Author: Denis Avetisyan
A new framework leverages decentralized learning and privacy-enhancing technologies to build more resilient intrusion detection systems.
PenTiDef combines differential privacy, latent space analysis, and blockchain coordination to mitigate poisoning attacks in federated learning-based intrusion detection.
While federated learning offers a promising path toward collaborative intrusion detection, its centralized nature introduces vulnerabilities and privacy concerns, particularly in decentralized environments. This paper introduces PenTiDef: Enhancing Privacy and Robustness in Decentralized Federated Intrusion Detection Systems against Poisoning Attacks, a novel framework designed to address these challenges through a combination of distributed differential privacy, latent space representation analysis for anomaly detection, and blockchain-based decentralized coordination. Experimental results demonstrate that PenTiDef effectively mitigates poisoning attacks and enhances privacy compared to existing defenses across diverse datasets. Could this approach pave the way for truly secure and privacy-preserving decentralized intrusion detection systems in increasingly adversarial networks?
The Expanding Attack Surface of Industrial Control Systems
The proliferation of Industrial Internet of Things (IIoT) devices, while driving unprecedented efficiency and automation, has simultaneously expanded the attack surface for malicious actors. Critical infrastructure, manufacturing plants, and supply chains are increasingly reliant on interconnected sensors, actuators, and control systems-all potential entry points for cyber threats. These attacks are no longer limited to simple malware; adversaries are employing sophisticated techniques like advanced persistent threats (APTs) and zero-day exploits to compromise these systems. Consequently, the need for robust intrusion detection systems (IDS) capable of identifying and mitigating these evolving threats is paramount. Traditional security measures, often designed for IT networks, prove inadequate against the unique challenges presented by IIoT-necessitating specialized solutions that can analyze network traffic, detect anomalies, and respond to incidents in real-time, safeguarding operational technology (OT) environments from disruption and potential catastrophe.
Conventional security architectures, designed for more contained networks, are proving inadequate for the expansive and diverse landscape of Industrial IoT deployments. These systems often rely on funneling data to a central security point, creating bottlenecks and single points of failure when dealing with the sheer volume of devices and data generated by modern industrial environments. Furthermore, the heterogeneity of IIoT – encompassing everything from legacy sensors to cutting-edge programmable logic controllers – introduces a complex web of communication protocols and operating systems. This diversity makes it exceptionally difficult to implement consistent security policies and maintain comprehensive visibility across the entire network, leaving substantial gaps that attackers are increasingly exploiting. The distributed nature of IIoT necessitates a shift towards decentralized, adaptive security solutions capable of addressing threats at the edge, before they can propagate and disrupt critical operations.
