Private Matrices: Scaling Secure Computation with Machine Learning
![The learned rank, [latex] TlT\_{l} [/latex], within the LA-PSMM agent demonstrably influences its computational gain, indicating a performance sensitivity to this specific parameter.](https://arxiv.org/html/2601.09916v1/x5.png)
A new approach combines coded computation and learning-based techniques to dramatically improve the efficiency of perfectly secure distributed matrix multiplication.
![The learned rank, [latex] TlT\_{l} [/latex], within the LA-PSMM agent demonstrably influences its computational gain, indicating a performance sensitivity to this specific parameter.](https://arxiv.org/html/2601.09916v1/x5.png)
A new approach combines coded computation and learning-based techniques to dramatically improve the efficiency of perfectly secure distributed matrix multiplication.
![The study of the XXZ spin model with [latex]S=1[/latex] reveals that even cumulants [latex]\Delta_k[/latex] for [latex]k=2,4,6[/latex] exhibit a power-law scaling with [latex]\delta E[/latex]-specifically, [latex]\Delta_k \propto \delta E^{k-1}[/latex]-across parameter sets [latex]\Delta=0.5, \Delta'=0.5[/latex], [latex]\Delta=1.5, \Delta'=0.5[/latex], and [latex]\Delta=1.5, \Delta'=0.0[/latex], as demonstrated through analysis of system sizes [latex]L=16, 18, 20[/latex] and the total spin current operator [latex]J_S[/latex], with a notable indication of a characteristic energy scale [latex]\Delta E_U[/latex].](https://arxiv.org/html/2601.10211v1/x1.png)
New research demonstrates that the statistical behavior of key operators in chaotic quantum spin chains aligns with predictions from random matrix theory, suggesting a fundamental level of universality.
![The evolution of residuals-specifically comparing the first and last 100 eigenpairs out of a set of 1000-demonstrates the stability of a Silicon pseudo-hermitian Hamiltonian of size [latex]n=23552[/latex] as determined through calculations performed with Yambo.](https://arxiv.org/html/2601.10557v1/x7.png)
