Author: Denis Avetisyan
A novel system proposes empowering patients with greater control over their electronic health records through decentralized technology.
This review details a blockchain and IPFS-based architecture for secure, interoperable access control and data sharing of Electronic Health Records.
Despite increasing digitization in healthcare, maintaining both the security and interoperability of electronic health records (EHRs) remains a significant challenge. This paper, ‘A Secure and Interoperable Architecture for Electronic Health Record Access Control and Sharing’, proposes a novel architecture leveraging blockchain and Interplanetary File System (IPFS) technologies to address these concerns. By implementing patient-centric access control via smart contracts on a private blockchain, the system empowers individuals while ensuring data integrity and compliance with regulations like GDPR. Could this decentralized approach represent a viable path towards more secure, patient-controlled, and seamlessly shared healthcare data ecosystems?
Architecting Trust: Addressing the Core Challenges of Health Data Management
Existing Electronic Health Record (EHR) systems, while intended to revolutionize healthcare, currently present significant vulnerabilities that impede both patient care and vital medical research. These systems, often relying on centralized databases, are increasingly targeted by cyberattacks, exposing sensitive patient information and disrupting healthcare operations. Beyond security concerns, a lack of interoperability – the ability of different EHR systems to seamlessly exchange data – creates fragmented patient records. This fragmentation forces clinicians to spend valuable time compiling information from multiple sources, potentially leading to diagnostic errors and delayed treatments. Consequently, researchers face substantial hurdles in accessing comprehensive datasets needed to identify trends, develop new therapies, and improve public health outcomes, highlighting the urgent need for more secure and connected health data infrastructure.
The architecture of conventional healthcare data storage presents a dual challenge. Centralized databases, while aiming for streamlined access, create single points of failure increasingly targeted by cyberattacks, potentially exposing sensitive patient information on a massive scale. Simultaneously, the prevalent fragmentation of health records across disparate hospital systems, clinics, and specialist offices actively hinders the flow of crucial data. This lack of interoperability doesn’t simply create administrative burdens; it obstructs a holistic understanding of a patient’s medical history, impeding accurate diagnoses, effective treatment plans, and the advancement of medical research reliant on comprehensive datasets. The result is a system where both security and the potential for insightful analysis are compromised, necessitating innovative approaches to data management.
The limitations of current health data systems necessitate a fundamental rethinking of how patient information is stored and accessed. Existing centralized databases, while intended to streamline care, present single points of failure vulnerable to increasingly sophisticated cyberattacks and data breaches. Simultaneously, the fragmented nature of many healthcare networks hinders the seamless exchange of vital patient data, impeding comprehensive diagnoses and effective treatment plans. Consequently, a shift towards decentralized solutions, potentially leveraging technologies like blockchain, is gaining traction. These approaches aim to distribute data control, enhance security through cryptographic methods, and empower patients with greater agency over their own health records – fostering a more robust, resilient, and patient-centric healthcare ecosystem that prioritizes both data integrity and accessibility.
