Author: Denis Avetisyan
Researchers have developed a novel framework that moves beyond traditional anomaly detection by incorporating explicitly defined security policies to improve the accuracy and interpretability of encrypted traffic analysis.

INTACT reformulates encrypted traffic anomaly detection as conditional constraint learning, enabling policy-driven security monitoring and violation inference.
Conventional security monitoring often treats anomalies as statistical deviations, yet in cryptographic traffic, violations are defined by explicit policy constraints-a fundamental mismatch limiting interpretability and adaptability. To address this, we introduce INTACT (INTent-Aware Cryptographic Traffic), a novel framework that reformulates violation detection as conditional constraint learning, explicitly incorporating declared security intent into the process. This approach yields a policy-parameterized family of decision boundaries, achieving near-perfect discrimination on real-world data and superior performance in detecting complex violations within a synthetic environment. Does this explicit intent conditioning represent a paradigm shift towards more robust and interpretable cryptographic monitoring systems?
The Evolving Landscape of Cryptographic Vulnerabilities
Conventional security systems frequently depend on signature-based detection methods, identifying threats by matching known patterns of malicious code or activity. However, this reactive approach struggles against the increasingly complex world of cryptographic attacks and policy breaches. As adversaries develop novel techniques-circumventing established signatures-these systems become less effective at identifying zero-day exploits or subtle violations of cryptographic best practices. This limitation is particularly acute in scenarios involving sophisticated attacks that exploit inherent weaknesses in cryptographic algorithms or misuse legitimately issued keys, highlighting the need for more intelligent, behavior-based security solutions capable of detecting anomalous activity rather than simply recognizing known threats.
The escalating complexity of cryptographic attacks necessitates a shift from reactive security protocols to those that anticipate and understand malicious intent. Traditional defenses, focused on identifying known attack signatures, are proving insufficient against adversaries who exploit subtle weaknesses within cryptographic algorithms or deliberately misuse encryption keys. These evolving threats demand security measures capable of analyzing how cryptographic tools are being used, not just that they are being used. Proactive systems now leverage behavioral analysis and anomaly detection to identify deviations from expected cryptographic practices, such as unexpected algorithm downgrades or key reuse, offering a more robust defense against increasingly sophisticated attacks that target the fundamental integrity and confidentiality of data. This intent-aware approach promises to significantly bolster cryptographic defenses in an era where simply recognizing a known threat is no longer sufficient.
Cryptographic systems are fundamentally undermined when key management policies are breached, leading to substantial risks for data confidentiality and integrity. Violations such as Lifetime Violation – using keys beyond their approved expiration date – create opportunities for attackers to exploit known vulnerabilities that may have been patched in newer iterations of an algorithm. Similarly, Algorithm Downgrade Violation, where stronger encryption is replaced with weaker, outdated methods, renders previously secure data vulnerable to decryption. Perhaps most concerning is Key Reuse Violation, which significantly increases the likelihood of a successful cryptanalysis, as repeated use of the same key provides attackers with more data to discern patterns and break the encryption. These seemingly technical failures represent tangible threats, potentially exposing sensitive information and compromising the trust upon which digital security relies.
INTACT: A Conditional Approach to Violation Detection
INTACT departs from traditional signature-based or anomaly-based cryptographic traffic analysis by formulating violation detection as a conditional constraint learning problem. This reframing allows the system to learn the boundaries of acceptable behavior defined by security policies rather than relying on pre-defined patterns or statistical deviations. Specifically, INTACT aims to learn a conditional distribution – the probability of observed traffic given an intended security policy – and identify instances where the observed traffic significantly deviates from this learned distribution, thus indicating a potential violation. This approach enables proactive detection of violations even if they do not match known attack signatures, and allows for a more nuanced assessment of traffic legitimacy based on the expressed intent of the security policy.
INTACT’s Intent Encoder functions by converting abstract, human-readable security policies – such as “allow outbound HTTPS traffic to known financial institutions” – into dense vector representations known as semantic embeddings. This transformation is achieved through a neural network trained to map policy language to these vectors, effectively capturing the meaning of the policy rather than simply its keywords. The resulting embedding serves as a standardized, numerical representation of the desired network behavior, facilitating automated comparison with observed traffic characteristics. This allows INTACT to detect deviations from the intended policy, even if the observed traffic doesn’t directly match predefined signatures or patterns.
