Author: Denis Avetisyan
As quantum computing looms, this review explores the practical challenges of integrating post-quantum cryptography into the low-power wireless networks that power our everyday devices.
This paper analyzes the energy overhead of post-quantum key establishment in Bluetooth Low Energy Personal Area Networks and proposes link-layer optimizations to minimize consumption.
The looming threat of quantum computing necessitates a transition to post-quantum cryptography, yet integrating these solutions into resource-constrained wireless networks presents significant challenges. This paper, ‘On the Energy Cost of Post-Quantum Key Establishment in Wireless Low-Power Personal Area Networks’, investigates the energy overhead associated with post-quantum key exchange in Bluetooth Low Energy networks. Results demonstrate that communication costs frequently dominate the energy budget, exceeding cryptographic computation, highlighting the need for coordinated protocol and link-layer optimization. Can practical, energy-efficient quantum-resistant communication be achieved in personal area networks without compromising performance or usability?
The Inevitable Shift: Quantum Threats to Cryptographic Foundations
The bedrock of modern digital security, public-key cryptography-specifically algorithms like RSA and Elliptic Curve Cryptography-faces a substantial threat from the advent of quantum computing. These systems rely on the mathematical difficulty of certain problems, such as factoring large numbers or solving the discrete logarithm problem, which classical computers struggle with. However, Shor's\, algorithm, a quantum algorithm, can efficiently solve these problems, effectively breaking the encryption that protects sensitive data. This isn’t a theoretical concern for the distant future; the increasing development of quantum computing capabilities suggests a growing possibility of decryption of previously secure communications, impacting everything from financial transactions and healthcare records to governmental communications and intellectual property. Consequently, the confidentiality of data currently protected by these widely used cryptographic methods is at risk, necessitating a swift transition to quantum-resistant alternatives.
The potential for a “Harvest Now, Decrypt Later” attack underscores a significant and often overlooked vulnerability in contemporary digital security. This strategy involves malicious actors collecting encrypted data today, anticipating the future availability of quantum computers capable of breaking current encryption standards like RSA and ECC. Even if fully functional, large-scale quantum computers are years away, the long lifespan of sensitive data – financial records, intellectual property, or personal communications – means that previously secure information could be retroactively compromised. Therefore, proactive adoption of post-quantum cryptography, algorithms resistant to both classical and quantum attacks, is not merely a future consideration, but a present-day necessity to safeguard data longevity and prevent a cascade of breaches once quantum computing power matures. This necessitates a shift in cryptographic agility, allowing systems to seamlessly transition to new, quantum-resistant standards before it’s too late.
The proliferation of Wireless Personal Area Networks and the Internet of Things has created an expansive, interconnected landscape critically dependent on public-key cryptography for secure communication. However, this very reliance introduces significant vulnerabilities as the advent of quantum computing looms. Devices ranging from wearable health trackers to smart home appliances and industrial sensors currently employ encryption standards susceptible to decryption by sufficiently powerful quantum computers. The sheer scale of these networks – often encompassing billions of devices with limited processing power and infrequent security updates – exacerbates the risk, making widespread, proactive upgrades essential. Addressing this threat requires a fundamental shift towards quantum-resistant cryptographic algorithms, not as a future precaution, but as an immediate necessity to safeguard the confidentiality and integrity of data transmitted across these increasingly ubiquitous wireless networks.
Forging Resilience: The Emergence of Post-Quantum Cryptography
Post-Quantum Cryptography (PQC) addresses the potential threat posed by quantum computers to currently deployed public-key cryptosystems. Existing algorithms, such as RSA and ECC, rely on the computational hardness of mathematical problems that are efficiently solvable by quantum algorithms, specifically Shor’s algorithm. PQC aims to develop and implement cryptographic algorithms that are believed to be secure against attacks by both classical computers and known quantum algorithms. These algorithms are based on different mathematical problems, including lattice-based cryptography, code-based cryptography, multivariate cryptography, and hash-based signatures, offering alternative security foundations not vulnerable to these quantum attacks. The development of PQC is crucial to maintaining the confidentiality and integrity of digital communications and data in a future where quantum computers are a reality.