Establishing a Foundation of Trust: A Decentralized Architecture
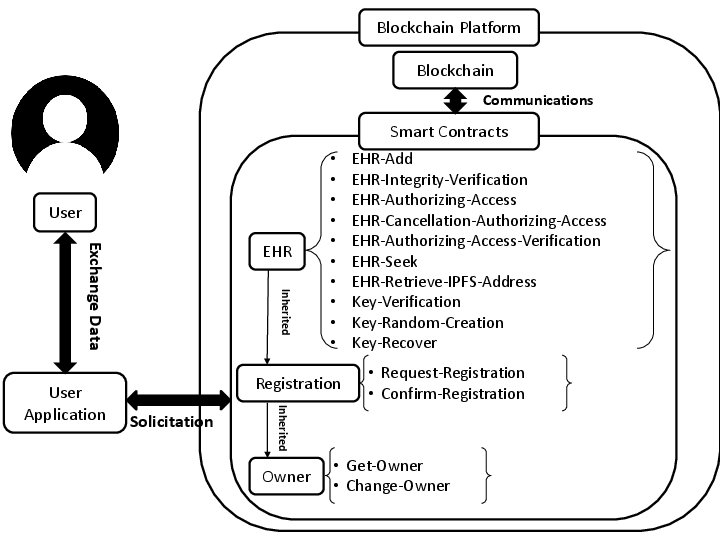
The system utilizes Blockchain Technology, specifically a Private Blockchain, to establish a secure and transparent record of Electronic Health Records (EHRs). This implementation creates an immutable ledger, meaning once data is recorded, it cannot be altered or deleted, ensuring data integrity. All transactions and data access events are cryptographically linked and time-stamped, providing a complete and verifiable audit trail. The private nature of the blockchain restricts participation to authorized members of a healthcare consortium, maintaining patient privacy and adhering to regulatory requirements such as HIPAA. This contrasts with public blockchains, offering enhanced control and scalability for managing sensitive health information.
Smart contracts within the system function as self-executing agreements defining access privileges to Electronic Health Records (EHRs). These contracts, deployed on the private blockchain, specify conditions under which data can be accessed, verifying the requesting party’s authorization against pre-defined roles and permissions. Access control is implemented at the data element level; specific fields within an EHR can be restricted to particular users or groups. This granular approach ensures compliance with regulations like HIPAA by limiting data exposure and providing a verifiable audit trail of all access attempts. The automated enforcement minimizes the risk of unauthorized access and simplifies the process of demonstrating adherence to privacy policies.
Hyperledger Fabric facilitates a permissioned blockchain network, crucial for healthcare data sharing due to its requirement for identified and authorized participants. This framework enables the creation of a consortium where multiple healthcare providers can collaboratively manage and access Electronic Health Records (EHRs) while maintaining control over data visibility. Scalability is achieved through Fabric’s modular architecture, allowing for the addition of nodes and transaction processing capacity as the network grows. Channel architecture within Hyperledger Fabric further enhances scalability and privacy by enabling subsets of the consortium to conduct transactions privately, limiting data exposure to only relevant parties. The platform’s pluggable consensus mechanism allows healthcare organizations to select a consensus protocol optimized for their specific performance and security requirements, avoiding the resource intensity of public blockchain consensus algorithms.
Bridging the Gap: A Hybrid Approach to Data Storage and Integrity
To manage the substantial data volume and associated costs of Electronic Health Records (EHR), our system employs a hybrid storage architecture. The majority of EHR data, including patient records and medical imaging, is stored on the InterPlanetary File System (IPFS), a decentralized storage network. Blockchain technology is then utilized to store only critical metadata pertaining to the EHR data, specifically cryptographic hashes that uniquely identify each data block stored on IPFS. This approach minimizes blockchain storage requirements and transaction costs while leveraging IPFS for scalable and cost-effective data retention. The hashes stored on the blockchain serve as immutable fingerprints, enabling verification of data integrity and authenticity without requiring the entire EHR to reside on the blockchain.
