Probing Strong Interactions with Holographic Defects
New research leverages the AdS/CFT correspondence to calculate correlation functions in defect conformal field theories, offering a powerful tool for understanding strongly coupled systems.
New research leverages the AdS/CFT correspondence to calculate correlation functions in defect conformal field theories, offering a powerful tool for understanding strongly coupled systems.
![The framework dissects software vulnerabilities by translating virtual CPU states and function descriptions - termed Reflections and Introspections - into actionable bug data, uniquely identified and categorized as [latex] Reached \ \& \ Triggered [/latex], then standardizing this information alongside fuzzing campaign timing data to visually report performance metrics and expose underlying system behavior.](https://arxiv.org/html/2601.15774v1/x5.png)
Researchers have developed a comprehensive framework to rigorously evaluate the effectiveness of firmware fuzzers, tackling critical challenges in embedded system security.
A new study reveals how inaccuracies in speech-to-text transcription can significantly hinder understanding of spoken code, especially for learners and in multilingual settings.
New research establishes a rigorous mathematical link between microscopic fluctuations and the macroscopic rates of transitions between metastable states, offering insights into phenomena ranging from quantum chromodynamics to condensed matter physics.
![Despite being misled by manipulated reports of [latex] \text{voltage} [/latex] at point A and [latex] \text{current} [/latex] at point B, including a false claim of charging at 1330V and 1330A when actually receiving 448V and 87A, VehicleX continued to charge normally, demonstrating a vulnerability exploitable through real-time, interactive manipulation of communicated demand responses.](https://arxiv.org/html/2601.15515v1/x6.png)
New research reveals a successful wireless Man-in-the-Middle attack against CCS EV charging stations, highlighting critical vulnerabilities in current security protocols.
A new algorithm overcomes reconstruction artifacts in digital holographic microscopy, enabling accurate quantitative phase imaging of large tissue samples.
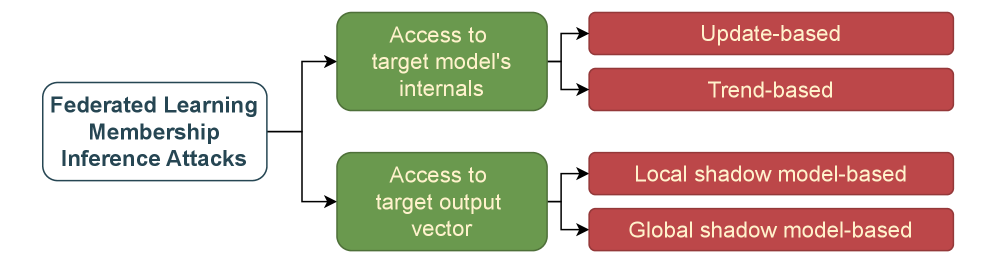
A new review reveals that determining if a specific record was used to train a model from tabular data is surprisingly difficult, despite growing concerns about data privacy.
A new system, Lattice, improves sequential prediction by intelligently blending learned patterns with established baselines, and quantifying its own uncertainty.
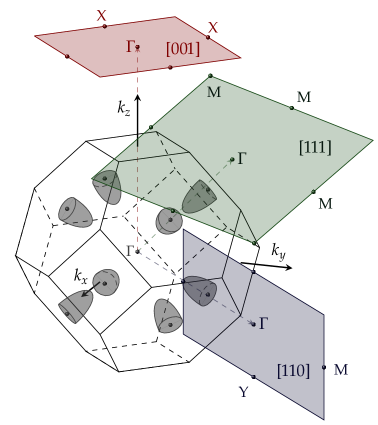
New research explores how manipulating the band structure of IV-VI semiconductor quantum wells can unlock the Quantum Anomalous Hall Effect without the need for external magnetic fields.
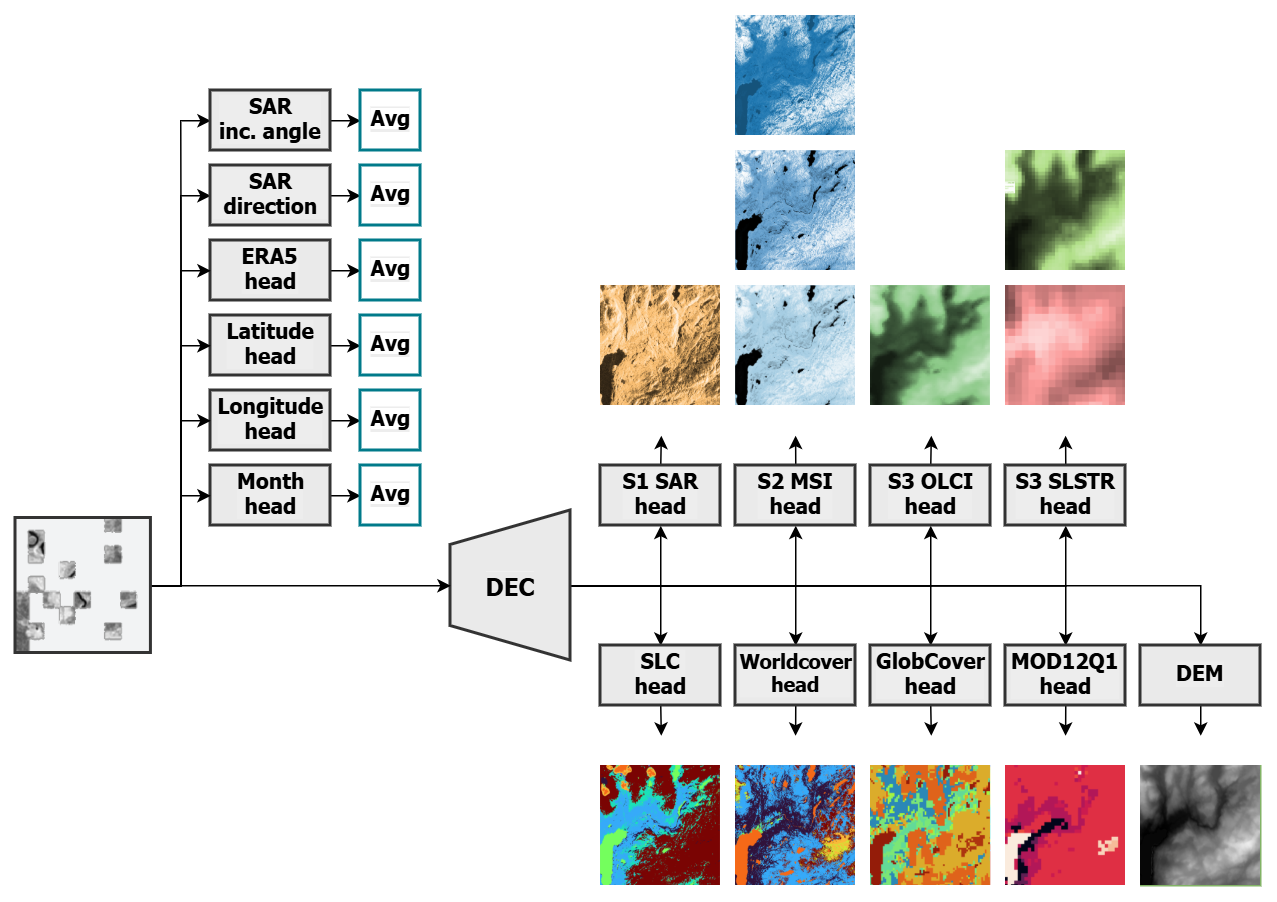
A new foundation model, THOR, promises to unlock greater insights from diverse Earth observation data, offering improved efficiency and adaptability for climate and societal applications.