The National Institute of Standards and Technology (NIST) initiated a Post-Quantum Cryptography (PQC) Standardization process in 2016 to evaluate and select cryptographic algorithms resistant to attacks from quantum computers. This multi-round process involved public submissions, rigorous analysis, and testing of candidate algorithms. The goal is to develop a new generation of cryptographic standards that can replace currently used algorithms susceptible to quantum attacks, specifically those based on RSA and Elliptic Curve Cryptography. The standardization process prioritizes algorithms demonstrating both strong security and practical performance characteristics, including key generation, encryption, and decryption speeds. Successful algorithms will be published as Federal Information Processing Standards (FIPS), facilitating interoperability and broad adoption across government and private sector implementations, and mitigating the risk of a cryptographic transition crisis.
CRYSTALS-Kyber is a Module-Lattice-Based Key Encapsulation Mechanism (KEM) selected as a primary algorithm in the NIST Post-Quantum Cryptography Standardization process. Its design centers on the hardness of solving the Module Learning With Errors (MLWE) problem over structured lattices. This approach yields a KEM offering strong security assurances against both classical and quantum attacks. Notably, Kyber distinguishes itself through comparatively small key and ciphertext sizes, and efficient software and hardware implementations, resulting in favorable performance characteristics for a range of applications including TLS and VPN protocols. The algorithm operates on rings, enabling optimizations that contribute to its speed and reduced resource usage without compromising security levels.
Securing the Periphery: Post-Quantum Key Exchange for BLE
Bluetooth Low Energy (BLE) devices are increasingly prevalent in Internet of Things (IoT) deployments, creating a significant attack surface vulnerable to future quantum computing threats. Current public-key cryptography utilized for BLE pairing and encryption, such as Elliptic Curve Diffie-Hellman (ECDH), is susceptible to algorithms like Shor’s algorithm when sufficiently powerful quantum computers become available. Integrating Post-Quantum Key Exchange (PQKE) protocols into BLE stacks addresses this vulnerability by replacing classically vulnerable algorithms with quantum-resistant alternatives. These PQKE protocols, based on mathematical problems believed to be intractable for both classical and quantum computers, allow for secure key establishment, ensuring the confidentiality and integrity of BLE communications even in a post-quantum cryptographic landscape. This proactive approach mitigates long-term security risks and preserves the trustworthiness of BLE-enabled IoT ecosystems.
Effective implementation of post-quantum key exchange within Bluetooth Low Energy (BLE) necessitates careful attention to protocol limitations. The Attribute Protocol Maximum Transmission Unit (ATT MTU) defines the largest packet size, typically ranging from 23 to 517 bytes, which constrains the size of exchanged keys. Additionally, the Link Layer Protocol Data Unit (PDU) introduces overhead due to addressing and control information, further reducing the effective payload capacity. These constraints require developers to consider key encapsulation mechanisms that produce compact ciphertexts or to employ fragmentation and reassembly techniques, which introduce additional overhead and potentially increase airtime usage. Optimizing key sizes and minimizing PDU overhead are crucial for achieving efficient and reliable post-quantum security within the bandwidth and energy limitations of BLE devices.