The Behavioral Encoder within INTACT processes network traffic characteristics – including packet sizes, inter-arrival times, and protocol flags – and converts these features into a numerical vector representation. This transformation utilizes techniques such as dimensionality reduction and feature scaling to create a concise and comparable embedding of the observed traffic behavior. The resulting vector facilitates a quantitative assessment of deviations from the desired behavior, as defined by the Intent Encoder’s semantic embedding. This proactive violation assessment allows for the identification of potentially malicious or non-compliant traffic patterns before they can fully manifest, improving security monitoring and response capabilities.
Underlying Mathematical Foundations: Conditional Violation Functions
INTACT utilizes a Conditional Violation Function, mathematically expressed as P(y=1|x,z), to determine the likelihood of a policy violation. Here, ‘y’ represents a binary violation indicator (1 for violation, 0 for no violation), ‘x’ denotes observed traffic data – encompassing variables like packet rates, flow sizes, and source/destination addresses – and ‘z’ represents the declared network intent or policy. This function assesses the probability of a violation occurring given specific traffic characteristics and the stated intent, allowing for a nuanced evaluation beyond simple threshold-based detection. The output of this function is a probability score between 0 and 1, representing the estimated risk of a violation for a given state of the network and declared policies.
The core of INTACT’s assessment capability lies in its direct mapping of observable system behavior – represented by traffic data x – to predefined policy constraints. This linkage is achieved by quantifying the relationship between observed actions and whether a constraint is violated, indicated by a binary outcome y where 1 signifies a violation. This allows for a context-aware evaluation because the assessment isn’t simply a static check against a rule; instead, the probability of violation, P(y=1|x,z) – where z represents declared intent – is calculated based on the specific observed behavior and the intended operation, providing a nuanced understanding of policy adherence and potential risks.
Lagrangian Relaxation is employed as an optimization technique to address the constrained learning problem arising from the integration of Conditional Violation Functions. This method transforms the original constrained problem into an unconstrained one by introducing Lagrange multipliers, which penalize violations of the constraints. The resulting objective function, incorporating these penalties, is then optimized using standard techniques. This approach allows for efficient computation, particularly in high-dimensional spaces, and facilitates scalability to large networks. By iteratively updating the Lagrange multipliers, the algorithm converges towards a solution that minimizes both the primary objective and the constraint violations, thereby enabling real-time performance and practical deployment of the intent-aware network control system. L(x, \lambda) = f(x) + \sum_{i=1}^{m} \lambda_i g_i(x) , where f(x) is the original objective, g_i(x) are the constraint functions, and \lambda_i are the Lagrange multipliers.
INTACT: Extending Beyond Conventional Methods
Statistical Anomaly Detection, commonly employing methods like Density-Based Detection, traditionally identifies deviations from established baselines without understanding why those deviations occur. INTACT builds upon these techniques by integrating intent-awareness, effectively adding a layer of contextual understanding. This means the system doesn’t just flag unusual activity; it evaluates that activity relative to the network’s declared objectives and policies. For instance, a surge in traffic might normally trigger an alert, but INTACT, knowing the intent is to provision resources for a scheduled event, correctly identifies it as expected behavior. By incorporating this semantic understanding, INTACT significantly reduces false positives and focuses attention on genuinely malicious or misconfigured activity, improving the efficiency and accuracy of network security monitoring.
INTACT significantly advances network security through active support for Intent-Based Networking (IBN). This framework moves beyond reactive security measures by allowing administrators to define desired network behavior – the ‘intent’ – rather than configuring individual devices. INTACT then automatically translates this high-level intent into the necessary low-level configurations and actively enforces these policies across the network. This automation not only reduces the potential for human error but also enables dynamic adaptation to evolving threats and changing business requirements. By continuously monitoring network behavior and comparing it against the declared intent, the system can proactively identify and mitigate deviations, ensuring consistent security posture and simplifying network management.
INTACT elevates network security beyond simple anomaly detection by establishing a robust feedback loop with Formal Policy Validation tools. This integration isn’t merely about identifying deviations from normal behavior, but verifying that the intended network behavior, as explicitly defined in security policies, is consistently realized in practice. By cross-referencing observed network activity with formally validated policies, INTACT can confirm correct implementation and enforcement, thereby mitigating risks arising from configuration errors or policy drift. This closes a critical gap in traditional security approaches, which often struggle to guarantee that declared intent translates into actual security posture, offering a more definitive and trustworthy level of assurance.
