Rewriting Data Storage with DNA and AI
A new approach combines the density of DNA with artificial intelligence to create a robust and error-resistant digital archiving system.
A new approach combines the density of DNA with artificial intelligence to create a robust and error-resistant digital archiving system.
Researchers demonstrate a surprisingly simple fabrication process for creating vertical nanopillar devices from complex metal-molecule stacks, potentially unlocking scalable molecular electronics and spintronics.
![The band structures of a magnetized square lattice reveal that incorporating optimal site renormalization parameters [latex]\lambda_{j,s}[/latex] significantly alters electronic behavior, distinguishing weakly correlated systems ([latex]U=1t[/latex]) from their strongly correlated counterparts ([latex]U=5t[/latex]).](https://arxiv.org/html/2601.16453v1/figures/_supp_lambdas.png)
New research reveals how strong electron correlation can disrupt the formation of robust integer quantum Hall states, impacting their potential for future electronic devices.
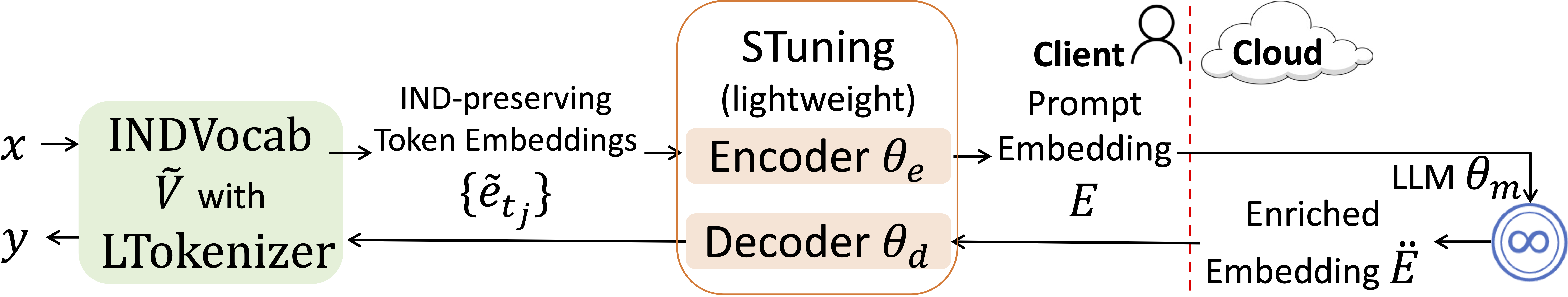
Researchers have developed a novel framework that enables privacy-preserving code generation using open-source AI models, shielding sensitive information from cloud observation.
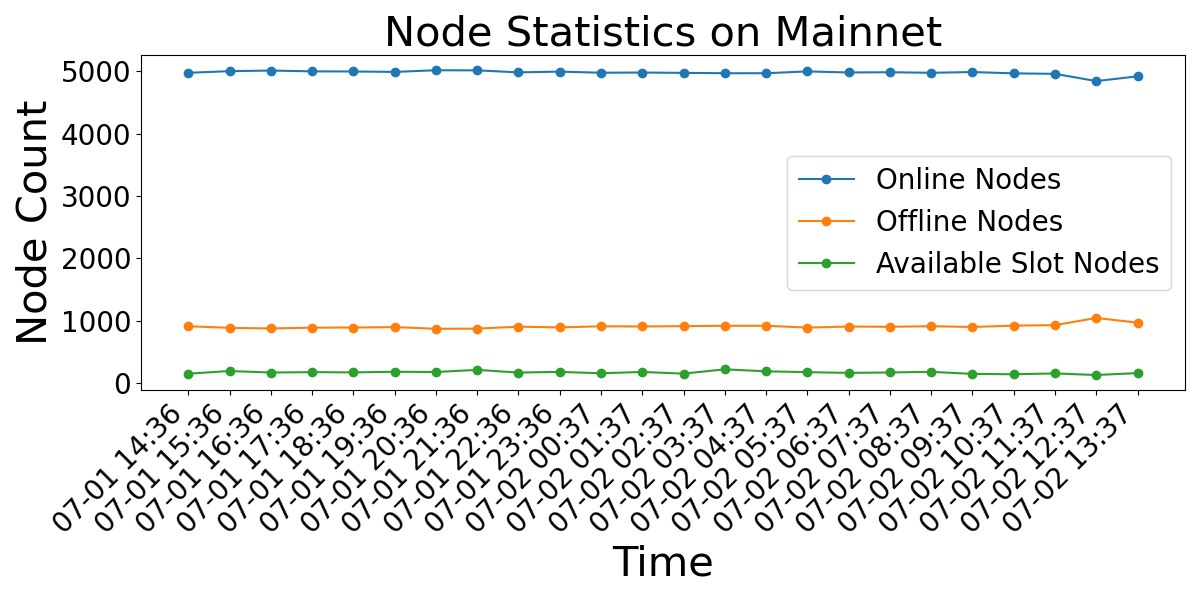
Researchers demonstrate a practical attack that could isolate Ethereum nodes and disrupt network consensus after the Merge.
Researchers have developed a systematic method using BRST symmetry to calculate how spinning black holes interact with surrounding fields.
Researchers are exploring innovative methods to encode quantum information in strontium-87 atoms, potentially unlocking more powerful and robust quantum computers.