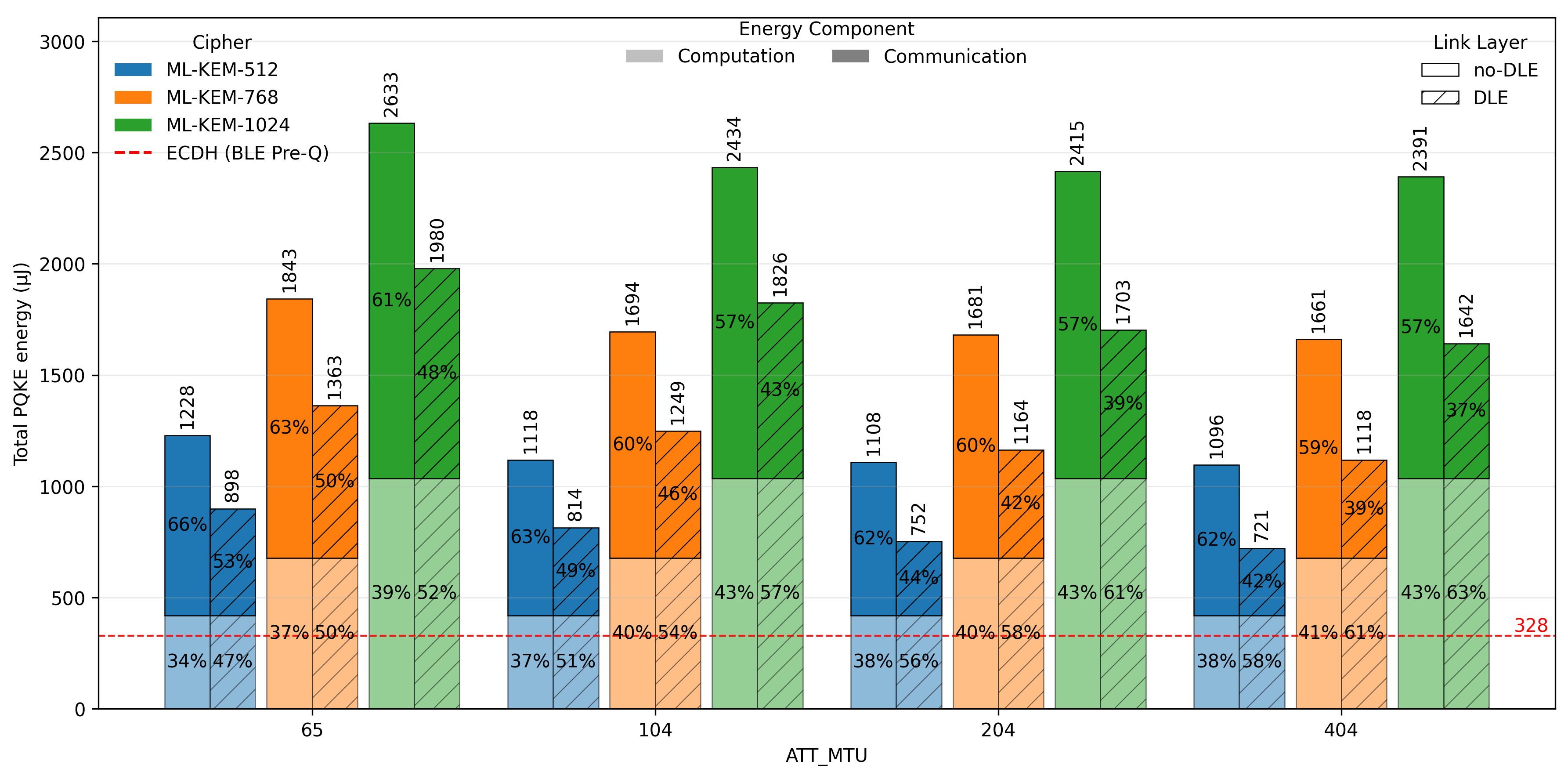
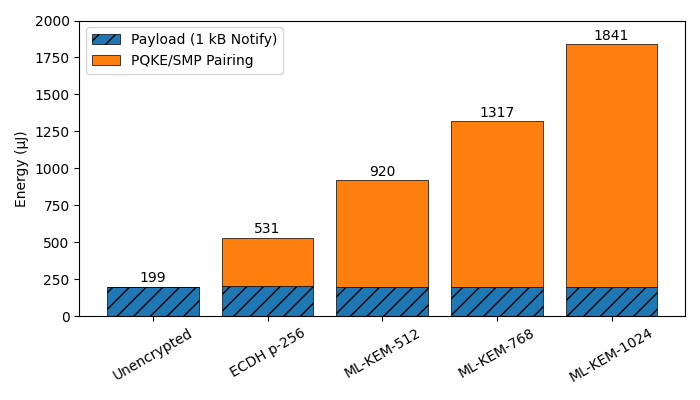
Due to the limitations of Bluetooth Low Energy (BLE) packet sizes, accommodating larger keys generated by Post-Quantum Key Exchange protocols may necessitate fragmentation. This involves dividing the key into smaller segments for transmission, increasing airtime and potentially impacting network performance. Recent research demonstrates the feasibility of post-quantum key establishment within low-power personal area networks (PANs) utilizing BLE, with measured total energy consumption ranging from 721 to 2633 μJ. This energy usage is dependent on the chosen security level of the post-quantum algorithm and the specific BLE configuration parameters, including connection interval and modulation scheme.