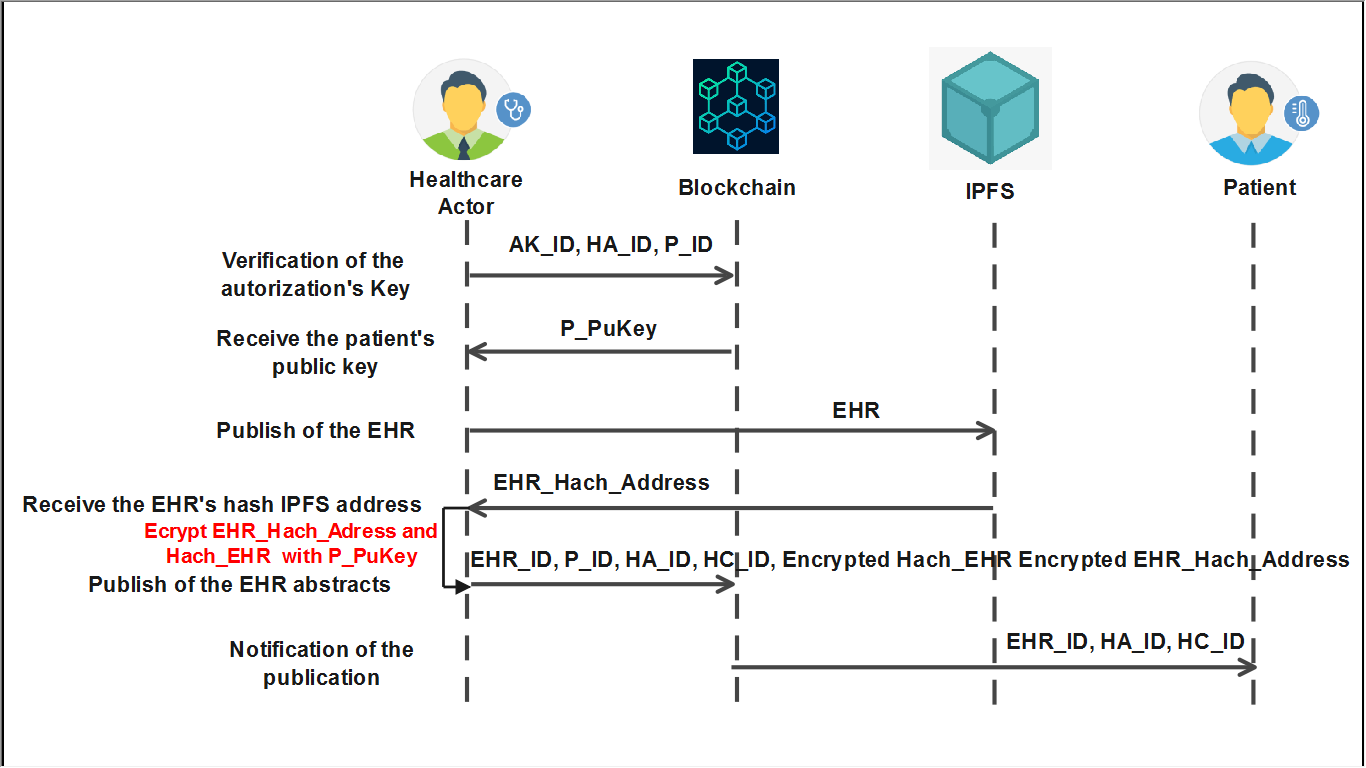
The EHR Publishing Protocol facilitates secure data transmission to the InterPlanetary File System (IPFS) through established cryptographic channels. Upon successful publication, the protocol generates a unique cryptographic hash of the data stored on IPFS. This hash, representing a digital fingerprint of the data, is then recorded on the blockchain via the EHR Integrity Verification Protocol. Subsequent verification of data authenticity involves retrieving the data from IPFS, recalculating its hash, and comparing it to the hash recorded on the blockchain; a match confirms data integrity and verifies the data has not been tampered with since its initial publication.
The system architecture leverages a hybrid approach to data storage and verification. Large electronic health record (EHR) datasets are stored off-chain using the InterPlanetary File System (IPFS) to address scalability and cost limitations associated with on-chain storage. Simultaneously, critical metadata and cryptographic hashes of the EHR data are immutably stored on a blockchain, ensuring data integrity and authenticity. Experimental validation has confirmed the stability of this architecture; performance metrics remained consistent even with increasing blockchain ledger size and transaction load, demonstrating the system’s ability to scale without compromising data verification capabilities.
