Taming Systemic Risk: A Faster Path to Accurate Measurement
![Statistical error in estimating exponential loss-using a two-dimensional Gaussian loss vector-decreases with increased sampling budget for both Sequential Approximate Aggregation (SAA) and single-level Fourier-Randomized Quasi-Monte Carlo (RQMC) methods, with performance notably influenced by the correlation coefficient ρ-specifically, [latex]\rho = -0.5[/latex] and [latex]\rho = 0.5[/latex]-where the sampling budget for SAA [latex]B_{SAA} = N[/latex] and for RQMC [latex]B_{RQMC} = N S_{shift}[/latex].](https://arxiv.org/html/2602.06424v1/x15.png)
A new computational method significantly improves the efficiency and accuracy of quantifying interconnected financial risk.
![Statistical error in estimating exponential loss-using a two-dimensional Gaussian loss vector-decreases with increased sampling budget for both Sequential Approximate Aggregation (SAA) and single-level Fourier-Randomized Quasi-Monte Carlo (RQMC) methods, with performance notably influenced by the correlation coefficient ρ-specifically, [latex]\rho = -0.5[/latex] and [latex]\rho = 0.5[/latex]-where the sampling budget for SAA [latex]B_{SAA} = N[/latex] and for RQMC [latex]B_{RQMC} = N S_{shift}[/latex].](https://arxiv.org/html/2602.06424v1/x15.png)
A new computational method significantly improves the efficiency and accuracy of quantifying interconnected financial risk.
![Density functional theory and coupled cluster methods were rigorously compared in their prediction of metal hydride cation and bimetallic bond dissociation energies, revealing that while both approaches exhibit mean absolute errors generally within the chemically accurate threshold of [latex]0-3 \text{ kcal/mol} [/latex], optimal reference determinant selection-HF or DFT-significantly impacts the performance of coupled cluster methods, achieving comparable accuracy to density functional theory across diverse systems.](https://arxiv.org/html/2602.06149v1/x3.png)
A novel approach leveraging density functional theory as a reference point dramatically improves the reliability of coupled cluster calculations for challenging systems, particularly those containing transition metals.
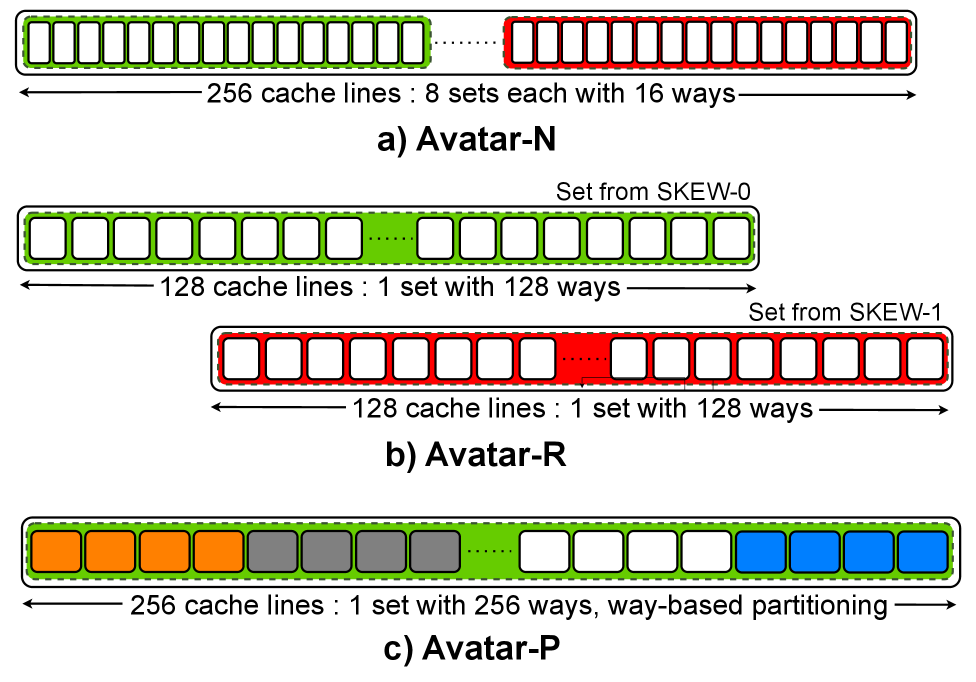
Researchers have developed a novel cache architecture that adapts to security needs on the fly, offering strong defenses against increasingly sophisticated attacks.
![The binding of vortices and antivortices, mediated by current-current coupling between paired [latex]p+ip[/latex] topological superconductors, fosters a composite condensation resulting in a [latex]4e[/latex] topological superconductor exhibiting coexisting superconductivity and a bosonic chiral [latex]\mathbb{Z}_{3}[/latex] topological order further enriched by remnant [latex]\mathbb{Z}_{4}[/latex] charge symmetry.](https://arxiv.org/html/2602.06963v1/vortex.png)
Researchers propose a novel route to building robust quantum computers using materials exhibiting unusual superconducting properties and the unique behavior of parafermions.
Researchers propose a system leveraging secure hardware and blockchain technology to establish the verifiable origin of digital photographs and combat the growing threat of synthetic media.
