Author: Denis Avetisyan
Researchers have developed a novel method to assess the effectiveness of logic locking techniques against malicious modification by analyzing the statistical distribution of logic cone structures.

This work leverages K-cut enumeration and NPN Boolean equivalence to quantify the indistinguishability of designs with and without logic locks, enhancing resilience against chosen plaintext attacks.
Despite growing interest in logic locking as a hardware security countermeasure, practical implementations have consistently proven vulnerable to attack, raising concerns about long-term efficacy. This paper, ‘Evaluating the Indistinguishability of Logic Locking using K-Cut Enumeration and Boolean Matching’, introduces a novel evaluation methodology based on comparing distributions of k-cuts-representations of logic cones-to assess the indistinguishability of locked designs. Our results demonstrate up to 92% accuracy in identifying locked circuits, even after resynthesis, suggesting that current logic locking techniques often fail to provide the strong security guarantees of indistinguishability. Can this approach pave the way for more robust and provably secure hardware IP protection schemes?
The Erosion of Design Integrity in Modern Circuits
As integrated circuits amass billions of transistors, their inherent complexity inadvertently creates new avenues for malicious actors. This escalating intricacy makes reverse engineering – the process of deconstructing a chip to understand its design – increasingly feasible, albeit computationally intensive. Counterfeiters exploit these vulnerabilities to clone designs, fabricate unauthorized copies, or introduce backdoors for espionage or sabotage. Traditional protective measures, such as physical security and encryption, are proving insufficient against sophisticated attacks leveraging advanced imaging techniques and automated analysis tools. The sheer volume of data within modern chips, coupled with the subtle nuances of circuit behavior, allows determined attackers to gradually piece together the original design, bypassing conventional safeguards and posing a significant threat to intellectual property and national security.
The escalating sophistication of hardware attacks renders conventional semiconductor protection schemes increasingly inadequate. Historically, security relied heavily on obscurity and reactive measures – addressing vulnerabilities after they were discovered. However, determined attackers, equipped with advanced reverse engineering tools and techniques like deprocessing and fault injection, routinely bypass these defenses. This necessitates a paradigm shift towards proactive security strategies integrated directly into the chip design process. Rather than simply reacting to threats, modern approaches focus on building inherent resilience, obfuscating critical circuit functions, and actively misleading potential adversaries. Such techniques aim to raise the cost and complexity of attack to a point where it becomes economically unfeasible, safeguarding intellectual property in an era of pervasive hardware insecurity.
Logic locking presents a compelling approach to safeguarding semiconductor intellectual property by intentionally embedding obfuscated logic within a circuit’s design. However, the technique’s success isn’t simply about adding complexity; a truly secure implementation demands that the locked design remains functionally – and crucially, performance-wise – indistinguishable from its unlocked counterpart. Attackers often leverage statistical analysis and machine learning to detect even subtle differences in power consumption, timing, or signal behavior, revealing the presence of locking mechanisms. Therefore, achieving strong indistinguishability requires sophisticated key management, careful logic partitioning, and rigorous verification to ensure that the introduced obfuscation doesn’t create exploitable vulnerabilities or degrade the circuit’s operational characteristics, making it a constant arms race between designers and those seeking to reverse engineer or counterfeit integrated circuits.
The practical deployment of logic locking, a technique for shielding integrated circuit designs, isn’t simply about obfuscation; it necessitates rigorous validation to guarantee security isn’t compromised. Assessing the resilience of a locked design demands more than just basic functional verification. Researchers are developing sophisticated attack algorithms-like Boolean satisfiability (SAT) solvers and machine learning techniques-to actively probe for weaknesses in the locking mechanism. These attacks aim to bypass the protection and reconstruct the original, unprotected circuit. Consequently, a robust evaluation framework must encompass a diverse range of attacks, measuring metrics like the time and resources required for successful unlocking, and the percentage of designs that remain secure under sustained assault. The ultimate goal is to establish quantifiable security guarantees, ensuring that the modified circuit genuinely resists reverse engineering and maintains its intended functionality even when subjected to determined adversaries.
