Boosting Polar Codes with Smart Design Choices
A novel framework combines bit reliability and codeword distance to enhance the performance of polar codes, particularly at shorter block lengths.
A novel framework combines bit reliability and codeword distance to enhance the performance of polar codes, particularly at shorter block lengths.
![For [latex] K = 2 [/latex], [latex] K = 3 [/latex], and [latex] K = 4 [/latex], the achievable rate regions of Algorithm 2-as established by Theorem 4-demonstrate performance approaching channel capacity (Theorem 2), surpassing that of a hard-decision majority-decoder (Corollary 2).](https://arxiv.org/html/2601.09947v1/rate_region.png)
A new algorithm efficiently recovers Reed-Solomon codes from multiple, imperfect readings, offering a path to more reliable data storage and transmission.
![Distinct bursts of [latex] (t_1, t_2) [/latex]-DI are observed in both the x (blue) and y (red) dimensions, indicating transient, directional impulses along these axes.](https://arxiv.org/html/2601.10540v1/x1.png)
This review explores a computationally efficient method for correcting data corruption caused by multiple, consecutive deletions and insertions within a data stream.
![The study demonstrates that performance, as measured by [latex]BLEU-4[/latex] scores, degrades predictably under additive white Gaussian noise (AWGN) conditions, revealing the inherent fragility of inter-component communication in noisy environments.](https://arxiv.org/html/2601.10267v1/x6.png)
A new framework leverages contextual understanding and error correction to dramatically improve communication reliability, particularly in challenging low-signal conditions.
A new hybrid encryption scheme combines classical and quantum techniques to offer robust data protection in the face of evolving computational threats.
=(4,2,3)[/latex] configuration, with [latex]\alpha=3[/latex] and parity consistency [latex]\beta_c[/latex] equaling parity quantization [latex]\beta_q[/latex] both set to [latex]\beta=1[/latex], demonstrates a classical and quantum cut approach to data redundancy and recovery.](https://arxiv.org/html/2601.10676v1/x1.png)
A new approach leveraging quantum entanglement offers the potential to dramatically reduce bandwidth demands in distributed storage systems.
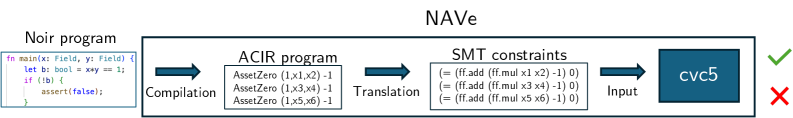
Researchers have developed NAVe, a formal verification system designed to proactively identify vulnerabilities in zero-knowledge circuits built with the Noir programming language.
![The study demonstrates that a non-invertible fusion gate operates not as a continuous transformation-such as movement along a Virasoro coadjoint orbit-but as a discrete shift between conformal families characterized by distinct conformal weights [latex]h_a, h_b, h_c[/latex], effectively manifesting in an AdS3/CFT correspondence as an instantaneous insertion of a defect [latex]D_b[/latex] that abruptly alters boundary stress-tensor data and delineates regions governed by differing highest-weight representations.](https://arxiv.org/html/2601.09534v1/images/fig_cartoon_defectshock_AdS3.png)
New research explores how non-invertible symmetries in quantum circuits connect to the geometry of gravity, potentially refining our understanding of the AdS/CFT correspondence.
Researchers have developed a novel algorithm that simplifies calculations of quantum eigenstates by eliminating the need for summing over intermediate states, offering a complete analytical solution for a wide range of potentials.
![The system models a punctuated arrival process wherein intervals of length Δ are systematically removed, effectively deleting honest blocks and influencing a cumulative score-[latex]B(i)[latex]-that reflects the impact of these deletions on a fully-delayed chain, with the score growth within each interval-[latex]S_{b,i}[latex]-being statistically independent and identically distributed due to the consistent [latex]\Delta[/latex]-length removal.](https://arxiv.org/html/2601.09082v1/x2.png)
A new mathematical proof establishes, with greater rigor than ever before, that honest nodes will consistently outpace malicious actors in the Bitcoin network.