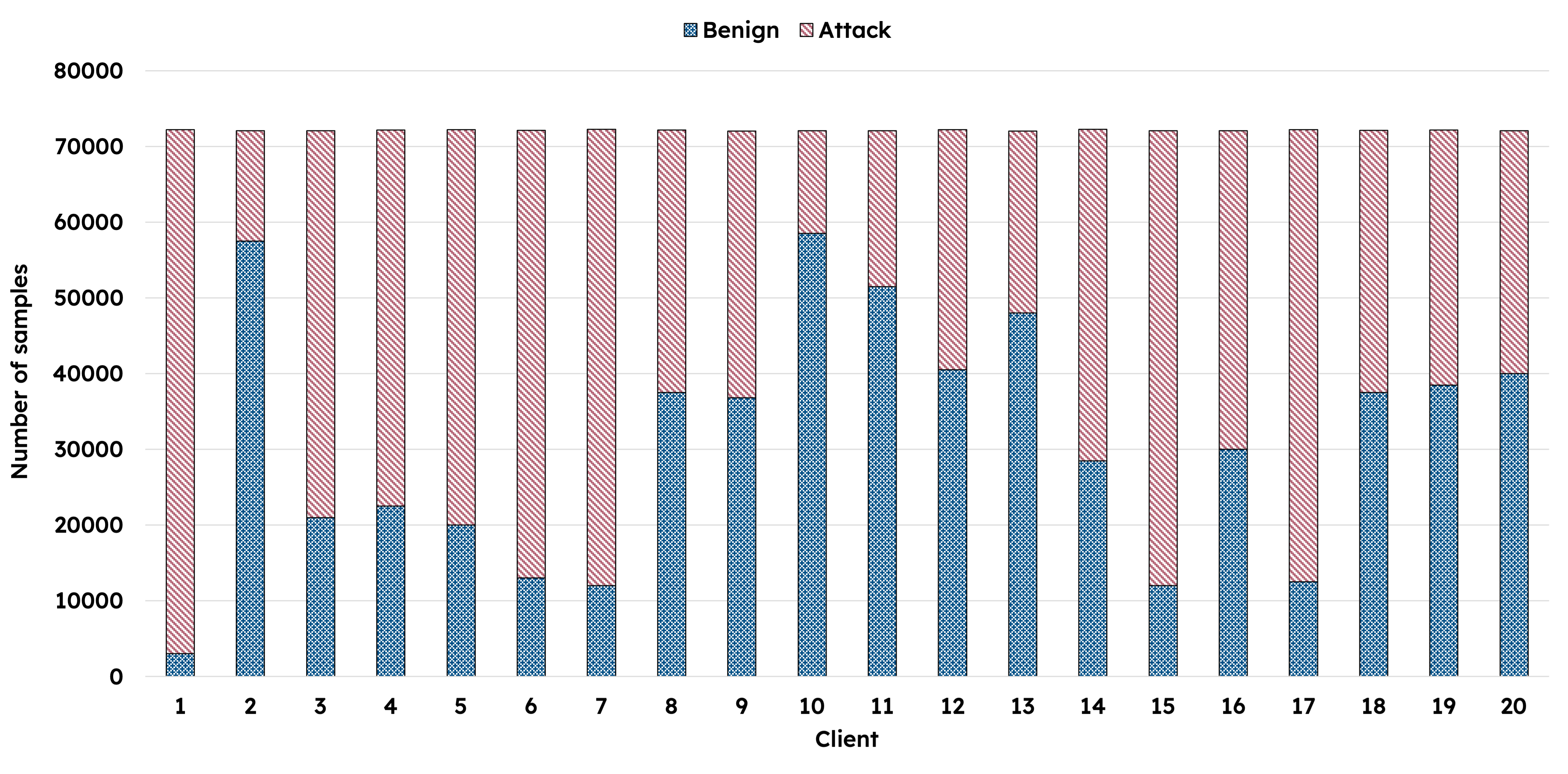
The distributed nature of Industrial IoT deployments introduces a significant hurdle for machine learning-based security systems: Non-Independent and Identically Distributed (Non-IID) data. Unlike traditional datasets where each data point is representative of the whole, IIoT sensors generate data heavily influenced by their specific environment and operational context. This means data from one sensor – or even a group of sensors in a single facility – can dramatically differ from data originating elsewhere, violating the fundamental assumptions of many machine learning algorithms. Consequently, models trained on centralized datasets often exhibit significantly reduced accuracy and fail to generalize effectively to the diverse data streams found at the network edge. Addressing this requires novel approaches to federated learning, transfer learning, or the development of algorithms inherently robust to data heterogeneity, ensuring reliable threat detection across the entire IIoT ecosystem.
Decentralized Federated Learning: A Principled Approach to Security
Decentralized Federated Learning (DFL) addresses the limitations of traditional intrusion detection systems by enabling collaborative model training across multiple edge devices or servers without requiring the exchange of raw data. In a typical DFL implementation for intrusion detection, each participating node trains a local model using its own isolated network traffic data. These locally trained models, rather than the data itself, are then aggregated – often using weighted averaging or more sophisticated algorithms – to create a global model. This global model benefits from the collective knowledge of all participating nodes while preserving the privacy of individual datasets, as sensitive information remains distributed and is never centrally stored. The distributed nature of DFL also increases system robustness by eliminating a single point of failure and reducing the risk of data breaches associated with centralized data storage.
Decentralized Federated Learning (DFL) utilizes blockchain technology to establish a secure and verifiable record of model updates contributed by participating nodes. Each update is treated as a transaction, cryptographically hashed, and added to a distributed, immutable ledger. This process ensures data integrity by making any unauthorized modification of updates readily detectable. Consensus mechanisms inherent in blockchain, such as Proof-of-Work or Proof-of-Stake, further validate updates before they are incorporated into the global model, mitigating the risk of malicious actors injecting faulty or biased information. The transparent and auditable nature of the blockchain provides a clear history of model evolution, enabling traceability and accountability in the learning process.