Future Directions: Maintaining Resilience in a Dynamic Environment
The consistent accuracy of network intrusion detection systems, such as INTACT, is fundamentally challenged by distribution shift – the inevitable alteration of data patterns over time and across varying network conditions. As network traffic evolves due to new applications, user behaviors, and emerging attack vectors, the statistical characteristics of ‘normal’ traffic change, potentially rendering previously effective detection models obsolete. Consequently, maintaining INTACT’s efficacy necessitates proactive strategies to address these shifts, ensuring it can reliably distinguish between legitimate activity and malicious intent even when confronted with previously unseen data distributions. Research is focused on techniques that allow the system to adapt and generalize, preventing performance degradation and sustaining a robust security posture in dynamic network landscapes.
Current investigations surrounding INTACT prioritize bolstering its capacity for effective learning even with sparse datasets, a crucial capability given the constantly evolving threat landscape and the inherent difficulty of acquiring comprehensive attack data. Researchers are actively exploring techniques to improve generalization, enabling the system to accurately identify and respond to previously unseen attack patterns without requiring extensive retraining. This involves refining the algorithms that allow INTACT to extract meaningful features from limited examples and to build robust models that are less susceptible to overfitting. The ultimate goal is to create a security system that not only defends against known threats but also proactively adapts to and neutralizes emerging cryptographic attacks, ensuring sustained performance and reliability in dynamic network environments.
The enduring strength of INTACT lies in its commitment to a continuously refined, intent-aware methodology. Rather than simply identifying malicious code, the system focuses on understanding the purpose behind network traffic, allowing it to differentiate between legitimate, albeit unusual, activity and genuine threats. This nuanced approach is particularly crucial as cryptographic attacks become increasingly sophisticated and polymorphic, designed to evade signature-based detection. By prioritizing behavioral analysis and contextual understanding, INTACT isn’t simply reacting to known attacks, but proactively adapting to novel threats and maintaining a robust security posture even when faced with evolving cryptographic landscapes. This dedication to intent recognition positions INTACT as a resilient solution capable of safeguarding networks against both present and future challenges.
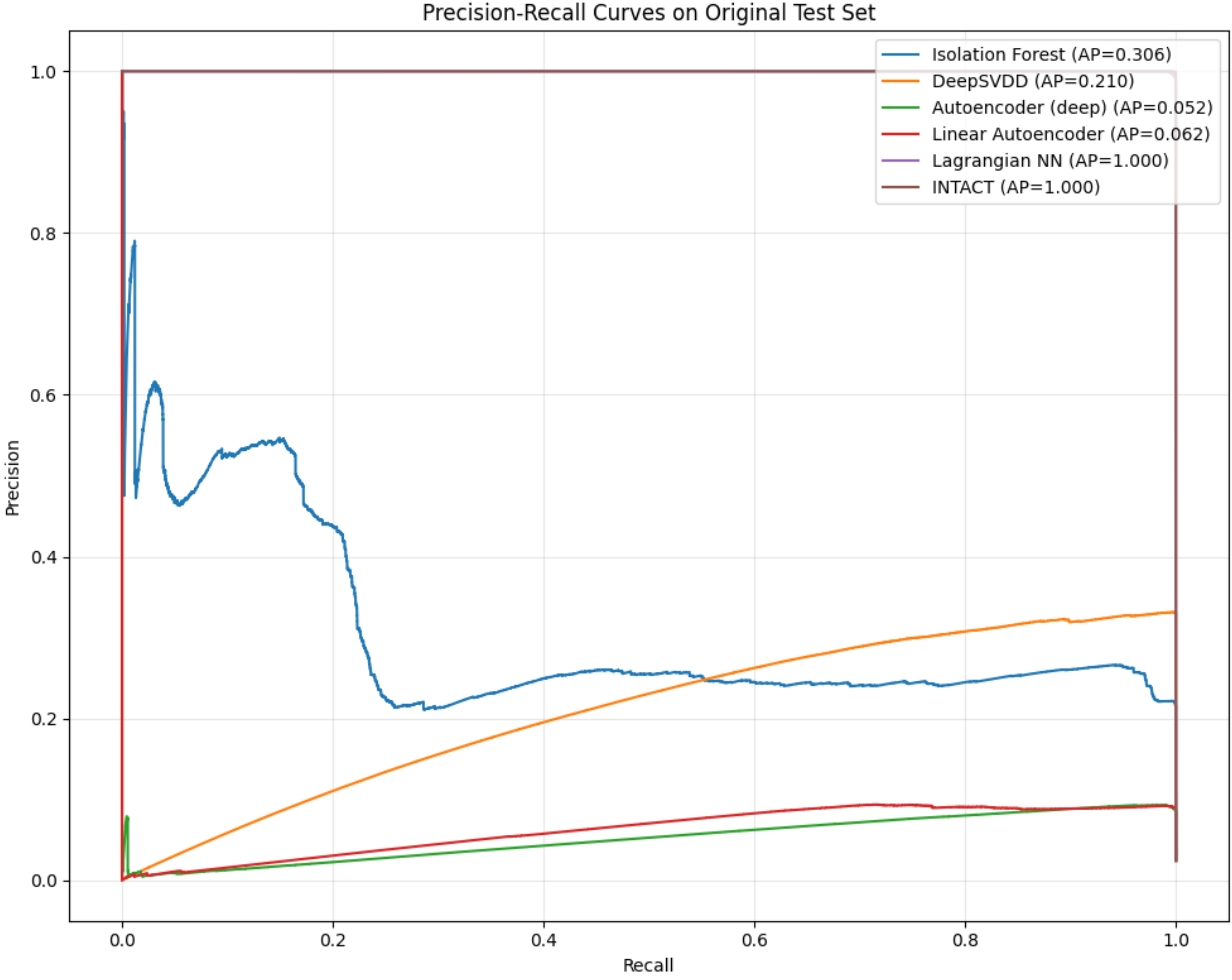
Evaluations demonstrate that INTACT attains leading performance in lifetime violation detection, a crucial metric for identifying potentially malicious activity before complete compromise. Specifically, the system achieved a perfect Area Under the Receiver Operating Characteristic curve (AUROC) of 1.0000 when tested against real-world network data, indicating flawless discrimination between benign and malicious behaviors. Furthermore, INTACT maintained a strong AUROC score of 0.9797 on a synthetically generated dataset, showcasing its robust generalization capability and ability to accurately identify anomalies even in unfamiliar scenarios. These results suggest that INTACT represents a significant advancement in intent-aware network security, offering a highly reliable means of proactive threat detection.
