack increases with each additional hop. Therefore, security protocols must account for the compounded risk inherent in multi-hop topologies and incorporate mechanisms to mitigate vulnerabilities at each relay node.
Secure Connection Probability (SCP) is a critical metric in multi-hop Decode-and-Forward (DF) relay networks, quantifying the probability that a confidential message remains secure throughout the entire relay path. Unlike single-hop systems, each DF hop introduces potential eavesdropping and decryption vulnerabilities; therefore, SCP is not simply a product of individual hop security. Calculating SCP requires modeling the cumulative effect of channel conditions and cryptographic parameters across all relays. Specifically, SCP considers the probability that each relay node correctly decodes the message, re-encrypts it with a new key, and forwards it securely, while simultaneously accounting for the probability that an eavesdropper intercepts and decrypts the information at any hop. SCP = \prod_{i=1}^{N} P_{secure,i}, where N is the number of hops and P_{secure,i} represents the security of the i-th hop, dependent on factors like signal-to-noise ratio and key management protocols. A low SCP indicates a high risk of compromised communication, necessitating robust security measures at each relay.
The Secure Connection Probability (SCP) in multi-hop Non-Terrestrial Networks (NTNs) is directly affected by the statistical characteristics of the wireless channel, most notably Rician fading. Rician fading, a composite of line-of-sight and multi-path components, introduces a varying signal strength and phase shift that impacts the reliability of key exchange and data transmission. Accurate modeling of Rician fading – typically defined by the K-factor representing the power ratio of the line-of-sight component to the scattered component – is therefore crucial for calculating SCP. The SCP is not simply a function of hop count but requires analysis of the probability that each hop maintains sufficient signal-to-noise ratio for secure communication, which is directly dependent on the channel’s fading distribution; specifically, the SCP calculation must account for the probability density function of the Rician-faded channel. P_{SCP} = \prod_{i=1}^{n} P_{Secure,i}(h_i), where h_i represents the channel gain of the ith hop and P_{Secure,i} is the probability of a secure connection over that link.
Analytical Tractability: The Power of Closed-Form Solutions
A closed-form expression for the Secure Connection Probability (SCP) provides a significant advantage in security assessment by eliminating the need for computationally intensive Monte Carlo simulations. Traditional security analysis often relies on simulating numerous channel realizations to estimate SCP, a process that demands substantial processing time and resources. Deriving an analytical solution, represented as a direct mathematical formula, allows for instantaneous calculation of SCP given specific channel parameters. This capability facilitates rapid prototyping, optimization, and real-time security monitoring, particularly within complex network architectures where numerous simulations would be impractical. The analytical tractability provided by a closed-form expression enables a deterministic and precise evaluation of security performance, bypassing the inherent statistical variability associated with simulation-based approaches.
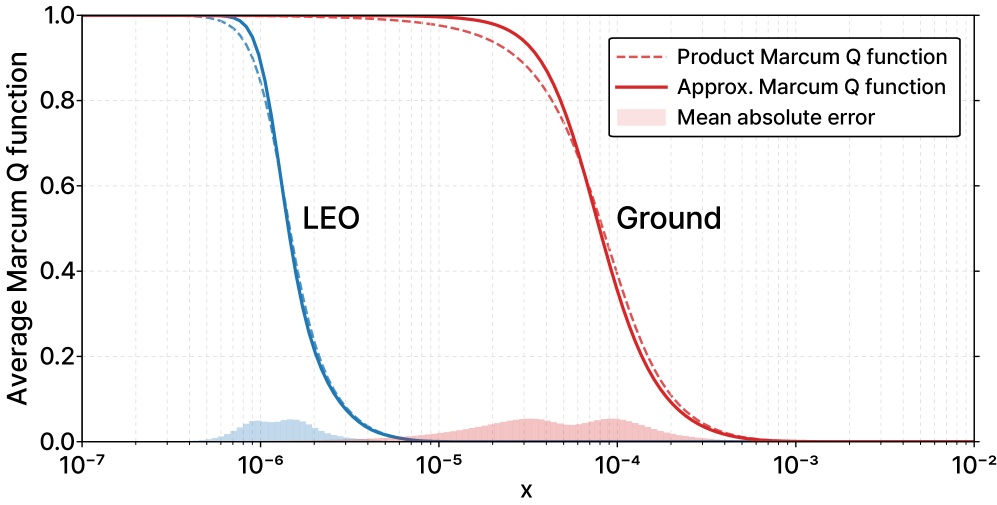
The analytical tractability of the Secure Connection Probability (SCP) derivation is fundamentally linked to the utilization of Heterogeneous Rician channels. These channels model wireless propagation where signal strength varies across network layers, exhibiting differing Line-of-Sight (LOS) components and fading characteristics. Specifically, a Rician distribution, parameterized by a non-negative real number K representing the power ratio of the LOS component to the scattered component, is applied to each layer. The heterogeneity arises because each layer possesses a unique K factor and associated fading variance, necessitating a layered approach to the overall channel model. Accurately characterizing these per-layer Rician parameters is crucial, as the combined effect of these heterogeneous fading distributions directly impacts the SCP calculation and ultimately determines the reliability of the security assessment.
