Author: Denis Avetisyan
A novel class of ‘liquidity exhaustion’ attacks threatens the security of emerging intent-based cross-chain bridges by exploiting temporary capital shortages.
This review details how solver vulnerabilities in intent-based bridges can lead to availability attacks and potential profit extraction, impacting DeFi interoperability.
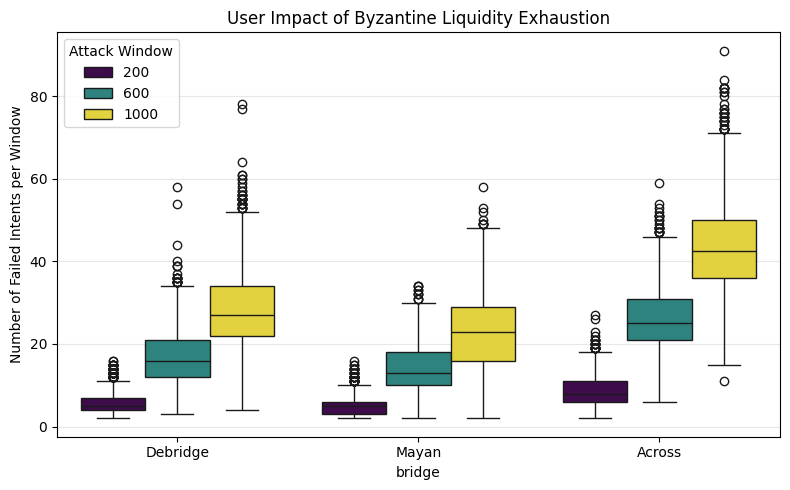
While intent-based cross-chain bridges offer improved user experience by leveraging off-chain solvers, this paradigm introduces novel economic vulnerabilities. Our work, ‘Exploiting Liquidity Exhaustion Attacks in Intent-Based Cross-Chain Bridges’, identifies and analyzes a new class of attacks-liquidity exhaustion-demonstrating how temporary depletion of solver capital can disrupt bridge availability and generate profit. Analyzing 3.5 million cross-chain intents across three major protocols, we show that protocols like deBridge are susceptible to these attacks under current parameters, while Across remains robust; furthermore, we reveal optimized attack strategies that significantly lower the barrier to entry. Can these findings inform the development of more resilient and economically secure interoperability solutions for the rapidly evolving decentralized finance landscape?
Unlocking Interoperability: Beyond Locks and Burns
Conventional cross-chain bridges, while enabling asset transfer between blockchains, frequently rely on mechanisms like locking assets on one chain and minting equivalent representations on another – or, alternatively, burning tokens on the source chain and minting new ones on the destination. These ‘lock-and-mint’ or ‘burn-and-redeem’ approaches introduce inherent vulnerabilities; locked assets represent custodial risk, creating attractive targets for hackers, while the need for trusted intermediaries to manage these processes introduces potential failure points. Furthermore, these systems often suffer from capital inefficiency, as assets are effectively duplicated across chains, limiting their utility and requiring substantial liquidity to facilitate transfers. The very architecture of these bridges necessitates pre-funding or reliance on centralized custodians, hindering scalability and creating systemic risks that newer approaches aim to mitigate.
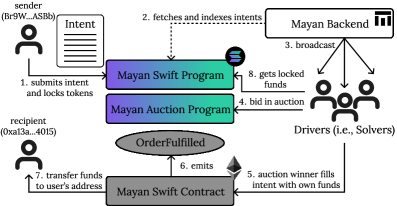
Traditional cross-chain communication often dictates how a transfer must occur – locking tokens on one chain and minting equivalents on another. Intent-based bridges, however, represent a fundamental shift in this approach, prioritizing the user’s desired outcome instead. This means a user simply specifies what they want to achieve – for example, swapping tokens across chains – without needing to concern themselves with the underlying mechanics. This abstraction unlocks considerable flexibility, allowing for more complex transactions and integration with decentralized applications, and fostering greater composability within the broader blockchain ecosystem. By separating intent from execution, these bridges enable a dynamic system where solvers compete to fulfill user requests in the most efficient manner, potentially reducing slippage and maximizing returns.