The pursuit of robust anomaly detection, as exemplified by INTACT, echoes a fundamental tenet of mathematical rigor. The framework’s emphasis on explicitly incorporating declared security policies – essentially, defining allowable constraints – aligns perfectly with the notion that clarity of definition precedes accurate inference. As Henri Poincaré stated, “Mathematics is the art of giving reasons.” INTACT doesn’t merely detect deviations; it establishes a formal basis – a ‘reason’ – for identifying violations by framing the problem as conditional constraint learning. This approach moves beyond empirical observation, striving for a provable understanding of normal versus anomalous behavior within cryptographic traffic analysis, much like a theorem derived from established axioms.
Future Directions
The framing of encrypted traffic anomaly detection as conditional constraint learning, as demonstrated by INTACT, represents a necessary, if belated, acknowledgement that security monitoring must be grounded in formally declared policy. However, the elegance of this approach exposes a critical dependency: the fidelity of those policies themselves. A system is only as trustworthy as the axioms upon which it is built; a poorly defined or incomplete security policy introduces systemic error, effectively shifting the problem from detection to policy refinement. The reduction of false positives, frequently touted as a primary goal, becomes moot if the very definition of ‘normal’ is ambiguous.
Future work should therefore not focus solely on increasingly sophisticated representation learning, but on methods for verifiable policy specification. Can we leverage formal methods to ensure that declared security policies are both complete and internally consistent? The current reliance on human-authored policies introduces an unacceptable level of abstraction leak. A truly robust system will require automated policy verification, perhaps drawing inspiration from program verification techniques.
Furthermore, the implicit assumption that ‘intent’ can be accurately inferred from traffic patterns remains problematic. Intent, after all, is a semantic property, and inferring semantics from syntax is, at best, an approximation. The pursuit of perfect anomaly detection is a fool’s errand; the goal should be to minimize the cost of both false positives and false negatives, a cost which, ultimately, must be expressed in quantifiable terms, not merely as a percentage.
Original article: https://arxiv.org/pdf/2602.21252.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- NTE Drift Guide (& Best Car Mods for Drifting)
- How to Get the Wunderbarrage in Totenreich (BO7 Zombies)
- Change Your Perspective Anomaly Commission Guide In NTE (Neverness to Everness)
- How to Beat Turbines in ARC Raiders
- NTE Fan Shows Off Mint Cosplay
- Deltarune Chapter 1 100% Walkthrough: Complete Guide to Secrets and Bosses
- Diablo 4 Best Loot Filter Codes
- How to Unlock the Mines in Cookie Run: Kingdom
- All Nameless Hospital Endings Full Guide In NTE
- Beware! Phishing Emails Are Deceiving Robinhood Users in a Sneaky Plot!
2026-02-27 04:18