Differential privacy is implemented in federated learning through the addition of calibrated noise to model updates before they are shared. This noise, typically drawn from a Laplace or Gaussian distribution, obscures the contribution of individual data points, preventing adversaries from inferring information about specific training examples. The level of noise added is controlled by a privacy parameter, ε (epsilon), with lower values indicating stronger privacy guarantees but potentially impacting model accuracy. Techniques such as clipping gradients and limiting per-example sensitivity further refine the process, ensuring the added noise effectively masks individual contributions while maintaining the utility of the aggregated model. The goal is to provide provable privacy guarantees, preventing membership inference attacks and protecting sensitive data used in the training process.
PenTiDef: A Robust Defense Framework Against Data Poisoning
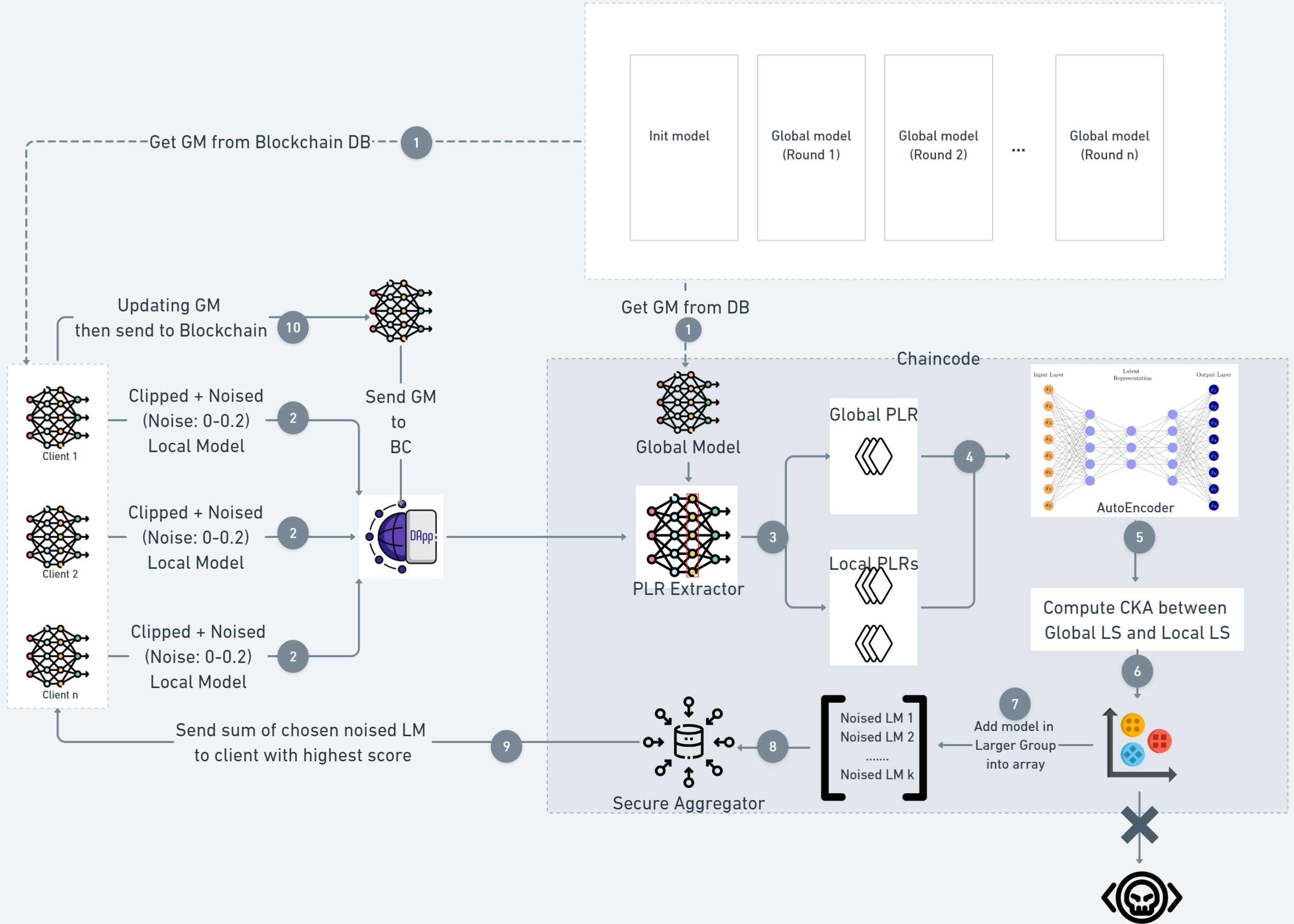
PenTiDef is a defense framework designed to mitigate the impact of poisoning attacks on intrusion detection systems. It achieves this by integrating Distributed Federated Learning (DFL) with supplementary techniques to enhance resilience. Poisoning attacks, in this context, involve malicious actors introducing crafted data into the training process to degrade the performance of the intrusion detection system. PenTiDef’s DFL component allows for collaborative model training across multiple edge devices, reducing reliance on a central vulnerable point. The framework then employs additional methodologies – including AutoEncoders, Centered Kernel Alignment, and a Hyperledger Fabric blockchain – to validate model updates and ensure the integrity of the globally shared intrusion detection model, thereby safeguarding against compromised performance resulting from malicious data injection.