Performance Under Scrutiny: Embedded Systems and Quantum-Safe Algorithms
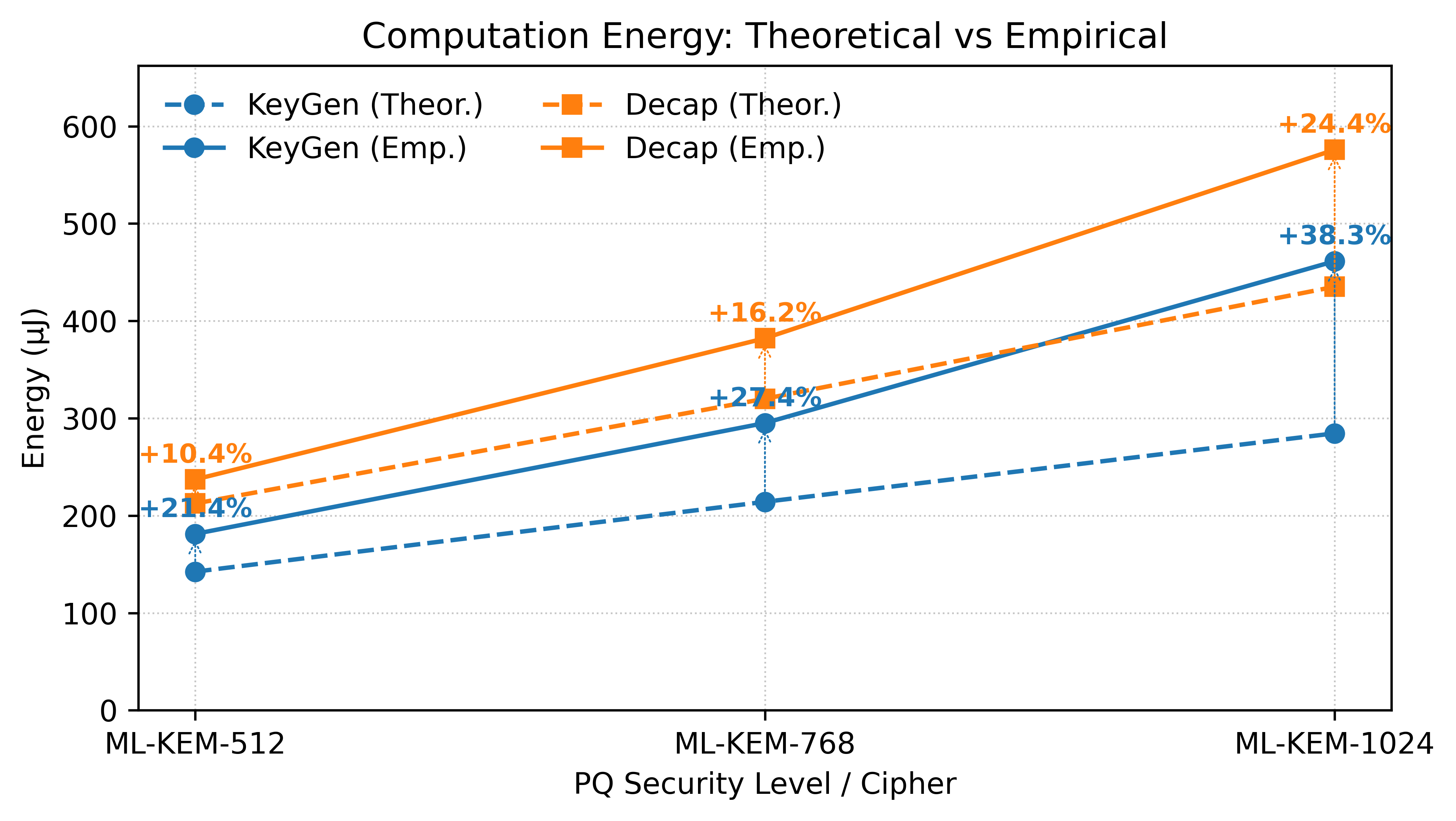
Evaluating the computational cost of post-quantum cryptography on embedded systems necessitates rigorous benchmarking on platforms like the Arm Cortex-M4 and nRF52840. These devices, commonly found in IoT and edge computing applications, present unique resource constraints-limited processing power, memory, and energy-that significantly impact algorithm performance. Benchmarking allows developers to move beyond theoretical complexity and determine the practical feasibility of implementing these crucial security protocols in real-world deployments. Specifically, it reveals bottlenecks and guides optimization efforts, ensuring that post-quantum algorithms can operate efficiently within the limitations of embedded hardware, thereby safeguarding future communications against emerging quantum threats. The process moves beyond simply confirming functionality to quantifying the actual resource demands of each algorithm, facilitating informed decisions regarding their suitability for various embedded applications.
The pqm4 Benchmark offers a standardized methodology for gauging the computational demands of post-quantum cryptographic algorithms on embedded systems. This framework meticulously tracks performance metrics, most notably cycle counts, providing developers with actionable insights for optimization. By quantifying the resources required for key encapsulation and digital signature operations, the benchmark facilitates targeted improvements to code efficiency and algorithm selection. Developers can utilize these metrics to refine implementations, ensuring they operate within the stringent power and processing limitations typical of resource-constrained devices. The resulting data empowers informed decisions regarding algorithm suitability and enables the creation of secure, efficient cryptographic solutions for embedded applications.