Deconstructing Circuit Behavior with Cut Distributions
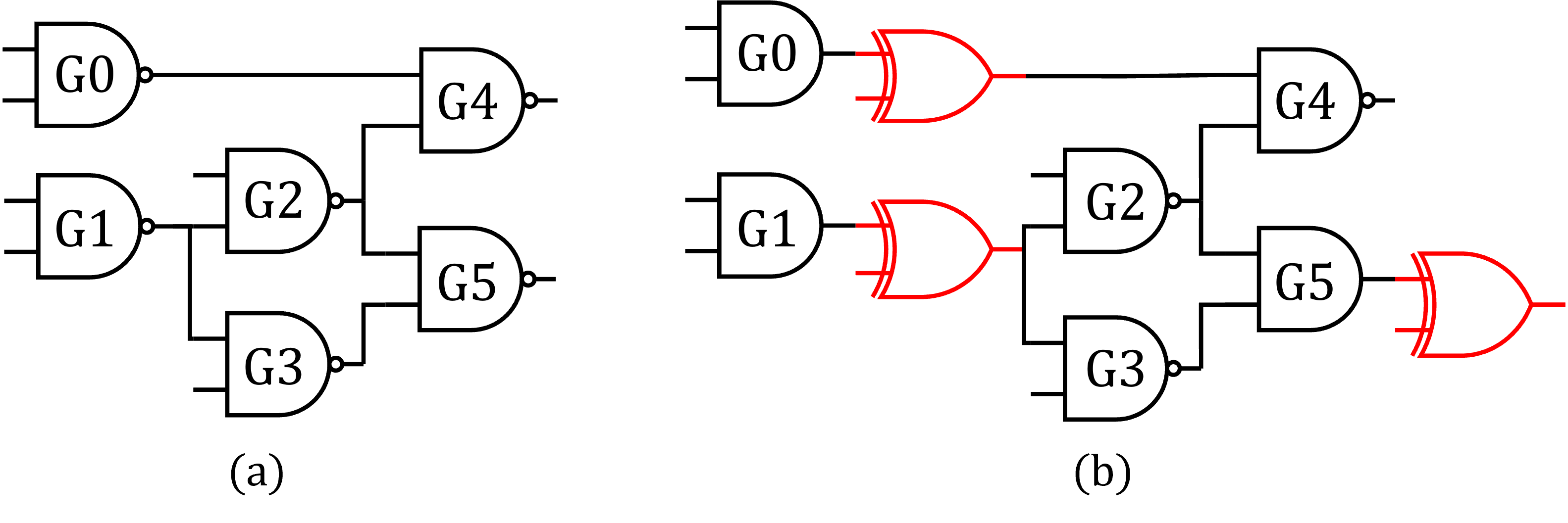
K-Cut Enumeration is a methodology for comprehensively analyzing digital circuit logic by systematically identifying and evaluating all possible logic cones with a specified number of inputs, denoted as ‘k’. A logic cone consists of all gates connected to a particular input or set of inputs. By examining each k-cut, the technique provides a detailed view of how signals propagate and interact within the circuit. The process involves defining all combinations of ‘k’ inputs and then tracing the logic gates influenced by those inputs, creating a representative subset of the circuit’s functionality for analysis. Varying ‘k’ allows for the assessment of both simple and complex circuit behaviors, offering a granular understanding of the design’s structure and interconnections.
Comparing the cut distributions of locked and unlocked circuit designs provides a quantifiable method for assessing the extent of modifications introduced during the locking process. A cut distribution represents the frequency of each unique cut within a circuit, and discrepancies between locked and unlocked designs indicate alterations to the original logic. Larger differences in cut distributions correlate with more substantial modifications, suggesting a greater difficulty in reverse engineering the original, unlocked functionality. This approach allows for a numerical evaluation of obfuscation strength, moving beyond qualitative assessments of circuit complexity, and enabling a comparative analysis of different locking techniques based on their impact on the cut distribution profile.
Jaccard Set Similarity provides a quantifiable method for comparing cut distributions by calculating the size of the intersection divided by the size of the union of the cut sets. This results in a similarity score ranging from 0 to 1, where 1 indicates identical cut distributions and 0 indicates no overlap. Specifically, given two cut distributions, A and B, the Jaccard Similarity is calculated as |A \cap B| / |A \cup B|. This metric allows for the objective comparison of circuit logic structures, enabling the determination of the degree of modification between different designs and facilitating the assessment of reverse engineering difficulty based on the extent of structural similarity.
NPN Boolean Equivalence enhances circuit similarity analysis by normalizing for common circuit transformations, specifically negation and input permutation. This normalization process allows for accurate comparison of circuit structures even when these transformations have been applied. Evaluations on benchmark circuits demonstrate that utilizing the top-10 and top-20 most frequent 8-cuts, as determined by NPN Boolean Equivalence, achieves an average accuracy of up to 92% in identifying locked designs – those modified from an original, unlocked counterpart. This metric provides a robust method for quantifying structural similarity despite potentially obfuscating transformations.

Testing the Resilience of Logic Locking Against Sophisticated Adversaries
Chosen Plaintext Attacks (CPAs) represent a threat model where an adversary actively selects and submits specific input values to a locked hardware design to observe its resulting output. This allows the adversary to analyze the correlation between inputs and outputs, effectively reverse-engineering the locking mechanism and potentially identifying the original, unlocked functionality. CPAs are considered a powerful attack vector because they do not rely on random input patterns; instead, the adversary strategically crafts inputs to maximize information gain about the internal logic. The effectiveness of a logic locking scheme against CPAs is therefore a key metric in evaluating its security, as a vulnerable design will reveal its underlying structure when subjected to targeted input analysis.