PenTiDef employs AutoEncoder neural networks to create a compressed, lower-dimensional representation of input data known as the Latent Space Representation. This process facilitates improved anomaly detection by reducing the impact of noise and irrelevant features, while preserving essential characteristics. The AutoEncoder is trained to reconstruct the original input from this compressed representation; significant discrepancies between the input and reconstruction indicate anomalous data points. By analyzing data within this Latent Space, PenTiDef can effectively identify deviations from normal behavior, enhancing the accuracy and efficiency of intrusion detection compared to methods operating directly on raw data.
PenTiDef employs Centered Kernel Alignment (CKA) to quantify the similarity between locally updated intrusion detection models on edge devices and a globally aggregated model. CKA, a metric measuring the similarity of representations from different kernel functions, provides a statistically robust comparison, mitigating the influence of differing model architectures or training procedures. Specifically, PenTiDef calculates the CKA distance between the feature representations of benign and potentially poisoned model updates; a significant deviation from the expected similarity indicates a malicious attempt to compromise the global model, triggering a rejection of the suspect update. This allows the system to effectively identify and isolate adversarial contributions without relying on explicit knowledge of the attack strategy.
Hyperledger Fabric serves as the blockchain infrastructure for PenTiDef, facilitating secure and efficient coordination of edge devices during the collaborative defense process. This permissioned blockchain provides a distributed ledger for validating model updates and ensuring data integrity, preventing malicious actors from injecting compromised models. Fabric’s architecture, utilizing channels and private data collections, allows for selective sharing of information, minimizing communication overhead and maximizing privacy among participating nodes. Consensus mechanisms within Fabric guarantee the reliability and immutability of the shared model, while its modularity supports scalability to accommodate a growing number of edge devices and increasing data volumes. Transaction validation and smart contracts enforce pre-defined security policies and access controls, further strengthening the framework against adversarial manipulation.
