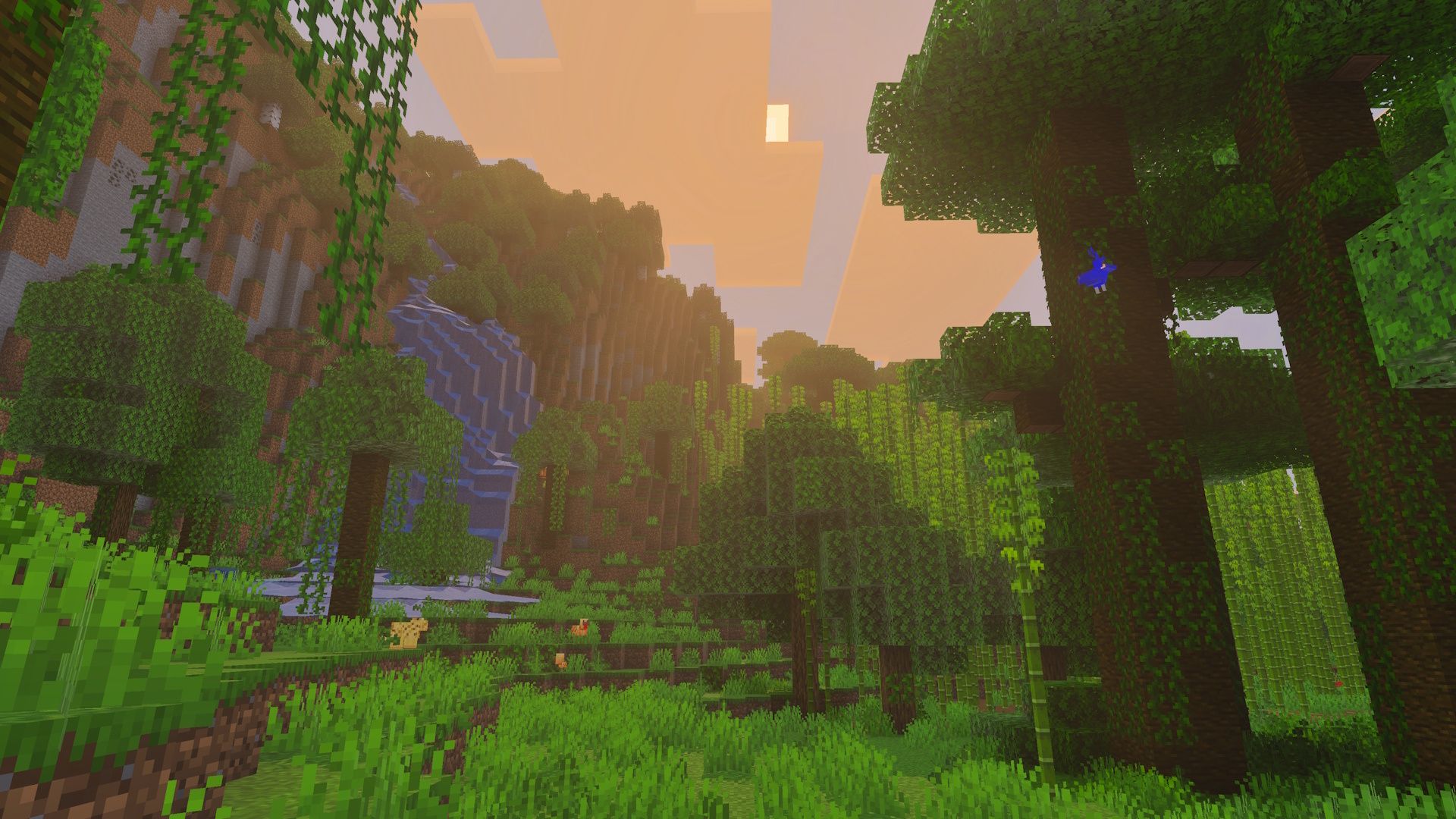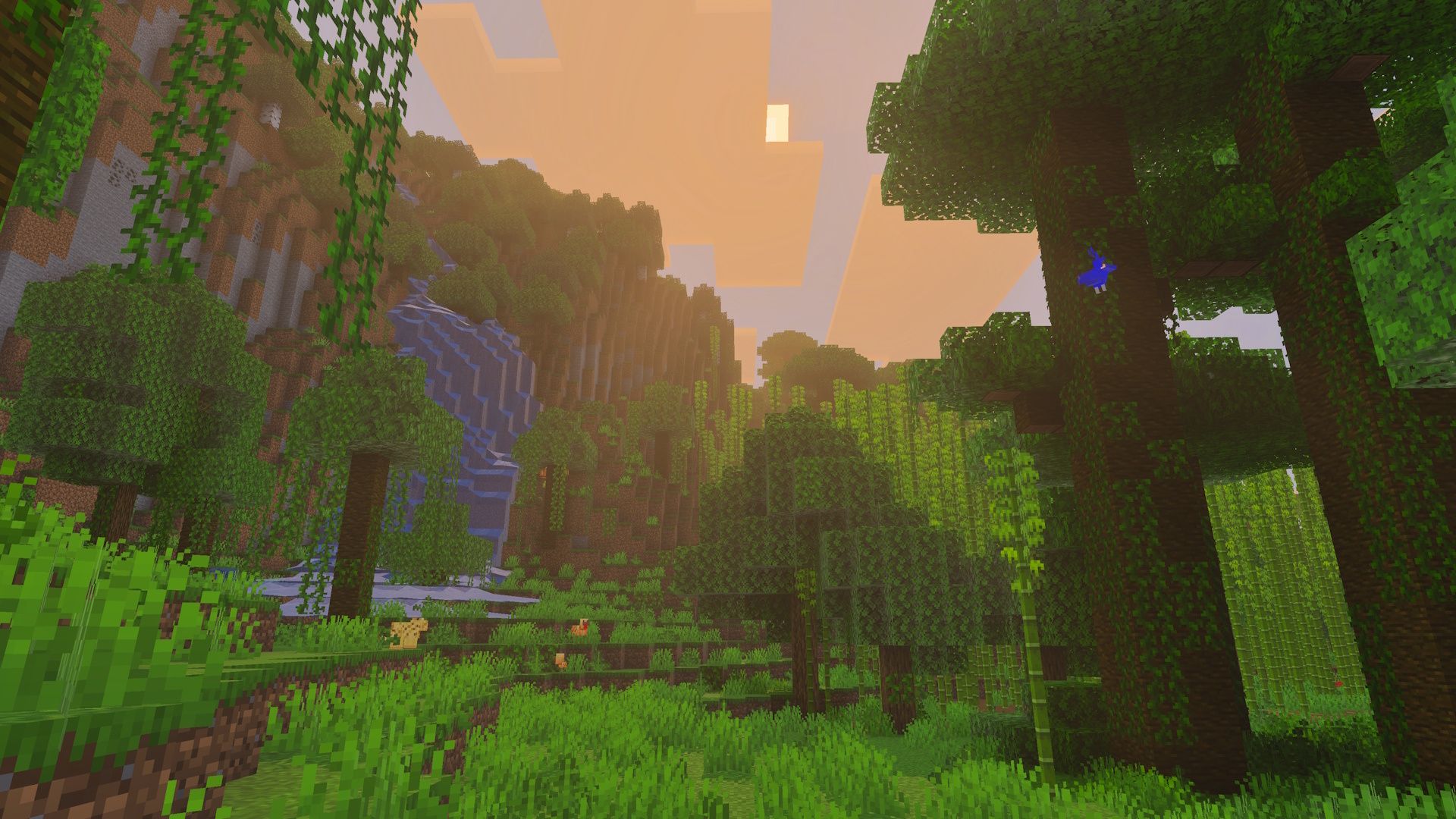
During the recent Minecraft Live event, Mojang unveiled the Dappled Forest, a brand-new biome for Minecraft. This area will be characterized by warm, orange hues and will contain the remnants of an old campsite for players to find. The Dappled Forest will also introduce unique poplar trees with brown and orange leaves, as well as new red shrubs. In addition, Warner Bros. surprised viewers with a teaser for a sequel to The Minecraft Movie, revealing the title to be The Minecraft Movie: Squared. Players can expect to explore these new forests in the third major update of the year, planned for release around the third quarter of 2026.