Optimizing post-quantum cryptographic implementations on embedded systems demands careful consideration of both performance and energy efficiency, and the integration of efficient real-time operating systems, such as Zephyr RTOS, plays a crucial role. Detailed profiling using tools like the Nordic Power Profiler Kit II allows developers to pinpoint energy-intensive operations and refine code for minimal consumption. Recent benchmarking demonstrates a significant correlation between key size and energy expenditure; for instance, the ML-KEM-512 algorithm achieves a PQKE Energy of 721 μJ, establishing a comparative baseline. However, the more secure ML-KEM-1024 implementation requires considerably more energy, reaching 2633 μJ – the highest measured cost in this study – highlighting the trade-offs between security levels and resource utilization in constrained environments.
Looking Ahead: Secure Mesh Networks and the Root of Trust
The proliferation of interconnected devices within large-scale Internet of Things deployments necessitates a proactive approach to security, particularly as quantum computing capabilities advance. Current encryption standards, while presently secure, face potential vulnerabilities with the advent of sufficiently powerful quantum computers, demanding a transition to post-quantum cryptography. Extending these novel security measures to Bluetooth Low Energy (BLE) Mesh networks is especially critical, given their widespread use in smart homes, industrial automation, and healthcare. BLE Mesh’s unique characteristics – including its many-to-many communication topology and resource constraints – present distinct challenges for implementing post-quantum algorithms. Successfully integrating these protections will not only safeguard sensitive data transmitted across these networks, but also ensure the continued reliability and trustworthiness of the increasingly pervasive IoT ecosystem, preventing large-scale disruption and maintaining user confidence.