Governing Access and Ensuring Responsible Data Use: A Holistic Approach
The foundation of secure health information exchange rests upon a robust user authentication and authorization system, embodied by the EHR Registration Protocol. This protocol meticulously verifies the identities of all system users – clinicians, researchers, and administrative personnel – through multi-factor authentication techniques, establishing a definitive link between an individual and their digital credentials. Beyond simple identification, the protocol defines granular permission levels, dictating precisely what data each user can access, modify, or share, and under what circumstances. This tiered access control isn’t merely preventative; it creates an auditable trail of data interactions, crucial for maintaining regulatory compliance and fostering trust within the network. By proactively validating user identities and enforcing strict access controls, the EHR Registration Protocol minimizes the risk of unauthorized data breaches and ensures the confidentiality, integrity, and availability of sensitive patient information.
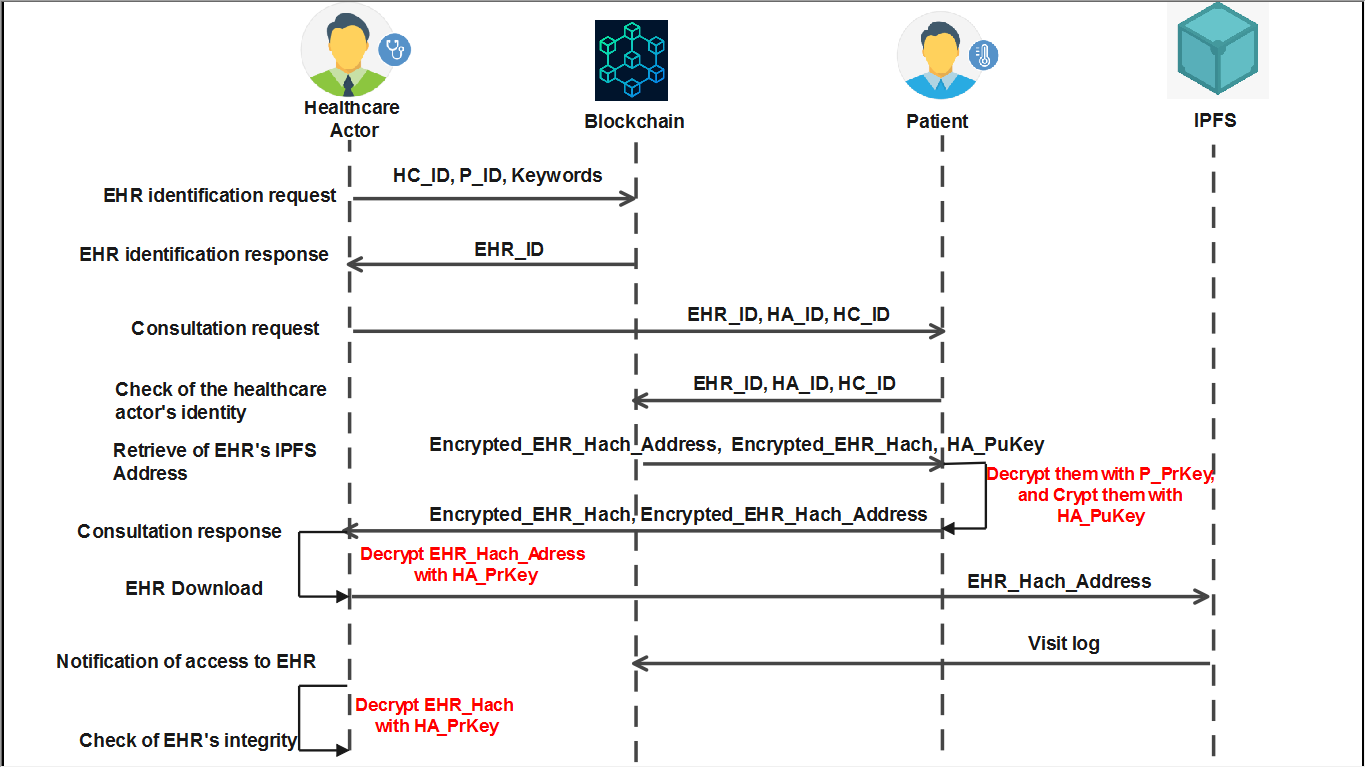
Beyond foundational access control, the system incorporates specialized protocols tailored to distinct data utilization scenarios. The Medical Emergency Protocol prioritizes rapid information access for critical care, overriding standard permissions when immediate patient safety is at risk. Simultaneously, the Investigation Protocol facilitates secure data release to authorized law enforcement agencies, adhering to legal mandates and maintaining a comprehensive audit trail. Crucially, the Research and Data Exploitation Protocol governs the sharing of anonymized or pseudonymized patient data for scientific inquiry, ensuring compliance with ethical guidelines and regulations while enabling valuable advancements in healthcare. These extensions to the core EHR Accessing Protocol demonstrate a nuanced approach to data governance, balancing the need for secure confidentiality with the imperative to support diverse and vital applications.