Intent-based bridges are distinguished by their reliance on off-chain ‘Solvers’ – specialized entities that compete to fulfill user-defined ‘Cross-Chain Intents’ rather than adhering to pre-programmed pathways. This creates a dynamic marketplace where liquidity providers, acting as Solvers, bid to execute these intents, optimizing for cost and speed. Recent data demonstrates the growing traction of this model; analysis reveals $9.24 billion in value has been transacted across 3.5 million intents on these bridges, indicating a substantial shift in how cross-chain communication is handled and suggesting a future where users specify desired outcomes, leaving the execution details to a competitive network of solvers.
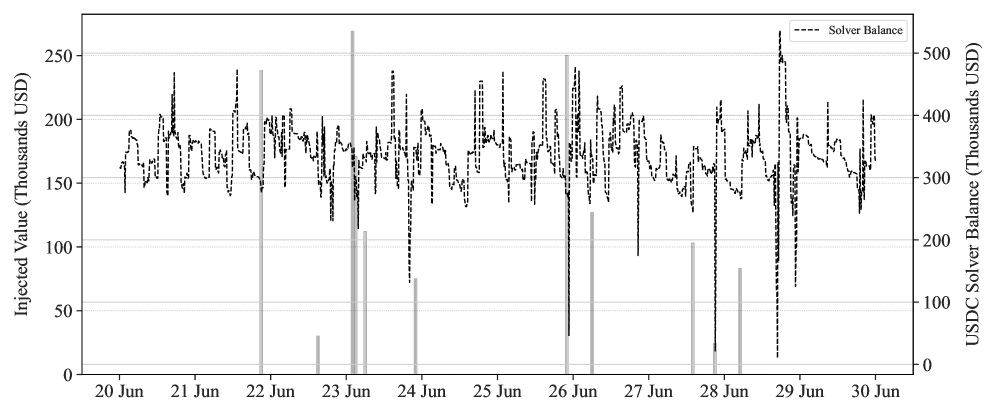
The Illusion of Solidity: Exposing Liquidity Exhaustion
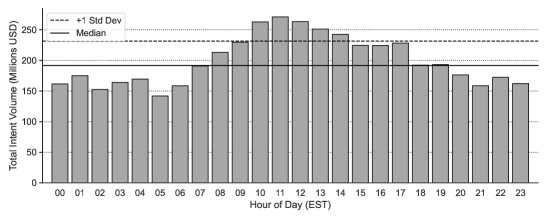
Liquidity Exhaustion Attacks represent a significant vulnerability in intent-based bridges. These attacks exploit temporary reductions in ‘Solver Liquidity’ – the funds available to execute user intents – leading to disruptions in intent fulfillment. Research indicates that solver liquidity is not consistently maintained across prominent bridges, with recurring depletion events observed in Mayan Swift, Across, and deBridge. This volatility creates opportunities for malicious actors to manipulate the system, as insufficient liquidity prevents the timely and successful completion of user transactions. The attacks do not necessarily require exploiting technical flaws in the bridge code itself, but rather capitalize on the economic conditions of available solver funds.