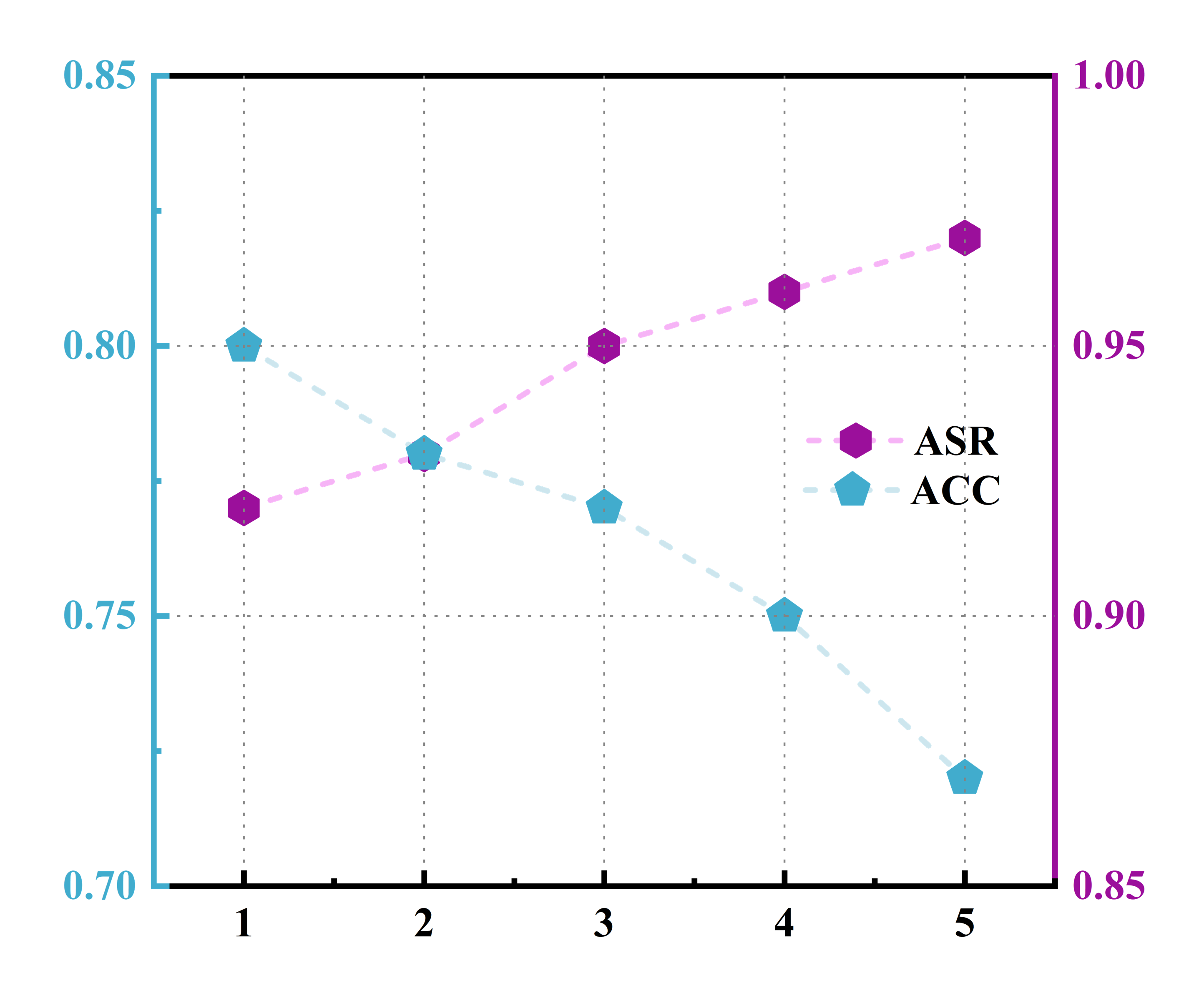
Researchers have uncovered a sophisticated attack that exploits attention mechanisms in federated self-supervised learning to inject hidden backdoors into models.
![Entanglement wedges remain distinct, as demonstrated by the absence of multiple entry of any given HRT surface-represented by a red curve on a Cauchy slice-into another, while adherence to the condition that the intersection of the Cauchy slice with the boundary of spacetime-[latex]\Sigma \cap \partial M[/latex]-contains the spacelike boundaries [latex]\partial B[/latex] and [latex]\partial B^{\<i>}[/latex]-denoted by black and green curves representing the intersections of [latex]\partial \mathcal{E}(B) \cap \Sigma[/latex] and [latex]\partial \mathcal{E}(B^{\</i>}) \cap \Sigma[/latex], respectively-ensures the geometric integrity of these regions.](https://arxiv.org/html/2602.04888v1/x1.png)
New research constructs a powerful graph model to understand how entanglement dictates the limits of information accessible in evolving universes.
A new approach combines encryption and inference to defend against malicious participants in distributed machine learning.
A new theoretical result demonstrates that reaching consensus doesn’t necessarily require the same communication overhead as broadcasting that consensus to all parties.
A new analysis demonstrates how strategic geometric arrangements of optical lattice clocks can enhance the sensitivity of networks designed to detect the subtle ripples of the gravitational wave background.