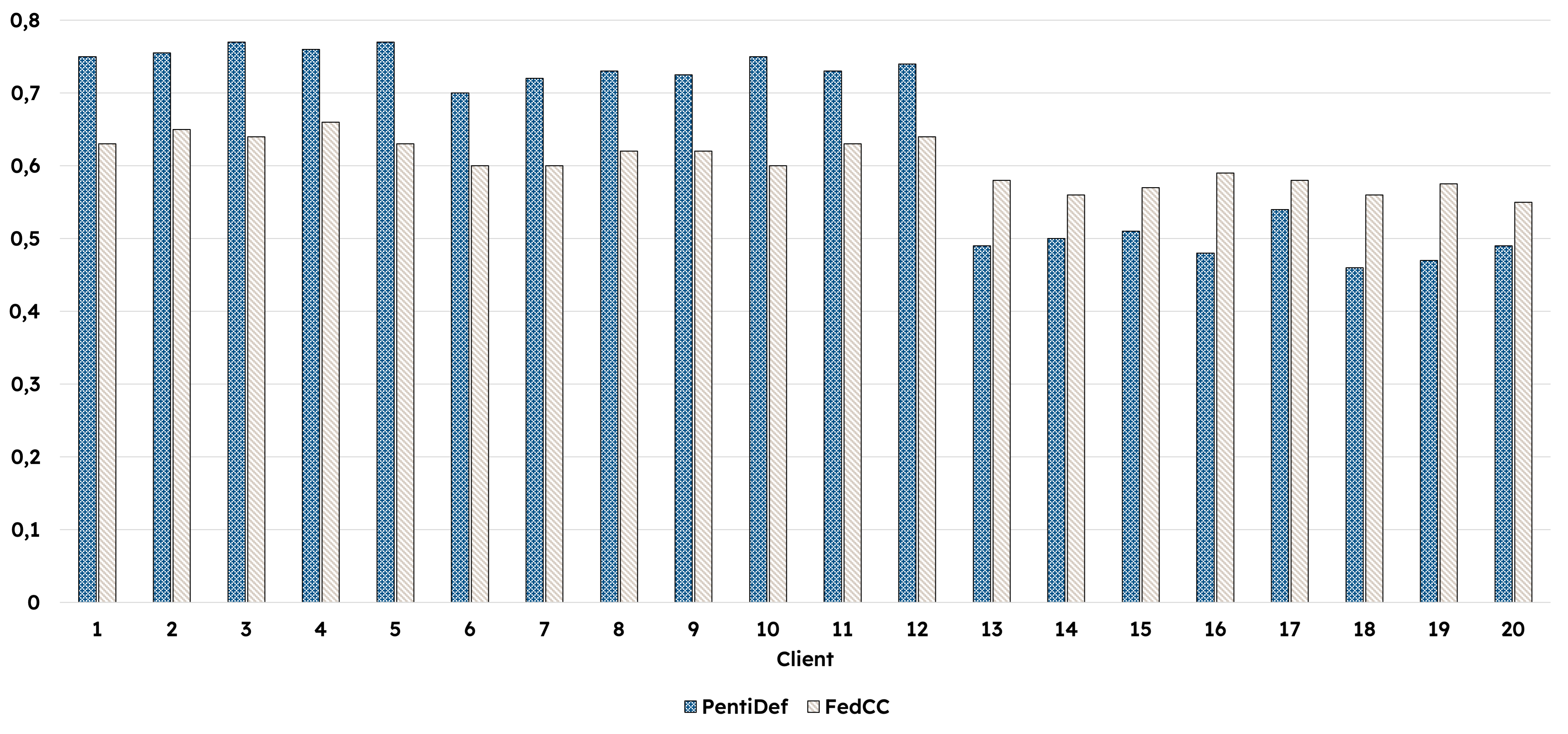
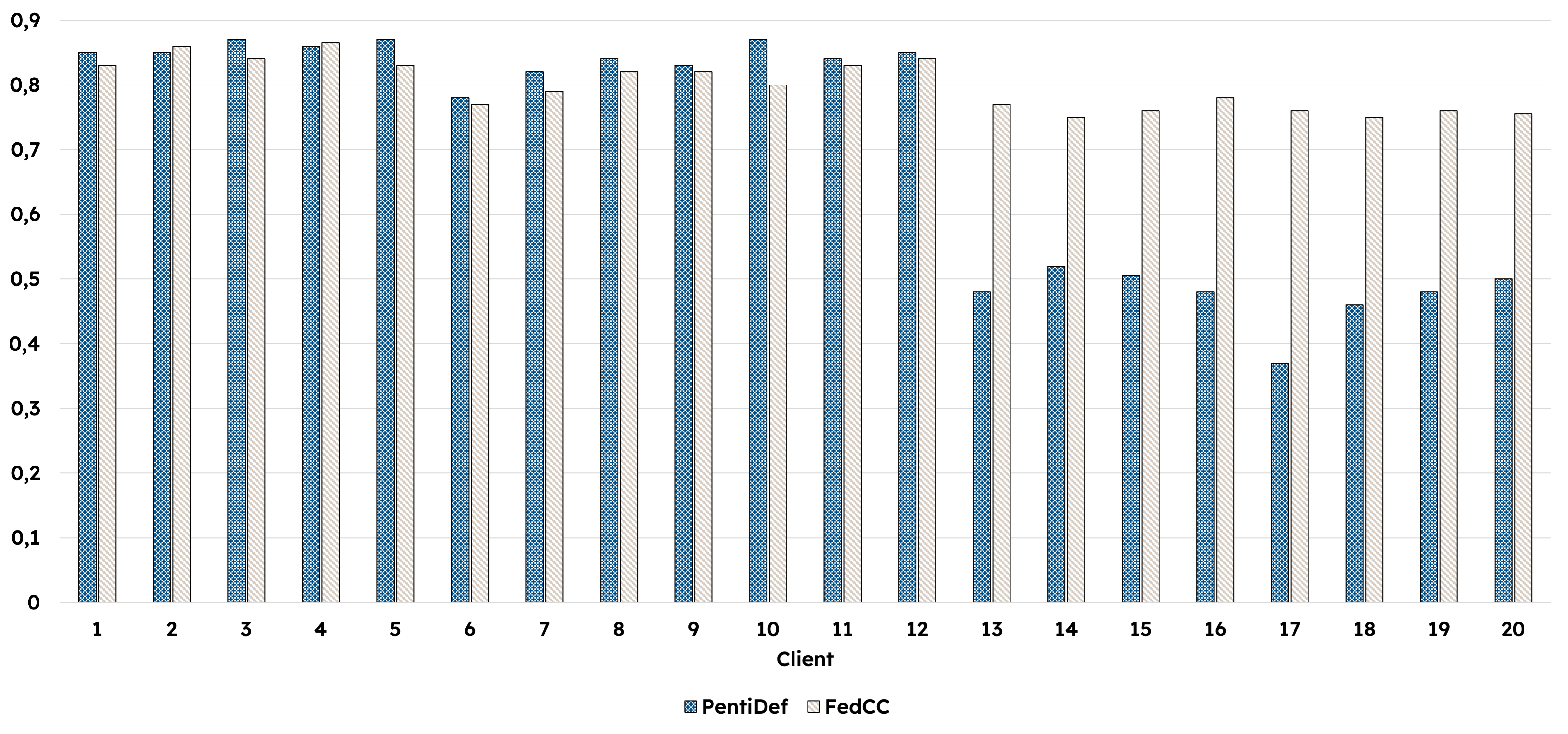
Validating PenTiDef and Charting a Course for Future Research
Rigorous experimentation reveals PenTiDef to be a substantial advancement in defending against data poisoning attacks, consistently exceeding the performance of established defenses like FLARE and FedCC. Across a diverse range of simulated attack scenarios, PenTiDef achieves an impressive accuracy rate of up to 92% in both detecting and mitigating malicious data injections. This heightened accuracy stems from the framework’s novel approach to anomaly detection and robust aggregation techniques, effectively isolating and neutralizing the impact of compromised data points before they can corrupt the learning process. The results demonstrate a significant improvement in model integrity and reliability, offering a more secure foundation for federated learning systems vulnerable to adversarial manipulation.
Rigorous testing of the PenTiDef framework across established benchmark datasets-specifically, the ‘CIC-IDS2018’ and ‘Edge-IIoTSet’ collections-provides compelling evidence of its robust performance and adaptability. The ‘CIC-IDS2018’ dataset, known for its comprehensive range of network intrusion scenarios, allowed for evaluation against diverse attack vectors, while ‘Edge-IIoTSet’, representing data from Internet of Things devices, confirmed the framework’s efficacy in resource-constrained environments. Consistent results across these disparate datasets demonstrate that PenTiDef isn’t simply tuned to a specific threat model, but rather possesses a generalized ability to identify and mitigate poisoning attacks, making it a versatile solution for a wide range of deployments and security concerns.