Embedded devices, increasingly prevalent in IoT networks, often lack robust security foundations, making them vulnerable to physical and digital attacks. Integrating OpenTitan, a fully open-source silicon root of trust, addresses this challenge by providing a verifiable and customizable hardware security anchor. This approach establishes a secure boot process, protects cryptographic keys, and enables attestation – verifying the device’s integrity and authenticity. By openly publishing the design and enabling community review, OpenTitan fosters transparency and allows for continuous improvement, mitigating the risk of hidden vulnerabilities common in proprietary solutions. Implementing such a root of trust significantly strengthens the overall security posture of embedded systems and bolsters confidence in the integrity of connected devices within large-scale deployments.
The implementation of standardized secure protocols-specifically DTLS 1.3 paired with QUIC and MQTT-offers a robust pathway to end-to-end encryption and authentication, safeguarding data confidentiality and integrity across interconnected devices. Recent investigations highlight the significant impact of link-layer optimization on energy efficiency; unoptimized Post-Quantum Key Encapsulation (PQKE) configurations reveal that communication costs constitute the majority-between 57% and 63%-of total energy expenditure. However, through strategic link-layer adjustments, energy consumption can be substantially reduced, achieving savings of 25-34%, and thus enabling more sustainable and scalable deployments of secure mesh networks, particularly crucial for the proliferation of large-scale Internet of Things (IoT) ecosystems.
The pursuit of secure communication, even in the face of quantum threats, inevitably introduces complexity. This study highlights the delicate balance between cryptographic strength and energy efficiency within constrained wireless networks. It’s a system adapting to a changing landscape, mirroring the inevitable decay all systems face. As Ken Thompson observed, “Debugging is twice as hard as writing the code in the first place. Therefore, if you write the code as cleverly as possible, you are, by definition, not smart enough to debug it.” This resonates with the challenges detailed in the paper; optimizing link-layer protocols for post-quantum cryptography isn’t merely implementation, but a constant process of refinement as the system matures and reveals its vulnerabilities over time. The energy cost analysis represents steps towards graceful aging, a necessary evolution in the face of persistent threats.
What Lies Ahead?
The integration of post-quantum cryptography into the fabric of low-power wireless networks is not merely a technological challenge, but an acknowledgment of entropy. Systems learn to age gracefully; they do not resist the inevitable shift in cryptographic landscapes. This work demonstrates feasibility, yet the true cost isn’t measured solely in energy expenditure, but in the persistent negotiation between security and efficiency. Further exploration must address the dynamic interplay between key sizes, communication frequencies, and the inherent limitations of constrained devices.
The optimization strategies presented here represent a localized mitigation, a slowing of decay. However, the broader question remains: how do these systems adapt to evolving threats without demanding constant, disruptive overhauls? Focusing on adaptable protocols-those that prioritize resilience through fragmentation and clever link-layer management-may prove more valuable than striving for absolute cryptographic perfection. Sometimes observing the process is better than trying to speed it up.
Ultimately, the longevity of these networks will depend not on eliminating vulnerabilities, but on accepting them as an intrinsic property of complex systems. The field should shift toward quantifying the rate of decay, rather than attempting to defy it. The energy cost of security is significant, yes, but the cost of inflexible systems, destined for premature obsolescence, is far greater.
Original article: https://arxiv.org/pdf/2602.18708.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- All Skyblazer Armor Locations in Crimson Desert
- All Shadow Armor Locations in Crimson Desert
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- Marni Laser Helm Location & Upgrade in Crimson Desert
- Best Bows in Crimson Desert
- All Helfryn Armor Locations in Crimson Desert
- All Golden Greed Armor Locations in Crimson Desert
- How to Craft the Elegant Carmine Armor in Crimson Desert
- Keeping Large AI Models Connected Through Network Chaos
- One Piece Chapter 1179 Preview: The Real Imu Arrives in Elbaf
2026-02-24 09:03