Oracle-less attacks pose a substantial security risk to logic-locked circuits because they circumvent the typical requirement for an attacker to query the circuit with inputs and observe the corresponding outputs – an “oracle”. These attacks rely solely on the circuit’s external behavior and do not necessitate knowledge of internal signals or the ability to differentiate between correct and incorrect outputs. This approach significantly broadens the attack surface, as it removes dependencies on potentially detectable probing or side-channel analysis techniques used to access oracle information. Consequently, evaluating logic locking schemes against oracle-less attacks provides a more realistic assessment of their resilience in practical adversarial scenarios.
The efficacy of logic locking techniques – specifically, Trojan-based Random Logic Locking (TRLL), Split-Function Logic Locking with High Don’t-Care count (SFLL-HD), LUT Lock, and MUX Lock – is determined through evaluation against sophisticated attack models like Chosen Plaintext Attacks and Oracle-less Attacks. These attacks simulate advanced adversaries capable of targeting vulnerabilities in locked designs. Performance is quantitatively measured using the ISCAS’85 Benchmark Suite, allowing for comparative analysis of each technique’s resilience. Results indicate an overall accuracy of 84% achieved with 4-cuts, a similarity score of 54% with reasonable accuracy using 6-cuts, and a highest accuracy with a similarity score of 29% observed using 8-cuts, providing metrics for assessing the strength of each logic locking implementation.
Evaluation of logic locking techniques was conducted using the ISCAS’85 Benchmark Suite, a widely adopted set of circuits for design and security validation. Results indicate an overall accuracy of 84% was achieved when employing a 4-cut strategy. Further analysis with 6-cuts yielded a similarity score of 54% while maintaining reasonable accuracy. The highest accuracy was observed with an 8-cut strategy, resulting in a similarity score of 29%.

The pursuit of secure systems, as detailed in this evaluation of logic locking techniques, echoes a fundamental truth about all engineered creations: they are perpetually subject to refinement through exposure. This paper’s method of assessing indistinguishability via k-cut enumeration and Boolean matching directly addresses the inevitable emergence of vulnerabilities-the ‘incidents’ that mark a system’s progression towards maturity. As Alan Turing observed, “Sometimes people who are unhappy tend to look at the world as if there is something wrong with it.” Similarly, security evaluations aren’t about proving perfection, but rather acknowledging potential flaws and iteratively strengthening the system against chosen plaintext attacks. The process of identifying vulnerabilities through rigorous analysis, much like the enumeration of kk-cuts, represents a step toward graceful aging, not a declaration of inherent failure.
What Lies Ahead?
The pursuit of indistinguishability in logic locking, as explored within this work, reveals a fundamental truth about defensive strategies: they merely shift the landscape of attack, not eliminate it. Evaluating security through the distribution of logic cones offers a granular view, a temporary stay against the inevitable erosion of confidence. The method relies on Boolean equivalence, a snapshot of structural similarity, but structures, like all things, are subject to the relentless pressure of time. A lock’s effectiveness isn’t measured by its initial resistance, but by the rate at which it yields to persistent probing.
Future investigations will likely focus on the dynamic aspects of these ‘locks’. Static analysis, even with nuanced techniques like k-cut enumeration, provides only a partial picture. The true challenge lies in modeling the interaction between attacker and design over time-a complex system where stability is often a delay of inevitable compromise. Considering the computational cost of exhaustive evaluation, approximations and probabilistic models will become increasingly crucial, though any simplification introduces its own set of vulnerabilities.
Ultimately, the field confronts a paradox. Increasing complexity in defensive mechanisms creates increasingly complex attack surfaces. The quest for perfect security is, by definition, asymptotic. It is not an error in the lock itself that will ultimately matter, but the sheer weight of time and ingenuity brought to bear against it. The system does not fail; it ages.
Original article: https://arxiv.org/pdf/2602.21386.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- All Skyblazer Armor Locations in Crimson Desert
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- All Shadow Armor Locations in Crimson Desert
- Marni Laser Helm Location & Upgrade in Crimson Desert
- One Piece Chapter 1180 Release Date And Where To Read
- All Helfryn Armor Locations in Crimson Desert
- All Golden Greed Armor Locations in Crimson Desert
- All Icewing Armor Locations in Crimson Desert
- How to Beat Stonewalker Antiquum at the Gate of Truth in Crimson Desert
- Legendary White Lion Necklace Location in Crimson Desert
2026-02-26 20:08