Researchers have established a broader range of problems where quantum computers demonstrably outperform their classical counterparts, even under strict resource constraints.
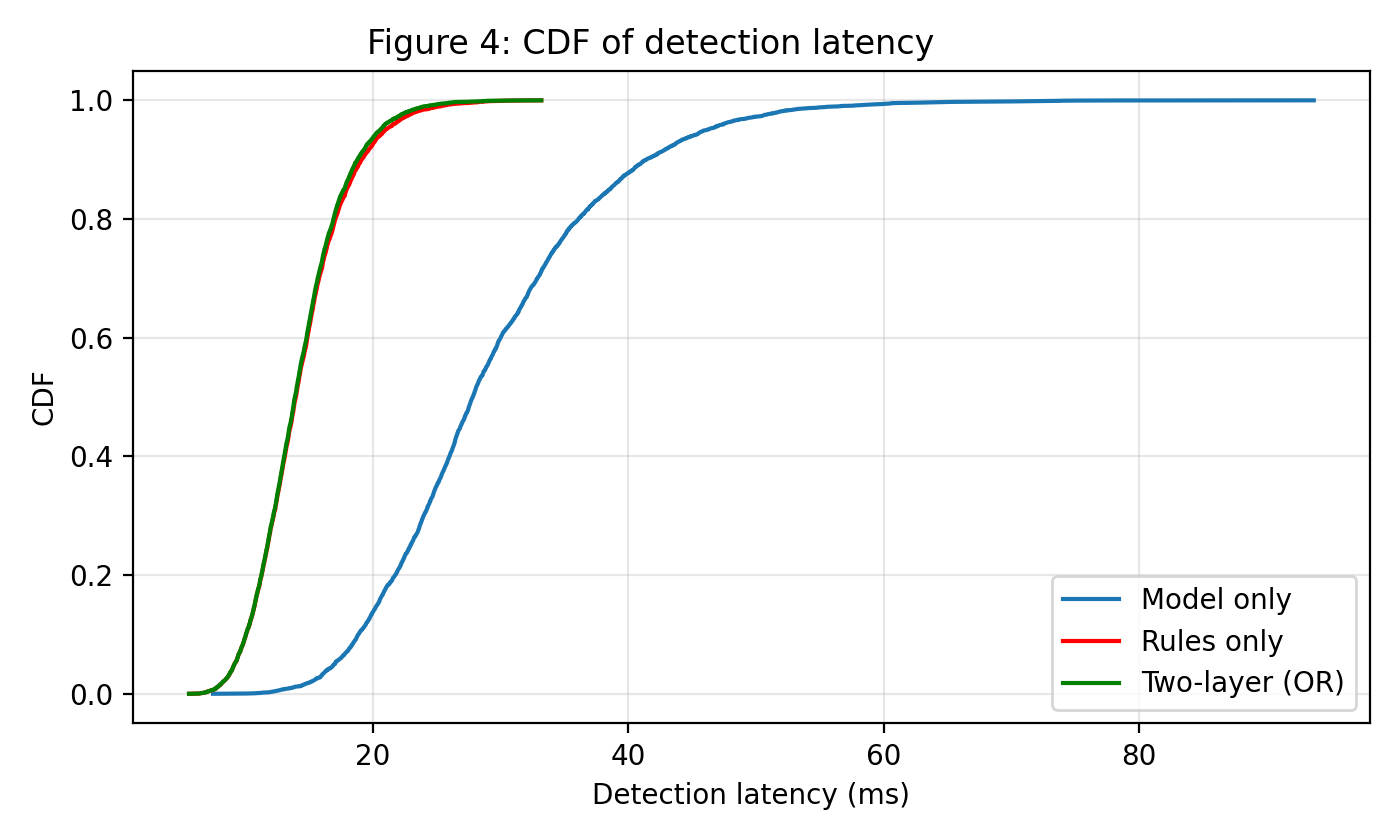
New research details a dynamic security framework that uses machine learning to analyze system behavior and prevent malicious encryption attempts.
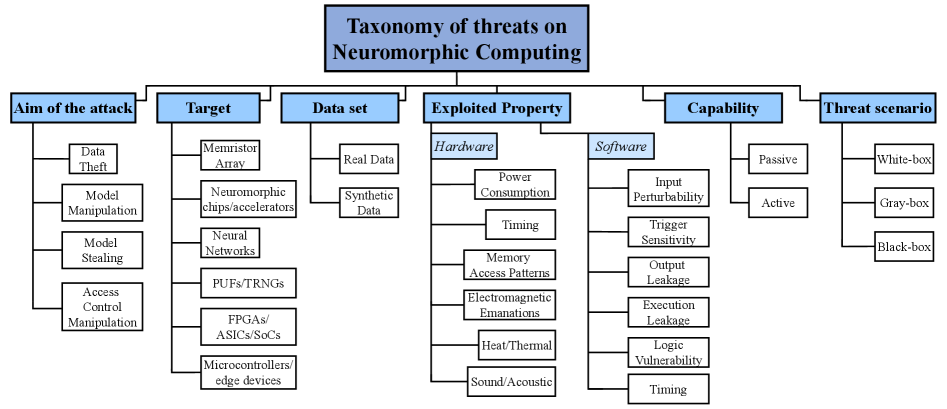
As neuromorphic systems move from research labs to real-world applications, a comprehensive understanding of their unique security vulnerabilities is becoming critically important.