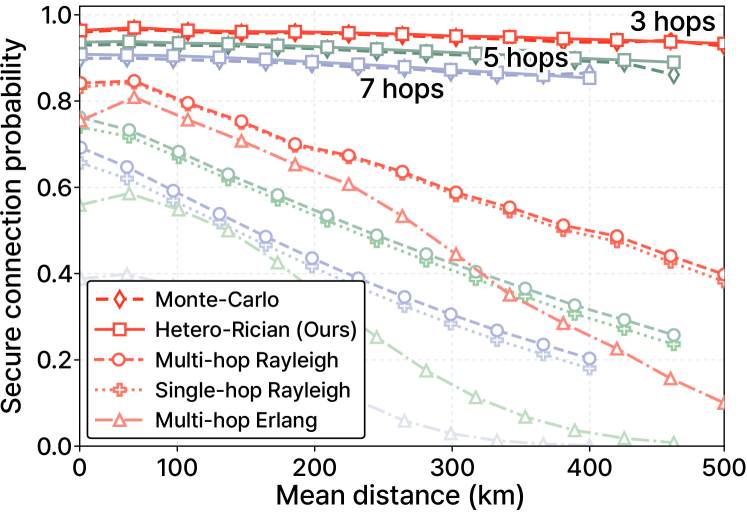
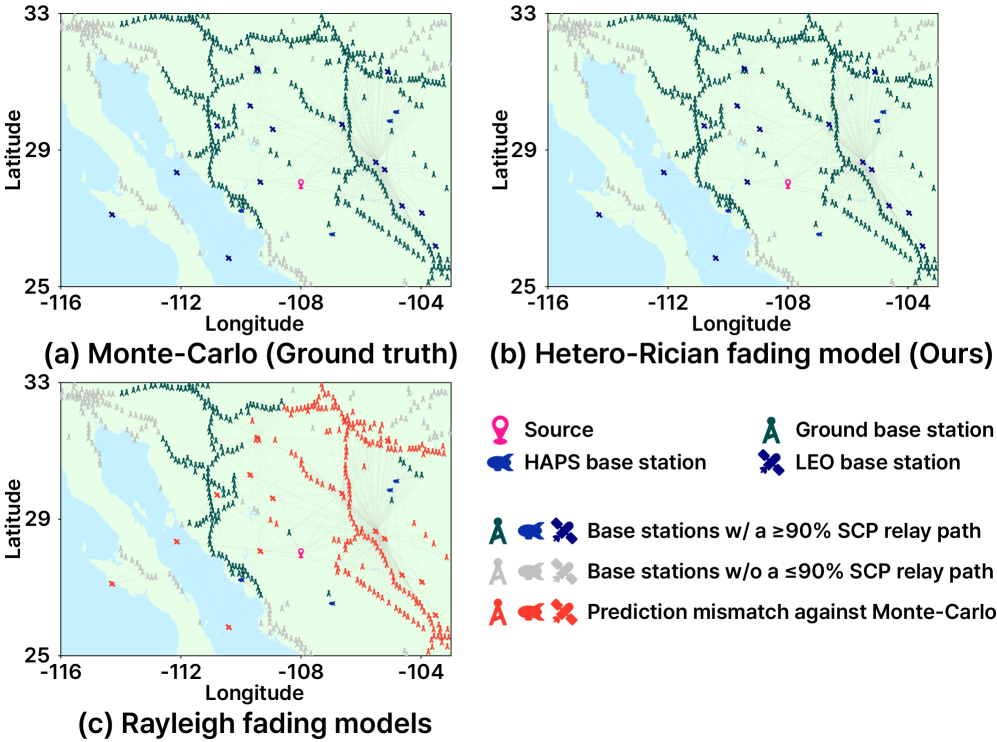
The accuracy of the proposed analytical framework was validated through comparison with Monte Carlo simulations across multiple network layers, yielding a mean absolute error of ≤ 0.06. This metric quantifies the average difference between the predicted Secure Connection Probability (SCP) from the analytical model and the SCP obtained via simulation. Critically, performance is further enhanced when focusing on regions where SCP is ≥ 90%, exhibiting a reduced mean absolute error of ≤ 0.034. This demonstrates the framework’s high degree of fidelity, particularly in scenarios demanding robust security performance.