A new approach efficiently calculates thousands of eigenpairs for large, non-Hermitian Hamiltonians common in materials science simulations.
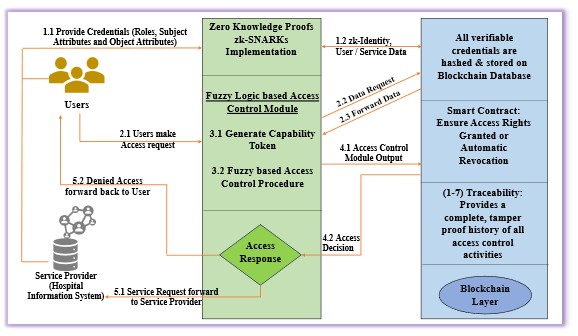
A new framework leverages fuzzy logic and zero-knowledge proofs to fortify data privacy and security in decentralized edge computing environments.
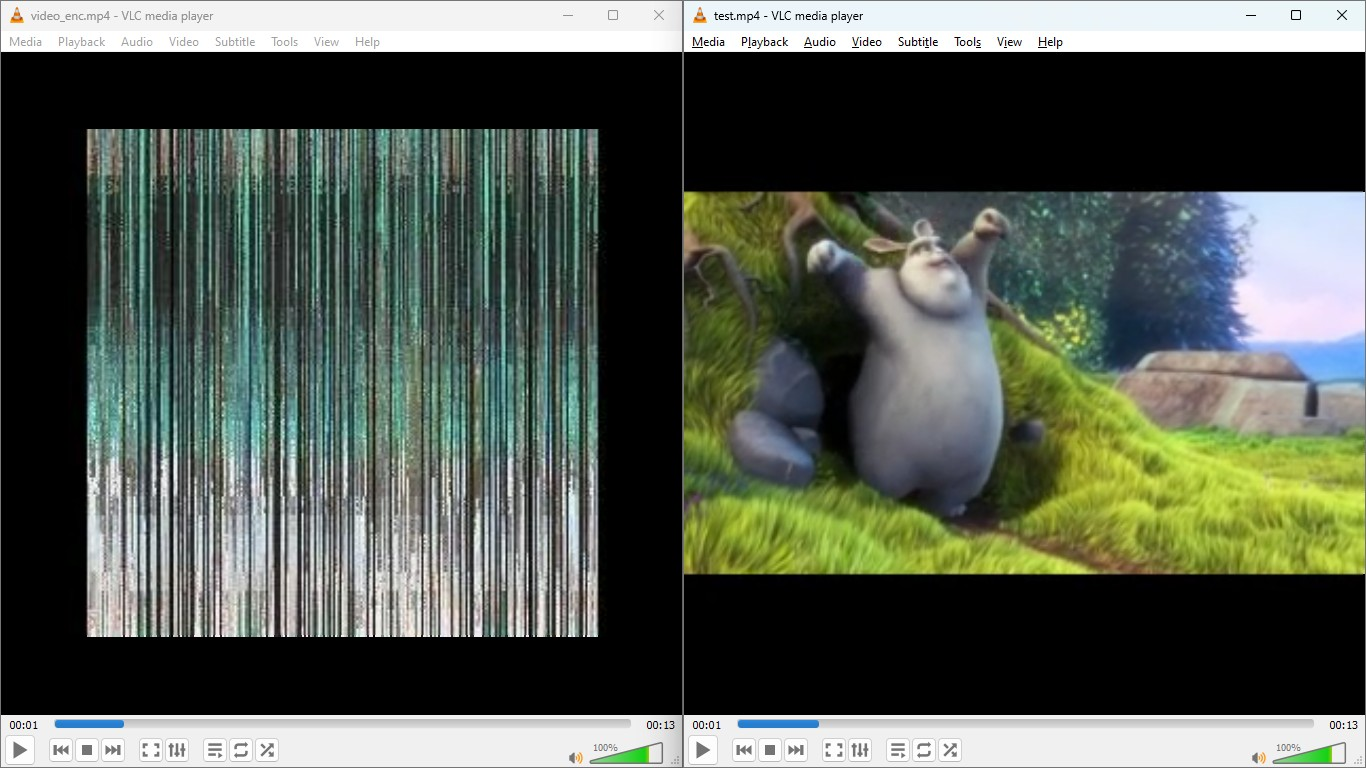
A novel encryption technique leverages the computational complexity of Sudoku puzzles to safeguard images, audio, and video data against modern attacks.
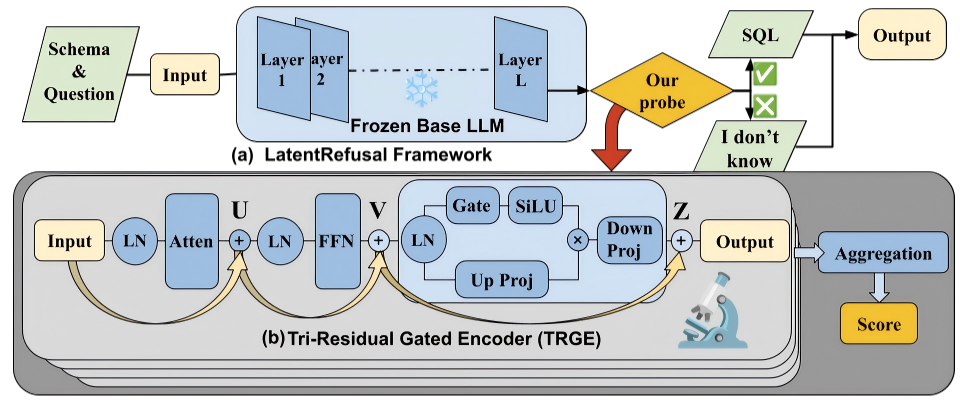
A new approach identifies when a question is impossible to answer with a database, preemptively halting query generation for safer and more reliable text-to-SQL systems.
New research demonstrates how to reliably generate secret keys directly from the inherent structure of complex, multi-terminal data sources.
Researchers have developed a mathematical framework that elegantly connects the behavior of low-energy and high-energy interactions in quantum field theory.
![The study demonstrates that likelihood errors-calculated between full and reduced order quadrature (ROQ) likelihoods, and further refined with a multiband approach-remain consistently below a threshold of [latex] 7\times 10^{-3} [/latex] across 6400 randomly sampled gravitational waveforms drawn from a 256-second basis parameter space, suggesting a high degree of accuracy in the reduced models.](https://arxiv.org/html/2601.09819v1/x2.png)
A new approach to constructing gravitational wave signals significantly speeds up data analysis by efficiently building the necessary mathematical basis.

A comprehensive dataset reveals widespread susceptibility to bad randomness in Ethereum smart contracts, exposing critical gaps in current security tooling.