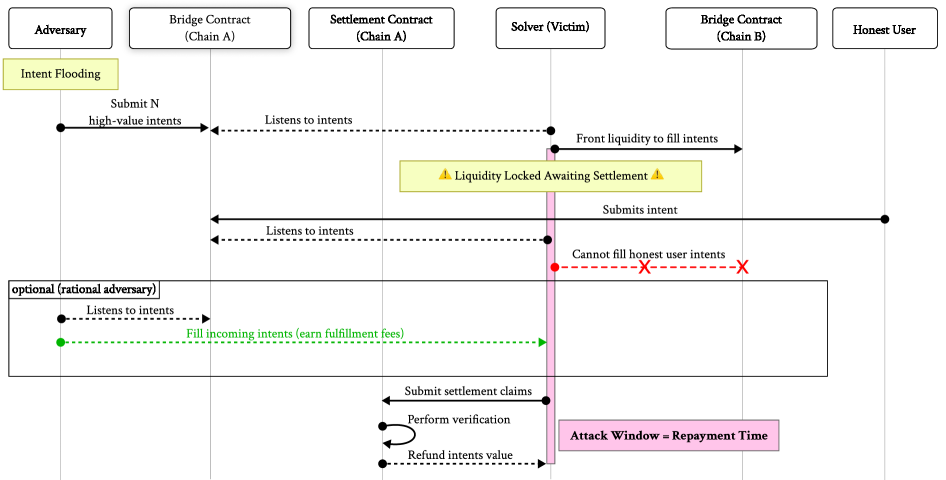
Intent-based bridges are vulnerable to exploitation by both ‘Rational Adversary’ and ‘Byzantine Adversary’ models due to the potential for ‘Liquidity Exhaustion Attacks’. A Rational Adversary, motivated by financial gain, can manipulate solver liquidity depletion to profit from discrepancies in asset pricing or extract funds during settlement delays. Conversely, a Byzantine Adversary, acting with malicious intent but without necessarily seeking financial reward, can induce solver liquidity exhaustion to disrupt bridge functionality and impede legitimate transactions. The differing motivations of these adversarial models do not alter their ability to exploit the underlying vulnerability; both can capitalize on temporary solver liquidity deficits to achieve their objectives, whether financial or disruptive.
Settlement delay, the period between a solver fulfilling a user intent and receiving reimbursement, significantly increases the vulnerability of intent-based bridges to liquidity exhaustion attacks. This delay creates a window where solver liquidity is temporarily reduced, allowing malicious actors to exploit the imbalance. Observed protocol refund times vary considerably: Mayan and deBridge exhibit approximate refund periods of 1,000 seconds, while Across requires over 2 hours for solver reimbursement. This substantial difference directly impacts the feasibility of attacks, as longer delays provide a greater opportunity for manipulation and increase the potential for successful disruption or profit-seeking exploits.
Fortifying the System: Proactive Defenses Against Exhaustion
Rate limiting and automated solver rebalancing are key proactive defense mechanisms against exhaustion attacks. Rate limiting functions by restricting the rate at which intents are fulfilled based on currently available liquidity; when liquidity is constrained, intent processing is throttled to prevent complete system failure. Automated solver rebalancing complements this by dynamically adjusting the capital allocation assigned to each solver. This redistribution of capital aims to optimize the system’s ability to handle incoming intents and maintain service availability, even under stress, by ensuring resources are directed towards the most efficient and responsive solvers. Both strategies operate preemptively, mitigating risk before an attack fully manifests and providing resilience against fluctuating demand or malicious activity.
Dynamic fee adjustment functions as an incentive mechanism to encourage solver participation during peak demand. This approach draws inspiration from both Ethereum’s EIP-1559 proposal, which introduced a base fee burned with each transaction to dynamically adjust block prices, and the liquidity provision models utilized by Aave. By increasing fees when demand for intent fulfillment exceeds available solver capacity, the system creates a financial incentive for more solvers to contribute liquidity. Conversely, during periods of low demand, fees can be reduced to maintain solver engagement. This dynamic adjustment aims to balance network load with solver availability, ensuring consistent performance and resilience against potential exhaustion attacks.
Solver diversity is a critical component of system robustness, mitigating risks associated with single points of failure or malicious manipulation. Our analysis demonstrates that a concentrated attack targeting a limited pool of solvers can significantly reduce the cost required to compromise the system; specifically, a targeted attack strategy can decrease attack costs by as much as 97.18% compared to a non-targeted approach. This data highlights the importance of distributing intent fulfillment across a broader range of independent solvers to increase the overall cost and complexity for potential attackers and enhance system resilience.
The Evolving Landscape: A Future of Intent-Driven Interoperability
The burgeoning field of cross-chain interoperability is witnessing a shift toward intent-based bridges, exemplified by platforms like Across, Mayan Swift, and deBridge. These systems represent a departure from traditional methods, focusing not on how to move assets between blockchains, but rather on the user’s intended outcome. By abstracting away the underlying complexities of cross-chain communication – such as differing consensus mechanisms and data formats – these bridges simplify the process for developers and end-users alike. This simplification fosters a more composable blockchain ecosystem, enabling decentralized applications to seamlessly interact with assets and data across multiple chains. Consequently, the potential for innovation in areas like decentralized finance and Web3 is significantly expanded, as applications are no longer constrained by the limitations of a single blockchain environment.