Performance evaluations indicate that the proposed approach exhibits a significantly reduced Secure Connection Probability (SCP) gap compared to the highest-performing baseline scheme utilizing Rayleigh fading channels. Specifically, the SCP gap is 4.5 times smaller, demonstrating a substantial improvement in accuracy when predicting secure connection establishment. This reduction in gap size signifies that the proposed method more closely aligns with the actual SCP achieved in practical heterogeneous network deployments, offering a more reliable metric for security assessment and optimization than Rayleigh-based alternatives.
The analytical rigor demonstrated in characterizing secure connection probability within heterogeneous networks echoes a pursuit of fundamental elegance. This work moves beyond simplified models, acknowledging the complexities of Rician fading and multi-hop relaying to deliver a more accurate representation of real-world conditions. It is reminiscent of Stephen Hawking’s observation, “Intelligence is the ability to adapt to any environment.” The study’s adaptability-its capacity to refine understanding through meticulous modeling-is not merely technical proficiency, but a sign of deep comprehension. This pursuit of accuracy, while complex, ultimately creates a system that is more durable and comprehensible, mirroring the beauty found in well-designed systems.
Beyond the Horizon
The characterization of secure connection probability, even within this analytically tractable framework, feels less like a destination and more like a refinement of the questions. The present work illuminates discrepancies in prior models, revealing the subtle, yet critical, influence of heterogeneous Rician fading in multi-hop, non-terrestrial networks. However, true elegance demands acknowledging what remains unsaid. The assumption of static topologies, while useful for initial analysis, feels increasingly contrived. Real networks breathe, nodes fail, and links fluctuate – a dynamic complexity that will necessitate stochastic geometry beyond current boundaries.
Furthermore, the focus on physical layer security, while essential, exists in a vacuum. An interface should be intuitively understandable without extra words, and so too should security seamlessly integrate with higher-layer protocols. Future explorations must consider the interplay between secure connection probability and network coding, cooperative jamming, or even the subtle art of misinformation – layers of deception that complicate the very notion of a ‘secure’ connection.
Refactoring is art, not a technical obligation, and so it is with this field. The pursuit of ever-more-realistic fading models, while valuable, risks obscuring fundamental principles. A more fruitful direction might lie in identifying the minimal complexity required to achieve a given security level – a quest for essential truth, stripped of unnecessary ornamentation. The horizon beckons, not with simpler answers, but with more thoughtfully framed questions.
Original article: https://arxiv.org/pdf/2602.07959.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- All Skyblazer Armor Locations in Crimson Desert
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- All Shadow Armor Locations in Crimson Desert
- Marni Laser Helm Location & Upgrade in Crimson Desert
- One Piece Chapter 1180 Release Date And Where To Read
- All Helfryn Armor Locations in Crimson Desert
- All Golden Greed Armor Locations in Crimson Desert
- All Icewing Armor Locations in Crimson Desert
- How to Beat Stonewalker Antiquum at the Gate of Truth in Crimson Desert
- Legendary White Lion Necklace Location in Crimson Desert
2026-02-11 04:36