The PenTiDef framework prioritizes data security by seamlessly integrating privacy-preserving techniques throughout the federated learning process. This design choice moves beyond mere performance gains, actively safeguarding sensitive information contributed by participating entities. Through methods like differential privacy and secure aggregation, the framework ensures that individual data points are not directly exposed, minimizing the risk of data breaches and unauthorized access. This commitment to privacy not only fosters greater trust among stakeholders but also facilitates compliance with increasingly stringent data protection regulations, such as GDPR and CCPA, thereby paving the way for wider adoption of secure and collaborative machine learning systems.
Evaluations reveal that PenTiDef not only fortifies defenses against data poisoning but also enhances system performance. Comparative analyses demonstrate a significant reduction in training times when contrasted with established defense mechanisms like FLARE and FedCC, suggesting improved computational efficiency and scalability. Crucially, this efficiency extends to practical blockchain implementations; PenTiDef consistently maintained stable transaction throughput when integrated with Hyperledger Fabric, even under escalating workloads. This resilience indicates that the framework can effectively safeguard federated learning systems without compromising operational speed or reliability, making it a viable solution for resource-constrained environments and high-demand applications.
A critical component of PenTiDef’s success lies in its Capacity Kernel Alignment (CKA) score, which provides a robust mechanism for discerning between legitimate and compromised machine learning models. Evaluations revealed a clear threshold – models exhibiting a CKA score of 0.8 or higher were consistently identified as benign, while those falling below 0.6 were reliably flagged as malicious, even when attackers comprised 40% of the participating nodes. This precise differentiation underscores PenTiDef’s anomaly detection capabilities, allowing the system to proactively identify and isolate adversarial contributions before they can significantly impact the integrity of the federated learning process and the overall system’s trustworthiness. The CKA score, therefore, serves not merely as a metric, but as a dynamic gatekeeper, safeguarding the collaborative learning environment against subtle and sophisticated poisoning attacks.
The pursuit of a robust intrusion detection system, as detailed in this study, mirrors a fundamental tenet of computational elegance. The PenTiDef framework, by integrating differential privacy and blockchain coordination, attempts to establish verifiable boundaries against malicious interference – a system where correctness can be demonstrated, not merely observed through testing. This echoes Edsger W. Dijkstra’s assertion: “It’s not enough to show that something works; you must prove why it works.” The framework’s focus on latent space representation and anomaly detection isn’t simply about identifying threats, but about creating a provably secure system, aligning with the principle that a solution’s value lies in its demonstrable truth, not empirical success.
What’s Next?
The presented framework, while a step towards a demonstrably secure federated intrusion detection, merely addresses symptoms. The fundamental problem remains: trust. PenTiDef minimizes damage from malicious participants, but does not eliminate the need for initial, and ongoing, verification of model contributions. Future work must move beyond defensive layering and consider formal methods for proving the integrity of latent space representations, or ideally, constructing systems where malicious data is mathematically impossible, not simply statistically improbable.
A troubling redundancy exists within the combined approach. Differential privacy, blockchain consensus, and anomaly detection all attempt to solve the same underlying issue – untrusted data. The elegance of a truly minimal solution demands a unified mathematical principle, not a collection of heuristics. Further research should focus on distilling these separate defenses into a single, provable guarantee. The current architecture feels, regrettably, like building a fortress around a vulnerability that could be elegantly avoided with a different foundation.
Ultimately, the field must acknowledge that “robustness against poisoning” is not a final state. It is an ongoing arms race. The true measure of success will not be the complexity of the defenses, but the simplicity and provability of the underlying system. Until then, each added layer of security introduces further opportunities for abstraction leaks and subtle, yet critical, failures.
Original article: https://arxiv.org/pdf/2602.17973.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- All Skyblazer Armor Locations in Crimson Desert
- Robinhood’s $75M OpenAI Bet: Retail Access or Legal Minefield?
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- How to Catch All Itzaland Bugs in Infinity Nikki
- Speedsters Sandbox Roblox Codes
- Jojo’s Bizarre Adventure Ties Frieren As MyAnimeList’s New #1 Anime
- Invincible: 10 Strongest Viltrumites in Season 4, Ranked
- Top 10 Must-Watch Isekai Anime on Crunchyroll Revealed!
- Who Can You Romance In GreedFall 2: The Dying World?
- Top 8 UFC 5 Perks Every Fighter Should Use
2026-02-24 05:43