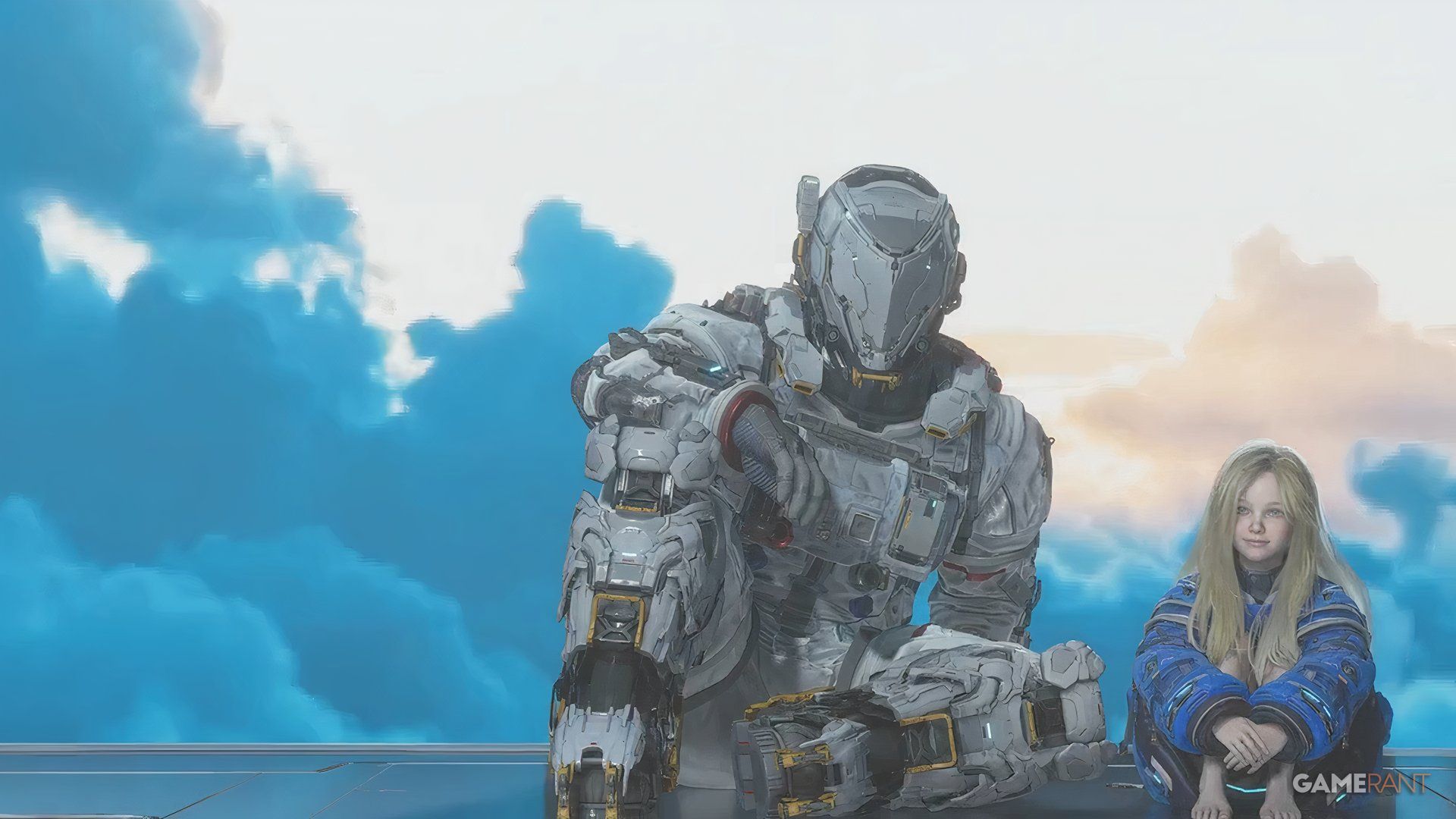
ARC Raiders Reveals How Many Players Focus Solely on PvE vs PvP

Originally, Embark Studios planned for ARC Raiders to be a purely cooperative game, similar to Helldivers 2. However, the team discovered during development that the game wasn’t engaging enough. To create more excitement and encourage players to return, they added player-versus-player (PvP) elements, transforming it into an extraction shooter. This wasn’t about creating a competitive game – there are no PvP leaderboards – but rather about increasing the unpredictability and stress. Now, players have to contend with both dangerous ARC enemies and other players, making each match more challenging.






![Driven Floquet systems exhibit quantum scars-stable states defying typical thermalization-where the mean overlap between initial states and energy eigenstates exceeds random matrix theory predictions, mirroring classical stability boundaries determined by Lyapunov exponents and appearing prominently near driving frequencies of [latex]\omega_{s} = 0[/latex] and π, a phenomenon distinct from the behavior of generic random states which remain closely aligned with random matrix theory expectations across all parameter space.](https://arxiv.org/html/2604.13164v1/x1.png)