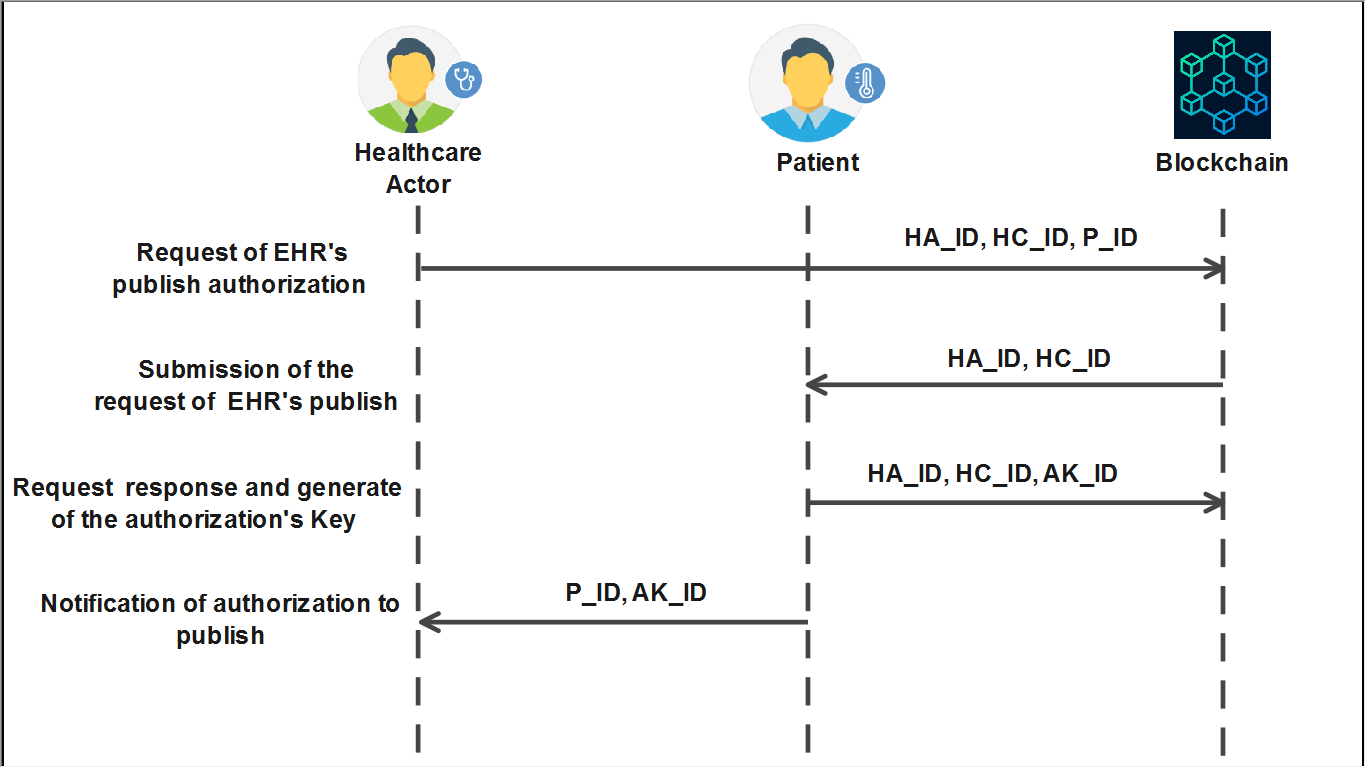
The system’s EHR Publication Authorization Protocol leverages smart contracts to rigorously enforce data sharing policies, ensuring compliance with regulations such as the General Data Protection Regulation. Performance testing demonstrates a robust capacity for handling data requests; the system consistently achieves up to 600 read transactions per second with a 5-second timeout, alongside 45 write transactions per second with a 30-second timeout. Notably, read transaction latencies remain remarkably stable, fluctuating between 0.01 and 0.03 seconds, while write transaction latencies consistently fall between 1.1 and 1.2 seconds – these figures are maintained irrespective of the overall ledger size. System resource utilization remains efficient; RAM consumption exhibits stability under varying loads, ranging from 1332.1 to 1431.6 MB, indicating a scalable and reliable foundation for secure data exchange.

The architecture detailed within prioritizes a holistic approach to data management, recognizing that vulnerabilities often reside not within isolated components, but at the interfaces between them. This resonates with Donald Knuth’s observation: “Premature optimization is the root of all evil.” The proposed system, by focusing on interoperability and decentralized control via blockchain and IPFS, avoids the trap of optimizing individual access points without considering the larger data flow. Such an approach, much like a carefully designed organism, anticipates weaknesses inherent in complex interactions, striving for a robust and resilient system where data integrity and patient control are paramount. The focus on a unified structure, mirroring Knuth’s emphasis on fundamental principles, strengthens the entire framework.
Future Directions