Recent advancements in cross-chain communication prioritize user intent over the intricate technical details of transferring assets, opening doors to innovative applications within decentralized finance and Web3. Systems like deBridge aim to simplify the process, allowing users to execute actions – such as swapping tokens or interacting with smart contracts – without needing to understand the underlying complexities of bridging. However, a recent analysis reveals a significant vulnerability: under specific configurations, deBridge experienced a 67% success rate for simulated attacks, highlighting the critical need for robust security measures. This underscores that while intent-based bridges offer considerable potential for a more interconnected blockchain landscape, ongoing research and development of defensive mechanisms are paramount to realizing their long-term viability and protecting user funds.
The promise of a seamlessly interconnected blockchain ecosystem hinges on a sustained commitment to bolstering the security of cross-chain communication. While intent-based bridges represent a significant step forward, they are not impervious to attack, as demonstrated by vulnerability analyses revealing potential exploits even in leading systems. Consequently, ongoing research and development are paramount; this includes not only refining existing defense mechanisms against known vectors but also proactively addressing emerging vulnerabilities as the technological landscape evolves. This iterative process of threat identification, mitigation, and validation is critical for fostering user trust and ensuring the long-term viability of cross-chain interoperability, ultimately unlocking the full potential of a truly composable Web3.
The exploration of liquidity exhaustion attacks reveals a fundamental truth about complex systems: stability isn’t inherent, it’s earned. This research, detailing how temporary capital depletion can disrupt intent-based cross-chain bridges, echoes a sentiment shared by Linus Torvalds: “Most good programmers do programming as a hobby, and then they get paid to do it.” The drive to understand and then break a system-to test its limits-is precisely what this paper embodies. By deliberately probing the vulnerabilities within these bridges, the authors aren’t simply identifying risks, they’re reverse-engineering the architecture of trust itself, uncovering the unseen connections that govern decentralized finance. The intentional stress testing exposes the fragility hidden within seemingly robust designs.
What Lies Beyond the Bridge?
The notion of ‘intent-based’ bridges, so neatly sidestepping the cumbersome mechanics of lock-and-mint, always felt…elegant. Perhaps too elegant. This work doesn’t so much invalidate the concept as highlight its inherent fragility – a system trusting in continuous solvency, exposed by the simple, brutal reality of temporary capital depletion. The attack vectors detailed here aren’t flaws in code, precisely. They’re consequences of assuming perpetual access to a resource-a dangerous game in any decentralized system. The problem isn’t if liquidity will be exhausted, but when, and the ensuing scramble to re-establish guarantees will be…instructive.
Future work needn’t focus solely on patching this particular vulnerability. The real question is whether a truly robust cross-chain system is even achievable with current economic models. Perhaps the pursuit of seamless interoperability is itself a misdirection. Maybe friction – the very thing intent-based bridges attempt to eliminate – is a necessary security feature. The research now shifts from preventing exhaustion to designing systems that expect it, and degrade gracefully-or, ideally, fail spectacularly but safely.
One can also consider the implications for ‘solver’ markets. Is there a sustainable economic model for incentivizing continuous availability, or are these systems fundamentally vulnerable to coordinated, or even accidental, disruptions? The study of these attacks isn’t about protecting bridges; it’s about reverse-engineering the limits of trust in a world built on probabilistic guarantees.
Original article: https://arxiv.org/pdf/2602.17805.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- All Skyblazer Armor Locations in Crimson Desert
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- How to Catch All Itzaland Bugs in Infinity Nikki
- Jojo’s Bizarre Adventure Ties Frieren As MyAnimeList’s New #1 Anime
- Invincible: 10 Strongest Viltrumites in Season 4, Ranked
- Speedsters Sandbox Roblox Codes
- Re:Zero Season 4 Episode 3 Release Date & Where to Watch
- Top 10 Must-Watch Isekai Anime on Crunchyroll Revealed!
- Who Can You Romance In GreedFall 2: The Dying World?
- USD CNY PREDICTION
2026-02-24 01:07