One Piece Unveils Nerona Imu’s Akuma no Mi — The Strongest Power Yet
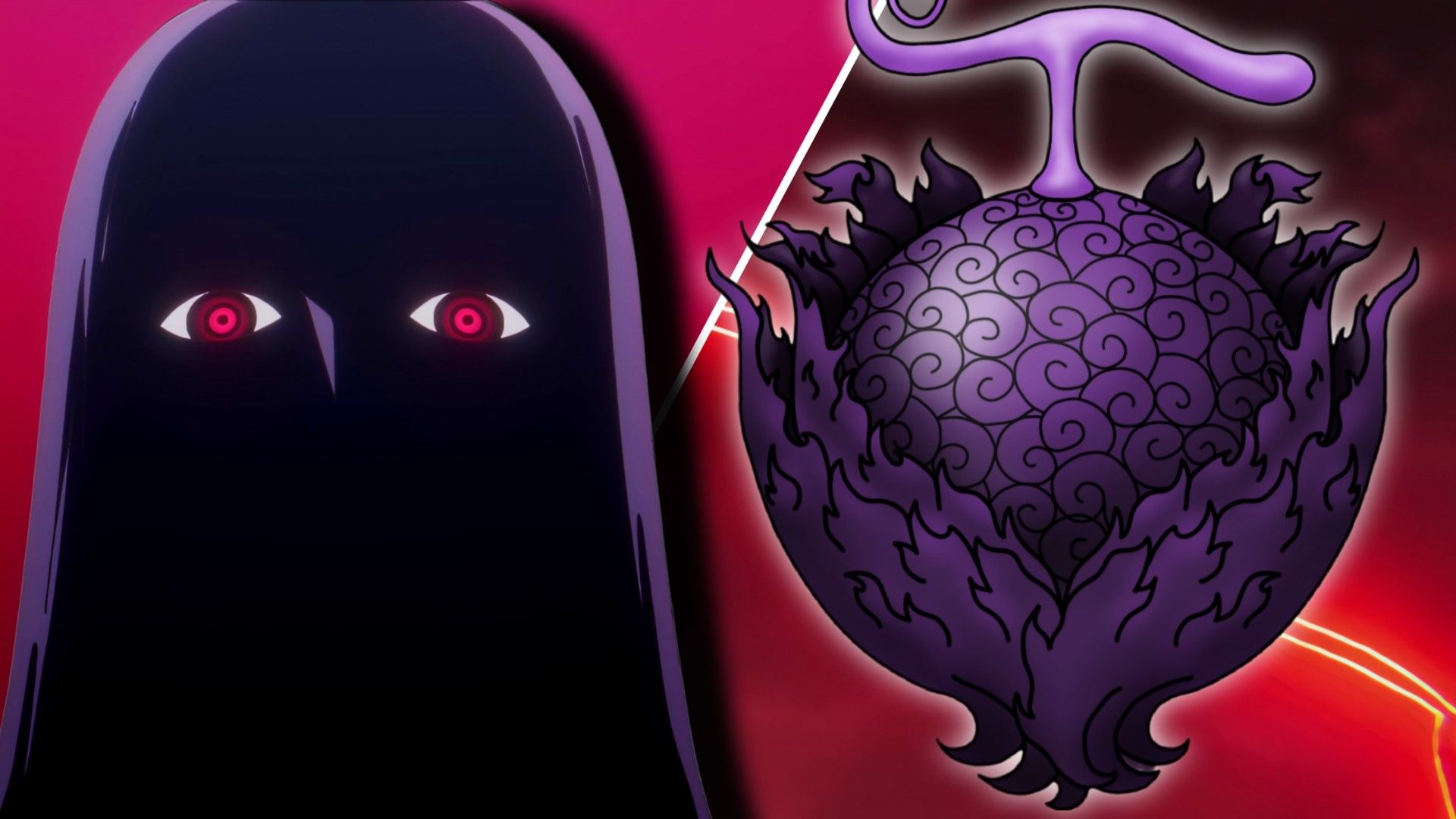
As a huge One Piece fan, I’m totally fascinated by Imu’s powers! It’s confirmed he has a Devil Fruit – an Akuma no Mi – but it’s unlike anything we’ve seen before. Usually, these fruits are written with specific kanji characters, but Imu’s fruit is written using katakana instead! That seemingly small detail is huge because it means Imu doesn’t have a regular Devil Fruit. He has something fundamentally different – essentially, ‘the Fruit of the Devil’ itself, and that’s what sets it apart from every other power in the series. It’s a game-changer!