The architecture presented here, while addressing critical issues of data control and interoperability, merely shifts the complexity, rather than resolving it. Blockchain, for all its promise, introduces its own dependencies – consensus mechanisms, oracle problems, and the persistent challenge of scalability. The true test will not be in demonstrating secure record storage, but in proving secure and efficient access under realistic load – a scenario often glossed over in idealized models. Documentation captures structure, but behavior emerges through interaction.
Further exploration should prioritize the pragmatic limitations of decentralized systems within existing healthcare infrastructures. Integration with legacy systems, regulatory compliance – particularly concerning data residency and right to be forgotten – and the human factors surrounding patient adoption are not merely ‘implementation details’. They are the system. A focus on minimal viable complexity, prioritizing genuine patient agency over technological novelty, would be a welcome departure.
Ultimately, the success of such an architecture hinges not on the elegance of the underlying technology, but on its ability to fade into the background, seamlessly supporting – rather than dictating – the delivery of care. The aim should be a system that anticipates failure modes, and gracefully degrades, rather than one that promises invulnerability.
Original article: https://arxiv.org/pdf/2602.20830.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- Robinhood’s $75M OpenAI Bet: Retail Access or Legal Minefield?
- All Skyblazer Armor Locations in Crimson Desert
- How to Get the Sunset Reed Armor Set and Hollow Visage Sword in Crimson Desert
- How to Catch All Itzaland Bugs in Infinity Nikki
- Speedsters Sandbox Roblox Codes
- Black Sun Shield Location In Crimson Desert (Buried Treasure Quest)
- Top 10 Must-Watch Isekai Anime on Crunchyroll Revealed!
- Who Can You Romance In GreedFall 2: The Dying World?
- Invincible: 10 Strongest Viltrumites in Season 4, Ranked
- USD CNY PREDICTION
2026-02-25 13:47